Akira Ransomware Attacks Becker Logistics LLC
Akira attacked Becker Logistics recently, a US-based transportation management corporation with history in the field. Becker Logistics has been in the market since 1997, so it’s safe to assume that it has quite a large database of customers.
- Becker Logistics didn’t comment on the incident, but it is presumed that they refused to pay the ransom
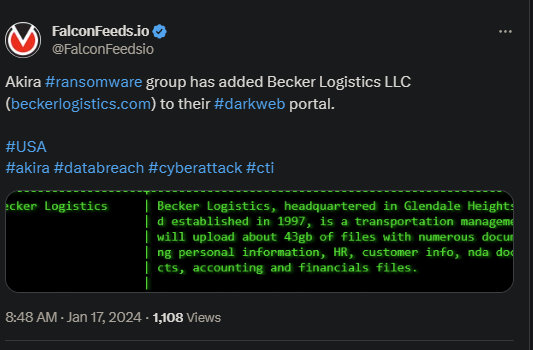
- Akira posted evidence of the attack and a note stating that they will release the data that they’ve managed to steal
- This amounts to little over 43GB of confidential information about the company’s clients, accounting, financial details, and other NDA papers
- Akira currently ranks as one of the most prolific and dangerous cyberthreat actors in the cyber sphere
Becker Logistics is a rather unusual target, since Akira prefers to focus on small and medium-sized targets. However, they don’t back down from addressing larger corporations whenever possible; it’s just that this isn’t the norm.
Akira is a very sophisticated ransomware actor that employs a variety of MOs and tools to achieve its goals. This allows it to often hit hard-to-break targets, despite the victims constantly upgrading their defense systems.
The details of the recent attack aren’t known, but, knowing Akira’s MO, they most certainly asked for a hefty ransom. Akira usually adapts the ransom demand to the victim’s financial capabilities to increase the likelihood of a successful payment.
Who Is Akira?
Akira first came into public light in March of 2023, which makes it a relatively young organization. Despite its recent emergence, the group has proven to be among the most dangerous in the business.
Akira acts fast and can hit multiple targets at the same time. It wasn’t long until the organization had several hundred victims under its name. The most prolific months were October and November 2023, but August was also notable.
However, the trend is growing, which causes serious concerns about the direction the organization is taking. Akira has proven itself to be a competent and far-reaching entity, with victims located all over the Globe.
This includes Europe, the US, and Australia. Akira also appears to hit indiscriminately. The group has been known to target consulting businesses, manufacturing companies, governmental institutions, telecommunication agencies, and many others.
An interesting peculiarity is Akira’s tendency to avoid any type of ransomware deployment. Instead, the group will only exfiltrate valuable data, without encryption, and demand ransom in exchange for deleting it.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

