BianLian Infiltrates US-Based B&B Electric
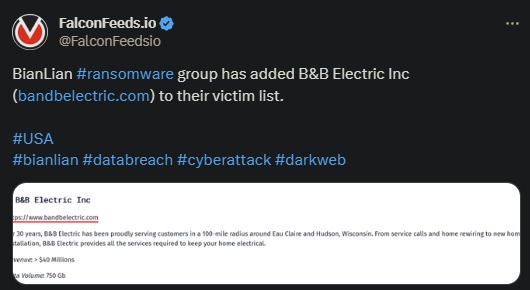
B&B Electric is BianLian’s newest victim, as stated by the attacker on its public platform. According to the original post, BianLian managed to infiltrate, encrypt, and steal an obscene amount of confidential data, totalling 750 GB.
- The victim didn’t make any public comment on the event, so it’s unclear if they’ve decided to negotiate with the ransomware actor
- BianLian is known for its sophisticated methods of attack and tactics
- The organization is also unwilling to negotiate the terms of payment in most cases and will only make small concessions in others
- As stated by prominent investigation entities, BianLian’s activity has increased visibly over the past year
While initially BianLian used the standard double-extortion practice, which involved encrypting the victim’s files and stealing them for ransom, it gradually shifted to exfiltration-only. In those cases, the group would no longer encrypt the data.
Instead, it only clones and downloads what it needs and use the material as leverage during negotiations. If the victim refuses negotiations or a consensus isn’t reached, BianLian will publish the data publicly.
This strategy only works if the victim is a high-profile corporate with a lot to lose. Or, at the very least, if the data that’s been stolen is very valuable.
This falls in line with BianLian’s preferred attack tactic. The organization typically targets valuable enterprises with a considerable revenue that they know they can milk successfully. This recent attack falls in the same category.
B&B Electric is a veteran in its respective field, with over 30 years of experience and a fat database of customers throughout and around Wisconsin. The company also packs a respectable revenue, with more than $40 million available.
This explains why B&B Electric made its way onto BianLian’s black list.
BianLian’s Profile
BianLian is relatively new, as it was first observed publicly in June of 2022. Most of the organization’s initial targets were US-based, but soon moved onto other continents, including Australia.
The organization prefers to target the healthcare sphere, but others are on the menu too. These include manufacturing, professional and legal services, high technology, construction, financial services, and others.
When it comes to the organization’s power and resources, private investigation teams have shed some light on the issue. A more complex assessment of BianLian’s code found similarities with the Makop ransomware actor.
This suggests that either the 2 groups share a codebase or that they have used the services of the same third-party developers. Both of these explanations are perfectly valid, given that that’s how most ransomware groups operate.
While BianLian isn’t as active as other ransomware organizations, FBI and CISA (Cybersecurity and Infrastructure Security Agency) places it among the 10 most dangerous extortion rings today. This is proof of the groups astounding influence.
When it comes to BianLian’s resources and gains, little data is available, given that the actor prefers to not disclose its profits. They are, though, known to demand high ransoms and show rather blunt negotiation tactics, with little wiggle room.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

