Anonymous Sudan Hacker Group Is Selling DDoS Services for Hire as ChatGPT Falls
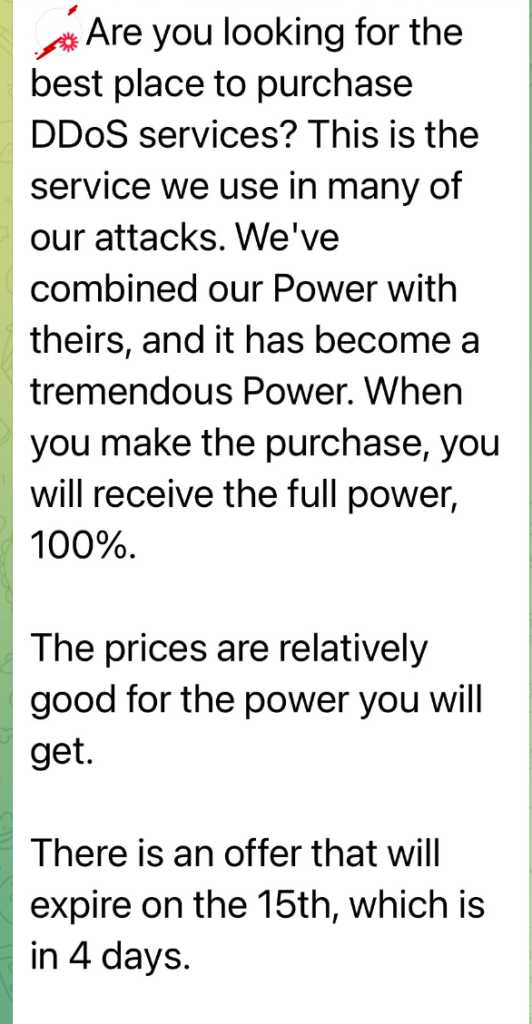
The Anonymous Sudan hacker group has recently announced that they’re selling DDoS services to anyone with the funds to pay. They claim to commit 100% of their resources in the DDoS-for-hire until the 15th of November.
- Anonymous Sudan has previously targeted Cloudflare, Open AI, the Daily Mail, and AP, with their preferred go-to tactic being DDoS attacks
- Their DDoS-for-hire services will only be available until the 15th this month at “reasonable” price points, as the hacker group claims
- The hacker group claims to put forth all of its resources in conducting DDoS-for-hire services in this period
- Anonymous Sudan is most likely a sub-group of the pro-Russian Killnet hacker group
The hacker group has made this announcement on their Telegram group, where they maintain contact with their followers and other cyber-criminals.
Anonymous Sudan appeared in January of 2023 and their targets consist mainly or global organizations and agencies.
The last we heard of them, they attacked OpenAI and disrupted ChatGPT’s services temporarily. OpenAI has made not offered any comments about this attack.
In a matter of days, it seems that the group turned to the Cybercrime-as-a-Service model and are now selling their DDoS capabilities to anyone who pays them.
Who Is Anonymous Sudan?
Anonymous Sudan is a newcomer threat actor who first made its appearance in January 2023. Trustwave SpiderLabs researchers claim that the group is related to the pro-Russian Killnet group.
They don’t appear to have any financial motivations but instead target known Russian targets. There seems to be no connection between Anonymous and Anonymous Sudan.
Moreover, they’ve recently attacked OpenAI on November 8th after accusing them of cooperating with the “occupation state of Israel”, further saying that “AI is now being used in the development of weapons and by intelligence agencies like Mossad.”
The group prefers DDoS attacks aimed at disrupting their targets’ services and causing chaos rather than profiting off of their actions.
It’s likely that we’ll keep hearing of Anonymous Sudan in the coming days as they’ll mount more and more DDoS attacks against high-profile targets.
Their latest shift to Cybercrime-as-a-Service where they sell DDoS-for-hire was an unexpected move from them that has raised alarms all over the world.
They’ve already attacked companies like Cloudflare, AP, and the Daily Mail, marking them as one of the biggest cyber threats around.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

