BLACK SUIT Ransomware Targets US-Based Corporation
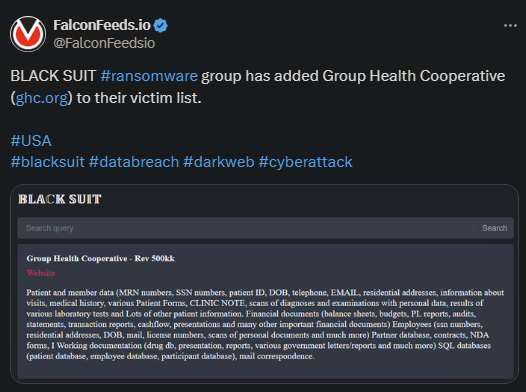
BLACK SUIT announced that they’ve breached a major US-based corporation: Group Health Cooperative. The original post doesn’t detail how much data they’ve stolen, but it does detail the type of data.
- BLACK SUIT managed to steal confidential information about patients and the organization’s structure and activity
- The hackers also didn’t detail the value of the ransom, the deadline for negotiations, or any other special demand
- It’s unclear whether the victim has contacted the hackers for negotiations or they’ve decided to ignore them
- To be noted, there is no decryption key for the BLACK SUIT ransomware
Ransomware attacks have been on the rise recently, both from hacking groups and RaaS (ransomware-as-a-service) entities. BLACK SUIT has joined the trend too, although it’s not as active as other high-end cybercriminal rings.
Despite that, BLACK SUIT managed to establish itself as a feared ransomware gang. They rely on highly advanced and sophisticated software, but their attack methods are fairly standard. The group relies primarily on phishing via emails.
Unlike other ransomware groups, BLACK SUIT paints itself as a moral actor. The hackers paint their work as altruistic; a service to those they breach. As ransomware notes show, BLACK SUIT believes that all they’re doing is highlighting system vulnerabilities.
The ransom they’re asking for file decryption and data deletion is simply the payment that they deserve for their services. In exchange for that, they also offer advice on how the victim can strengthen their defenses to prevent such events in the future.
What Should You Do in Case of a Ransomware Attack?
The ideal would be to prevent the ransomware breach, to begin with, but that’s typically easier said than done. This is why you should always rely on experts to improve your system security. But what if, despite that, you’re still breached?
In that case, you have 2 options. Either cave into the hackers’ request and pay the ransom or contact specialists to restore your file. This means accepting that your data will be shared with other hackers on the black market.
There is no simple and straightforward answer, but experts recommend ignoring negotiations and not paying the ransom. Each ransom paid incentivizes the criminals to keep their operations alive and running.
Plus, cybersecurity analysts explain that paying the ransom doesn’t guarantee anything anyway. The hackers can still share the data with other cybercriminal rings, which, in turn, will extort the victim again, sometimes months later.
BLACK SUIT isn’t known to do that, but there is no clear evidence that they haven’t done it either. It’s important to remember that many cybercriminal organizations collaborate with each other.
They either perform DDoS or ransomware operations together or share the loot they obtain for extra gains.
At this moment, BLACK SUIT doesn’t qualify as a RaaS actor. The cybercriminal ring remains a closed and exclusivist organization, as they prefer to keep their cards close to their chest. This explains why the ransomware actor hasn’t been cracked by the FBI yet.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

