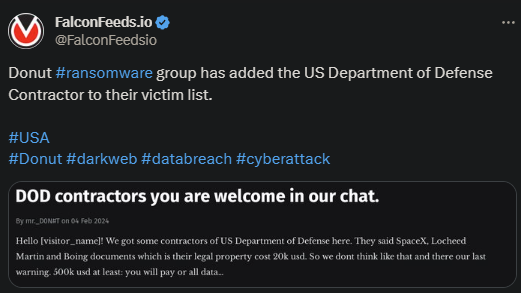
Donut Ransomware Attacks US Department of Defense Contractor
Donut infiltrates DOD contractor and posts the evidence on their public platform. According to the attacker, the data they’ve managed to steal is valued at $20,000 by the victims. So, Donut decided to ask for a $500,000 ransom instead.
- The victim didn’t comment on the attack and it’s unclear if they’ve decided to contact Donut representatives
- Donut is a newcomer in the ransomware sphere, which is why not many are familiar with it
- The organization quickly made a name for itself by targeting high-profile victims and extracting important confidential data
- According to the latest statistics, Donut secured approximately 2.5 TB of data from their last 10 victims
The group is still in its incipient phases, which is why not much is known about its structure and members. Some affiliations have been identified, though, linking Donut to other major cybercriminal groups like Ragnar Locker and Hive.
As the evidence suggests, Donut may have operated in the shadow of other major ransomware actors for more than a year. The first evidence of its existence came through in mid-2022.
The first hint that a new data extortion gang may be rising in the ransomware world came with the hacking of DESFA, a Greek natural gas company. The company reported a major breach in August of 2022, pointing at Ragnar Locker as the culprit.
A month later, another breakthrough took place. Another private company reported a ransomware infiltration under Hive’s name. The problem? Neither of these 2 ransomware actors didn’t seem to have been the actual culprits.
Donut’s Inception and A Look Into The Future
While the 2 reports seemed to lack any connection, one was shortly found. Both Ragnar Locker and Hive only published a small amount of data, compared to what was actually stolen. Instead of releasing the entire leak, as is usually the case.
However, at the same time, Donut, a completely unknown extortion ring, published the whole data package that the other actors were missing. Subsequent investigations hinted at the very plausible explanation that Donut was actually the culprit.
After breaching into their victims’ systems, Donut stole the data and sold it to Hive and Ragnar Locker. The latter 2 would then both extort the initial victim as well, while Donut would remain in the shadows.
The organization then became public and began conducting targeted operations using their own identity. However, the extortion method remains the same: Donut steals as much data as possible and shares it with other ransomware actors.
Essentially, they’re selling or giving away ammunition to other cybercriminal rings who too extort the victim for even more money. This is why specialists advise against paying the ransom.
Because, doing so will not only keep the attackers in the business, but will maybe incentivize them to sell the data to other actors as well. These will then extort the victim as well, leading to even greater financial losses.
Not to mention, paying the ransom tags the victim as profitable, increasing the likelihood of additional future infiltrations.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

