3AM Ransomware Targets Two US Companies
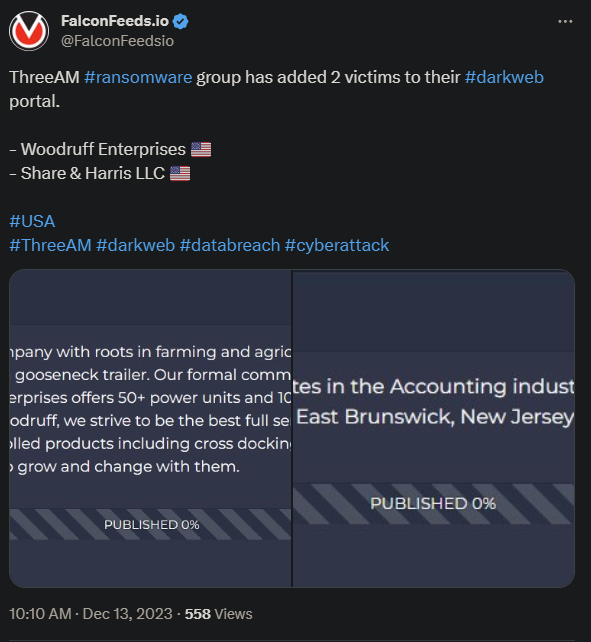
The novel 3AM ransomware targets two more companies on US soil. The victims are Woodruff Enterprises, a farming and agriculture company, and Share & Harris LLC, an accounting company.
- The attacks were swift, caught the victims by surprise, and resulted in the encryption and cloning of important internal data
- The 3AM group secured the assets and informed the victims that the info will be leaked publicly, should they refuse to pay the ransom
- 3AM has been on a wave lately, performing several high-profile attacks on privately-owned businesses
- Some of the attacks were unsuccessful in the sense that the victims refused to pay
The cyberthreat actor is a newcomer in the ransomware field, as the group only took responsibility for several attacks. The first instance where 3AM was used was during a failed LockBit attack.
In that specific case, the LockBit attack was unsuccessful, so the attackers used 3AM as a backup plan. The second wave was successful, which is what can explain why 3AM was now used as the first hacking tool, instead of a plan B.
The reason why 3AM succeeded where LockBit failed may have to do with how 3AM functions. Instead of relying on the latest tech, 3AM actually operates based on an outdated script, Yugeon Web Clicks v0.1.
The theory is that, by doing so, the cyberthreat actor can circumvent more modern firewalls that aren’t optimized for “expired” softs. That doesn’t mean that the group doesn’t also have modern approaches and MOs.
Who is 3AM and How Does It Work?
3AM got its name from its file extension, as is the case with many ransomware actors. The actor first became noticeable during the failed LockBit attack and has resurfaced recently thanks to its original success.
The group’s MO is consistent with the double extortion method, which relies on downloading the data, encrypt it on the originating machine, and demand a fitting ransom. The value of the ransom is usually estimated based on the target’s profile.
If the target refuses to pay, the group will either sell the data or publish it publicly. Both actions can result in severe damages for the victim, both financial and from a reputation standpoint.
The proper defense mechanism against 3AM usually consists of a multi-layered approach in the form of an EDR (Endpoint Detection and Response). The goal is to detect early intrusions and stop their progress before any meaningful damages.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

