BLACK SUIT Targets US-Based Enterprise
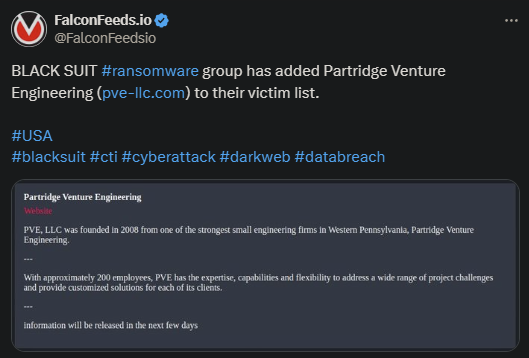
The BLACK SUIT ransomware actor announced a new US-based victim: Partridge Venture Engineering. The hackers posted the news about the breach, along with several words about the victim’s profile and history.
- BLACK SUIT operators also announced that the victim’s confidential data will be leaked publicly soon, hinting at the possibility that the negotiations have failed
- BLACK SUIT is a controversial ransomware gang with some linking it to more powerful actors like Conti or Royal
- The BLACK SUIT hackers communicate with victims via their TOR platform, which is where negotiations take place
- It is unclear how powerful and dangerous the infamous ransomware gang is and whether it’s an actual organization or a cybernetic Trojan horse
The latter isn’t just a vapid theory, as there are quite a few precedents to consider. High-profile ransomware organizations often use mock-up so-called “gangs” to conduct their operations under a different identity.
This is done to take some of the heat off of the organization’s name and fly under the FBI’s radar. But is this actually the case with BLACK SUIT? The answer is unclear, but there is evidence to point to a ‘yes.’
The US Department of Health and Human Services (HHS) published a report that highlighted the striking similarities between BLACK SUIT and Royal. These referred to code and tactic overlaps.
The same public advisory referred to the organization as a direct successor of the now-defunct pro-Russian Conti. That being said, nothing has been confirmed as of yet. But it’s worth noting that ransomware organizations are often rebranded names of older ones.
How to Survive a BLACK SUIT Attack?
The cybercriminal gang operates similarly to the rest of its peers. The standard method of attack revolves either around infected emails or compromised links or ads. Once the hackers are in, the situation degrades fast.
They will encrypt the victim’s files and download as much valuable data as they can. They will then leave a note instructing the victim to contact them via their TOR network to negotiate. And that, experts advise, you should never do.
Most victims refuse to negotiate with the hackers, but some do, and it never ends well. Cybersecurity professionals explain that paying the ransom not only does not solve your problem but may create additional ones as well.
As data shows, most ransomware groups will either leak the data publicly or sell it, whether the ransom is paid or not. Some won’t do either but will keep it instead and use it for other purposes later down the line.
The alternative is to take the hit, refuse any communication with the hackers, and deal with the fallout of the data leak. It may be costly, and it may tarnish the victim’s reputation, but it beats losing a lot of money on top of that as well.
When it comes to an actual plan against the ransomware actor itself, the solution is simple: prevention is your best friend. The best advice you can get is: to act as if you’re in immediate danger and work with professionals to boost your cyber-defense.
This includes training your personnel on how to identify the danger and avoid the baits.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

