CUBA Ransomware Adds DMS Imaging To Its Victim List
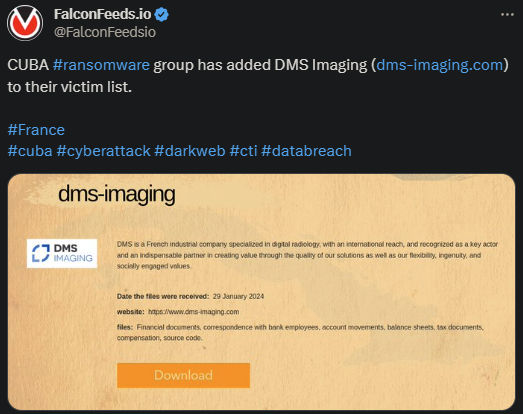
Veteran CUBA ransomware infiltrates France-based DMS imaging. The attack supposedly took place on 29th of January, current year, and led to important data leak and encryption. It’s still unclear how CUBA managed to penetrate DMS imaging.
- The victim specializes in digital radiology and has an international reach and global reputation
- The attack seems to have led to critical data loss, so it’s unclear what DMS imaging will do moving forward
- According to CUBA itself, the attacker managed to extract information about the victim’s client base, financial situation, confidential correspondence, balance sheets, etc.
- It is presumed that the negotiations are ongoing regarding the ransom
CUBA currently ranks among the most active and dangerous ransomware actors in the world, although it’s not as popular as Lockbit or BianLian. But the numbers don’t lie. CUBA has produced hundreds of victims between 2022 and 2023.
The organization has also secured approximately $60 million in ransomware profits over the course of its lifespan and it doesn’t seem to stop. This amount of financial success gets close to replicate that of Lockbit. The latter has $90 million to its name.
The recent attack shows CUBA’s proficiency and effectiveness in infiltrating pretty much any target. So long as the reward is worth the effort, of course.
Who’s CUBA Ransomware And How Come You Haven’t Heard of It?
CUBA ransomware first hit the public sphere in 2019, but only rose to prominence 3 years later, in 2022. Up to that point, CUBA was only known for sporadic, low-profile hits, until 2022, when the group’s activity ramped up drastically.
Within the span of a year, CUBA racked up several hundred victims and dozens of millions of dollars in ransomware gains. This sparked significant interest from organizations like CISA and the FBI, which raised an alarm signal about the org.
CUBA’s identity and structure are still unknown, but there are theories circulating around. While the organization itself claims to be Cuban, as the name suggests, hints have been found that suggest links to Russia.
The Russian affiliation may explain the organization’s sudden rise to power and its abrupt financial growth. One of the main reasons why Russia is considered to be the main puppeteer is the fact that Cuba lacks any meaningful software capabilities.
This makes it unlikely for any Cuba-based ransomware entities to growth into the global threat that CUBA is.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

