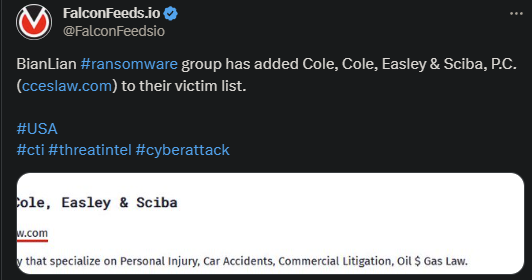
BianLian Adds Law Firm On Their Victim List
The US law firm in question is Cole, Cole, Easley & Sciba and it specializes in personal injury cases, car accidents, commercial litigation, and several other areas. The attack took place recently and led to important data leak. The victim didn’t comment on the event.
- BianLian is a relatively newly-formed cyberthreat enterprise, first emerging in 2022
- Ever since, the organization has been conducting weekly attacks on different targets, with multiple attacks taking place within a week at times
- There aren’t many details about the recent attack, but evidence indicates that BianLian used the classic double-extortion method
- The victim has several days to contact the attackers and negotiate the terms of decrypting their systems and deleting the stolen data
BianLian isn’t known as a particularly active ransomware actor, but its infiltrations are extremely effective and damaging. According to the latest investigations, BianLian has also moved away from the double-extortion practice.
This may be because it made the infiltration process more complex and costly. To circumvent that, BianLian opted for the simpler extortion method, stealing the victim’s data and threatening to release it publicly, but without encrypting it on the parent system.
However, this method only works if the data collected is more valuable than usual. Otherwise, the victim may simply choose to ignore the attempt at blackmail and simply take the loss. But if the data is confidential and very sensitive, they might need to negotiate.
Regarding its preferred victim type, BianLian doesn’t appear to play favorites. Rather, it goes where the money is and where the chance of infiltration appears higher. When it comes to the actual industries it targets, BianLian has a wide list of victims.
These include both public and private institutions from healthcare, manufacturing, legal services, education, real estate, and many more. The organization has even been known to attack entities from the aerospace and defense industry.
How Dangerous Is BianLian?
According to the latest investigation’s BianLian qualifies as one of the most dangerous in the ransomware sphere. On the one hand, the group usually avoids the double-extortion tactic, which makes it easier to deal with.
On the other hand, they are a very determined, resourceful, and aggressive entity with a very advanced toolkit. They often manage to secure considerable amount of confidential data which can quickly turn into a liability for the victim.
This is why many prefer to pay than having their sensible information leaked publicly. Taking some financial damages in exchange for keeping their reputation intact seems to be worth the trouble.
More importantly, it seems like BianLian has already made connections in the cyberthreat sphere. Private security analysts have found some code similarities between BianLian and Makop, another prominent actor.
This may either suggest that the 2 have shared the same developers in the past, or that they are actively sharing tools between each other. Either way, nothing is confirmed.
But it is interesting to see that BianLian may cooperate with other hacking entities to boost their capabilities and reach. This paints BianLian as a scary actor in the cyberthreat sphere.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

