Akira Went On A Ransomware Rampage In US
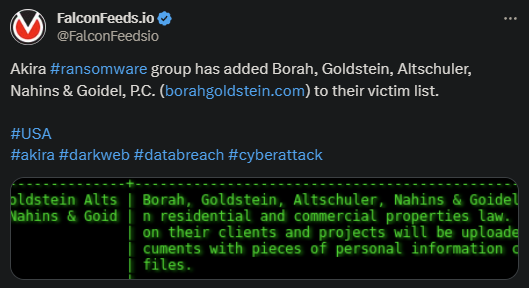
Akira attacked and infiltrated Borah Goldstein Altschuler Nahins & Goidel recently, managing to encrypt and steal a considerable amount of data. The attacker announced the attack on February 1st, along with the reminder that the data will be leaked soon.
- The victim is one with impressive history in the field of real estate and property law
- Borah Goldstein has been in the business for over 40 years, serving New York and holding an impressive database of clients
- It is presumed that Akira managed to steal a lot of confidential information about the company’s clients, finances, and operations
- Borah Goldstein didn’t comment on the recent attack and it’s unclear yet whether they’ve decided to negotiate the ransom or not
Ransomware attacks appear to be on the rise in 2024, following the trend set by the previous year. Most ransomware organizations are relatively new, dating back 2-3 years at most. Some are completely novel, like Akira, while others are rebranded veterans.
Ransomware attacks are generally more destructive and debilitating than standard DDoS intrusions. The may reason is that the primary attack method relies on the double-trouble problem.
The attacker will not only encrypt the parent system and disrupt the victim’s operations, but also steal valuable data and hold it for ransom. The victim then has to contact the attacker and reach a consensus regarding the value of the ransom.
If no consensus is reached, the cybercriminal organization will publish the data, which can potentially cause significant financial and reputational damage. Despite this, many victims refuse to pay.
Akira’s Identity and Primary MO
Akira is a novel cybercriminal entity that first broke into the public sphere in March of 2023. Despite its modest profile and recent breakthrough, Akira proved itself to be quite the formidable ransomware actor.
The method of attack relies primarily on exploiting (un)known vulnerabilities in the public domain. This allows Akira to infiltrate more cautious victims that have taken extra precautions to prevent ransomware attacks.
It’s also well-known that Akira ranks among the most brutal negotiators in the ransomware sphere, with some calling the group delusional. The ransoms they typically ask range in the millions and even hundreds of millions.
This explains why so many refuse to pay and prefer to handle the data leak on their own. It’s unclear where Akira will go from here, but one thing is certain: the cybercriminal actor is here to stay.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

