China and US Fall Victims to LockBit
LockBit posted evidence of their recent attacks on 4 major targets, Goldwind, located in China, and Bemes Inc., Spirit Leatherworks, and Robert F Pagano & Associates, located in the US. The aftermath of the attacks is still uncertain.
- LockBit currently ranks as the most active, dangerous, and most prominent ransomware actor on the market
- The organization is highly aggressive and attacks both private and public institutions, disrupting the victims’ operations and encrypting important data
- LockBit operators also download as much data as they can, which they can then use to blackmail their victims
- If the victim refuses to pay, LockBit either publishes the data or sells it for profit
The recent attacks follow the same MO associated to LockBit. The victims’ defenses were penetrated, followed by data encryption and important disruption of internal operations.
The cyberattacks proves once more how effective and dangerous LockBit is, as it can circumvent most defense mechanisms. The hits were financially motivated, which falls in line with how LockBit operates.
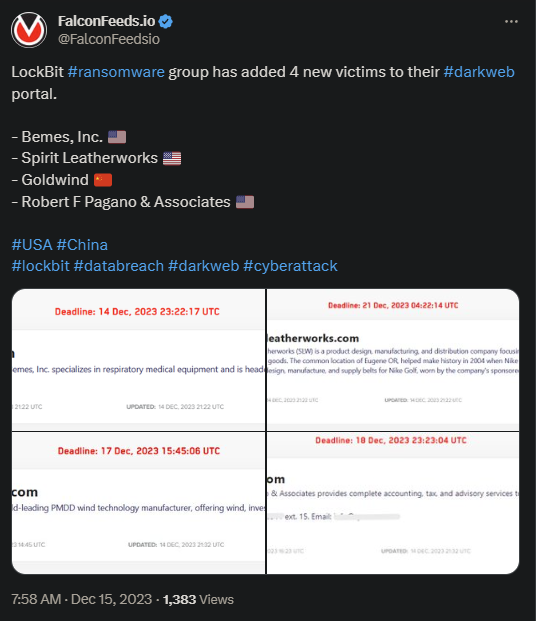
The information about the attack was published by LockBit itself on its public website. These attacks follow the recent trend in LockBit’s activity, as the organization has been extremely active over the past year.
It is estimated that LockBit is responsible for at least 1,000 hits between July 2022 and June 2023. This is close to 3 times more than the next in line, BlackCat, who’s only responsible for less than 400 attacks.
How LockBit Operates
Lockbit gained a lot of notoriety fast, firstly due to its aggressive approach and secondly thanks to the advanced strain of ransomware it uses. LockBit can penetrate a variety of defense systems and can quickly overwhelm even the most potent firewalls.
The attack always aims to clone and encrypt the victim’s data, cutting access from vital information and disrupting the operations. Most of the attacks are successful, as the victims prefer to pay to regain access to their data.
This is only possible due to LockBit operators being very conscientious about the need to upgrade the soft constantly. LockBit has developed several encryption variants over time, allowing the ransomware itself to adapt to even the reactive defenses.
The group’s longevity and success are also evidence of the organization’s discipline and internal coherence. LockBit has been active since late 2019 and it doesn’t show signs of stopping anytime soon.
The group’s resilience and constant self-improvement have opened the door to several collaborations with other ransomware agents. These include names like BlackMatter and Evil Corp, among others.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

