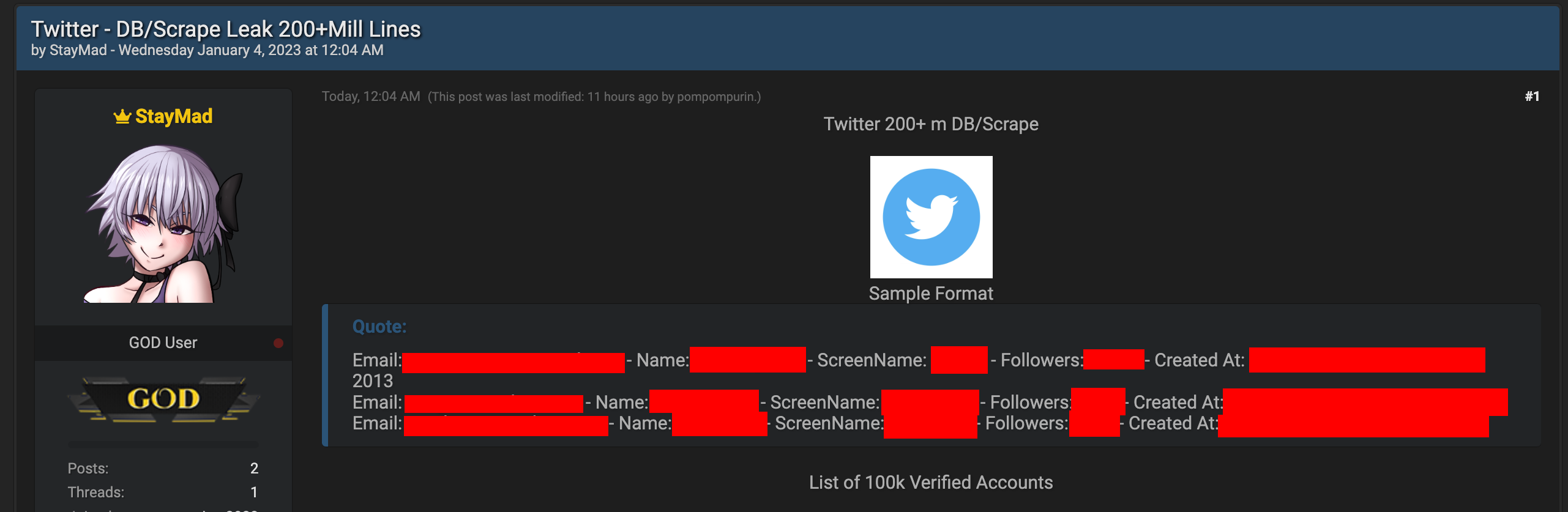
Account Details of Over 200 Million Twitter Users Leaked on Hacker Forum
Today, on a popular hacker forum, data of over 200 million Twitter users was leaked for anyone to download. The hackers claim to have obtained this data through scraping.
- Personal details of over 200 million Twitter accounts were leaked on a hacker forum
- Leaked data includes account name, handle, creation date, follower count, and email address
- Leaked data could be used for social engineering or doxxing campaigns
- Leaked data could be used to hack Twitter users’ accounts
Twitter seems to have experienced another data leak on January 4, when a user on a known hacker forum released a database containing scraped information on over 200 million Twitter users.
The database uploaded to the forum is of 63 GB. It contains information on over 200 million accounts, such as screen name, full name, follower number, date of creation, and most importantly, the registered email address.
Some popular and known names and entities in the leak include:
- Sundar Pichai
- Donald Trump Jr.
- SpaceX
- CBS Media
- NBA
- Social Media of WHO
The full dataset is freely available for anyone to download.
Update: This new leak appears to be the same as the one reported in December 2022 that affected over 400 million accounts.
The 200 million number in this case resulted from the removal of duplicates.
However, this time, the data is available for anyone to download for free, instead of being listed for sale at $200,000, as it was in December.
Privacy Affairs cybersecurity experts reviewed the published data and believe this latest leak could lead to social engineering attacks and doxxing.
The availability of the email addresses associated with the listed accounts could be used to determine the real-life identity or location of the affected account holders through social engineering attacks.
The email addresses could also be used for spam or scam marketing campaigns and for sending personal threats to individual users.
Privacy Affairs analysts determined that phone numbers were not disclosed in this leak.
This newest leak follows another leak in December 2022 when cybercriminals released data from over 400 million Twitter accounts.
However, at that time, the data was not released for free to the general public and was listed for sale for $200,000.
As such, even if that leak was bigger in scale, this new one could be considered more severe, as now many more bad actors can obtain this data.
It is not certain at this moment how exactly this data was obtained. The most likely method used could have been the abuse of an application programming interface (API) vulnerability.
How to protect yourself
Privacy Affairs always recommends using different passwords for every website or app online. If your Twitter password currently uses the same password as any other website or app, it’s recommended to change it immediately.
While not a very popular method at the moment, it would also be useful to use “burner” email addresses or separate email addresses for online accounts while forwarding emails to a master address.
This way, even if the email address associated with a Twitter or any other account is leaked, it can’t be associated with the end-user’s identity or other online services.
Our Mission
We believe security online security matters, and it's our mission to make it a safer place.

