Data is one of the most valuable commodities in the world right now.
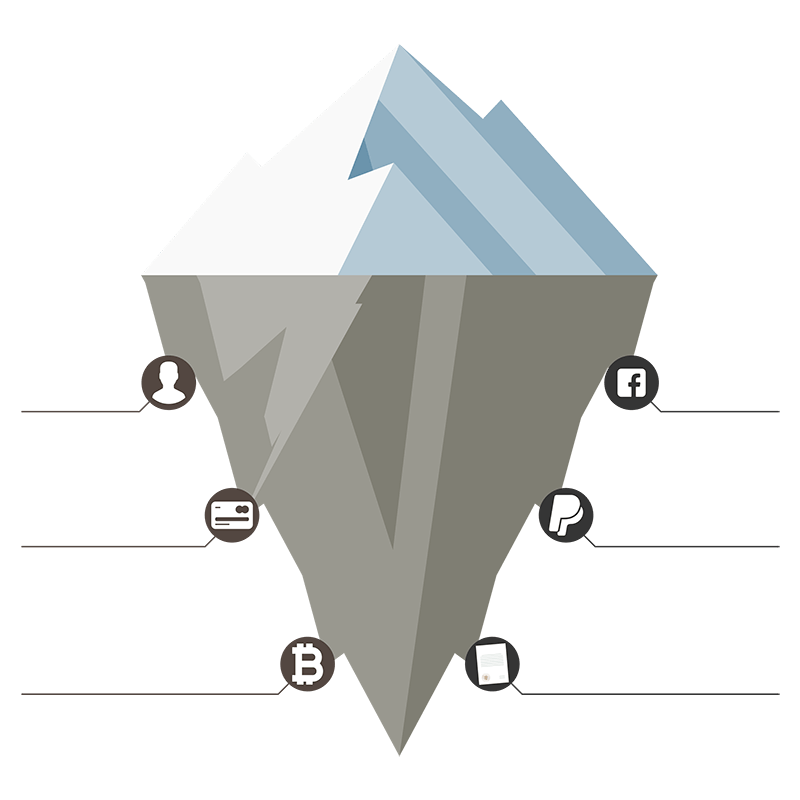
Companies such as Facebook and Google track you to sell highly personalized advertising space to the highest bidder. They know who your friends are, what you’re interested in, how likely you are to watch a certain video, your political leanings, and even which websites you visit.
Governments watch your every move by passing laws to force ISPs to provide information on every character you type into a search engine and every webpage you visit. They know your location at any time through triangulation of your mobile phone and can follow you using huge networks of CCTV cameras.
They even constantly try to undermine the safety that protects us from having our data wide visible to anyone who looks – strong encryption.
Hackers and cybercriminals are constantly looking for vulnerable systems companies use to store users’ data and use sophisticated social engineering attacks to trick people into handing their data over willingly.
Major data breaches happen at an alarming rate and continue to increase in frequency. A US computer is targeted in a hacking attempt every 25 seconds, and the cost of cybercrime on the global economy is set to reach $6 Trillion in 2021.
The consequences can be profound when your data falls into the wrong hands. This happens, ranging from changing your passwords, having your emails published, and your website memberships becoming public knowledge to being denied credit in the future because someone has used your name to take out a loan.
Privacy Affairs is an information provider and content creator dedicated to helping you understand how to protect your private data and ensure you don’t find yourself on the wrong side of a data breach or cyber attack.
We report important news, research vulnerable consumer and professional technologies, and provide information on how to keep your info safe from rogue companies, prying governments, cybercriminals, and anyone else who would do you harm by stealing or otherwise intercepting your data.
 Miklos Zoltan
Miklos Zoltan

 Bogdan Pătru
Bogdan Pătru Alex Popa
Alex Popa