BlackSuit Breaches Nigerian Company
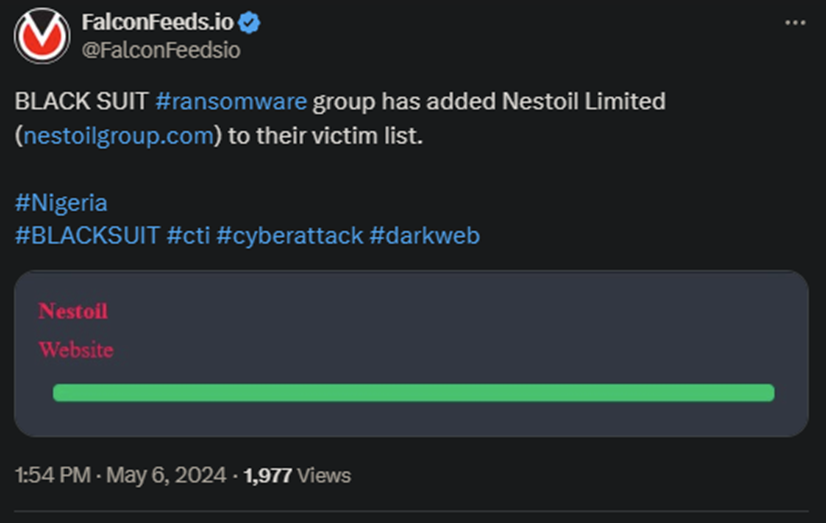
BlackSuit announced another high-profile breach with the Nigerian Nestoil Limited taking the hit. The hackers announced the operation on their leak website, but didn’t provide any additional details.
- Nestoil Limited didn’t comment on the event, so the status of the negotiations is unclear
- It is presumed that the company has refused to comply with the hackers’ demands yet, given that BlackSuit hasn’t released any data yet
- BlackSuit is a novel ransomware organization, as it first emerged publicly in May 2023
- The ransomware gang showed promise from the get-go, using advanced tactics and tools to infiltrate their targets
Cybersecurity experts have warned against BlackSuit’s potential shortly after its public release. One reason for that is the purported link between the BlackSuit and the former Royal gang. Royal gang also had connections to Conti.
This whole food chain is to be expected with most new ransomware organizations, as there are rarely any original ones. Most of them are either rebranding extinct organizations or taking heavy inspiration from them. Some are even mock-up gangs.
The latter are only used as façade by legitimate gangs to hide their trails and fly under the radar. BlackSuit appears to be a legitimate entity, but one with close ties to other high-profile actors. This raises an alarm signal regarding the gang’s actual capabilities.
The BlackSuit operators always leave behind a note announcing the victim of the breach. They leave instructions on how they can be contacted for negotiations and offer free system analysis services after the ransom is paid.
The hackers use the standard double-extortion practice, encrypting the victim’s file and downloading all of the sensitive data they can get. This may include customer information, financial sheets, and other confidential data they can get.
This brings up an interesting question: should you pay the ransom to recover the data?
How to Deal with BlackSuit Attacks
The standard recommendation is to ignore any calls for negotiations and move on. Paying the ransom typically places the victim on the hackers’ list, so they know who to breach again in the future. However, if it were as easy as that, nobody would pay the ransom.
So, why do some choose to pay? Especially when considering that most victims have data backups in place?
The answer is simple: because of the fallout associated with the public exposure of the data. There may even be legal repercussions, depending on the type of data being leaked, such as sensitive information about employees and customers.
The reason is that it’s the provider’s job to secure the data and prevent such leaks. So, many providers pay the ransom in hopes of avoiding that. Which, as experts suggest, doesn’t work anyway, because most ransomware actors leak the stolen data anyway.
This means that there’s no definitive solution for all cases. The best approach is still prevention and reducing the risk of an attack in the first place. To achieve that, the recommendation is to work with legitimate professionals to boost your defenses.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

