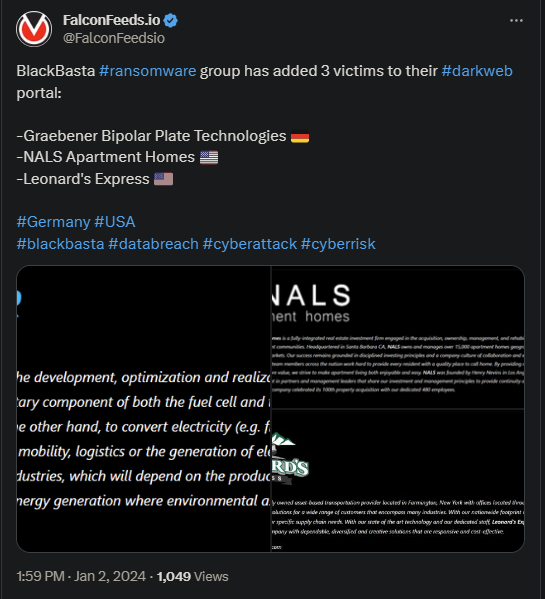
Black Basta Adds 3 More Victims to Their Portfolio
BlackBasta ransomware attacked 3 more corporate entities recently in Germany and US. The 3 victims are Graebener Bipolar Plate Technologies, NALS Apartment Homes, and Leonard’s Express.
The attacks resulted in a security breach, data cloning, and data encryption. It is unclear for now how the victims reacted to the event.
- BlackBasta became public in the first trimester of 2022, but grew exponentially since
- The organization racked up 19 high-profile victims and more than 100 low-profile ones within its first few months of activity
- The group operates globally, targeting various governmental and corporate entities in countries like Canada, US, Australia, Japan, and others
- The recent attacks led to a significant data leak
BlackBasta has a history of aggressive tactics, often hitting multiple targets at the same time. The group appears to be strictly financially motivated based on their profile and preferred MO (RaaS attacks.)
It’s unknown how much the ransom was worth in either of these 3 attacks, but BlackBasta is known for its ruthless attitude, greed, and extreme negotiation tactics. The March 2023 ransomware attack on Capita is clear evidence of that.
The public sector specialist, Capita, approximated damages worth of 15 to 20 million pounds as a result of the attack. It’s unclear if that includes the ransom costs or even if Capita actually paid it.
But in that case, as in many others, the breach caused an important data leak and blocked the victim’s operations for days. This led to even more significant financial losses.
Who is BlackBasta?
The group’s true identity is unknown, but Russian connections are suspected due to this being the organization’s preferred posting language. The group took off in early 2022, which also coincided with the start of the Ruso-Ukrainian war.
The general theory, though, is that BlackBasta built itself from the remains of Conti, one of the most prolific ransomware actors in history. Conti earned more than $150 million in ransom income in less than 2 years, until its fall.
BlackBasta relies on a very aggressive and intricate MO, infiltrating the victim’s system, phishing for credentials, using bots, and rely on Powershell to gain access to secondary networks. The actor will steal and encrypt as much data as it can.
The value of the ransom is always directly proportional to the victim’s financial capabilities to ensure payment. The alternative is to have the data either sold or spread across the DarkWeb for free.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

