Cloak Ransomware Gang Attacks Spanish Vehicle Rental Company
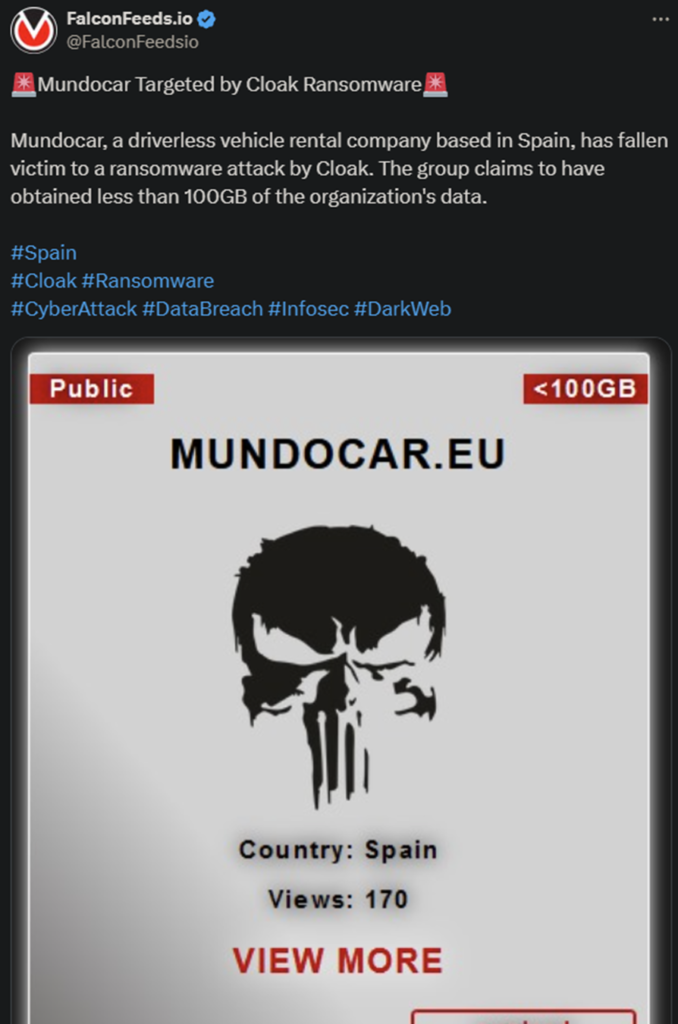
The anonymous Cloak ransomware gang announced a massive breach against Mundocar, a Spanish vehicle rental company. Mundocar did not confirm or comment on the event, but it does appear to be legit, at least at first glance.
- The hackers have tagged the job as ‘Expired’ on their leak site, which may suggest that the negotiations have failed
- According to Cloak’s post, the hackers managed to get away with 100 GB of internal data
- Cloak is a newcomer in the ransomware sphere after coming out publicly at the beginning of 2023
- The organization relies on the double-extortion practice to force the victims to comply with their demands
Ransomware attacks have been visibly more devastating in 2023, compared to the previous year, a trend which seems to continue in 2024. Ransomware gangs have also increased their activity with Lockbit leading the herd.
Experts place ransomware breaches higher on the list in terms of potential damages, compared to other types of cyberattacks. There are several reasons for that.
The first one is also the most obvious one: the data loss itself. It’s never a good sign when known hackers have possession of your sensitive data. Then there’s the problem of paying the ransom which, in almost all cases, it’s hefty to begin with.
The hackers will always approximate the value of the ransom based on the victim’s revenue profile. The higher the victim’s revenue, the higher the ransom.
Then we have the legal issues stemming from the breach itself. Because the target company is responsible for all of its employee’s and customers’ data, any leak makes it directly liable. This is one reason why many enterprises refuse to report ransomware breaches.
Finally, there’s the problem of the hackers sharing or selling the stolen data to other cybercriminal entities. In turn, these will then extort the victim again or use the data for their own gain.
How Cloak Operates
Despite being relatively new in the ransomware sphere, Cloak isn’t really innovative in the field. Instead, it sticks to the classic double-extortion practice. This allows the hackers to increase their leverage during negotiations.
The victim needs to pay for both the decryptor to recover access to the system and the deletion of the stolen data. The problem is that the latter rarely works. The hackers prefer to keep the data to themselves and either use it later or share it with other hackers.
Sometimes, it’s both.
Cloak is currently anonymous, as there is no clear information regarding its profile, code, members, or internal structure. However, given how the ransomware sphere operates, it’s more likely than not that Cloak is related to at least one other cybercriminal gang.
Ransomware organizations often collaborate with each other for higher and easier gains. They also often share manpower and resources, especially when pressed by law enforcement agencies. In the case of the latter, many gangs also dissolve and restructure.
So far, Cloak hasn’t been as active or as successful as high-tier ransomware operators, but the situation can always change.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

