Freshly Revived Lockbit Announces 2 Victims
Lockbit ransomware has claimed 2 more victims since its recent resurrection in an attempt to make a clear statement. Lockbit has been at the forefront of the news recently after being targeted by the Cronos operation.
- The FBI worked with their UK-based counterparts to dismantle Lockbit during the Cronos operation
- The law enforcement agency seized the organization’s main website and resources
- In an unexpected turn of events, Lockbit bounced back and resumed its normal operations
- Their first victim was the FBI itself
Not only that Lockbit recover in record time from the FBI operation, but it also targeted the FBI immediately after. The law enforcement agency didn’t comment on the attack, but the investigation is underway, trying to determine how that was possible.
Lockbit also released its 3.0 version soon after the event, showing that the group is fine and thriving and that they’re planning to expand. As of recently, the group’s website went back online, which is rather atypical.
Most ransomware organizations that have been hit by the FBI seek to rebrand themselves and change their tactics. Not Lockbit.
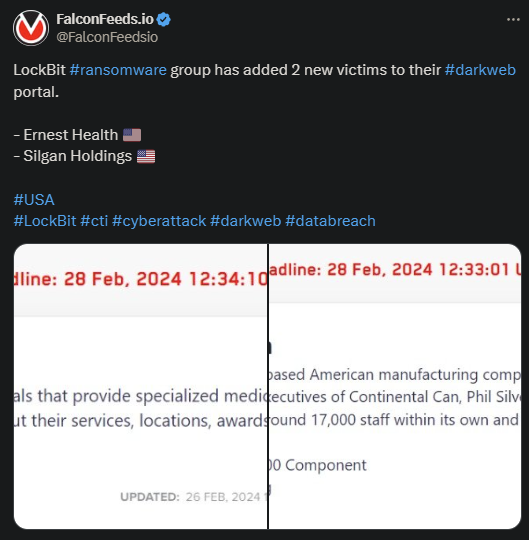
These recent attacks bear the mark of Lockbit’s usual tactics. The group breached the 2 victims on the 26th and gave them 3 days to contact Lockbit operators and begin negotiations. If not, the stolen data will be published publicly.
The 2 involved in the attack are Ernest Health and Silgan Holdings, both from the US.
How Come Lockbit Is Back?
A similar case happened with other ransomware organizations like Hive and RansomHouse, which disappeared from the public eye in their old form. But their new forms live on.
Currently, there are numerous organizations that share code and tactics similarities with Hive and RansomHouse. Many of the people working for these 2 extortion rings jumped boats and joined other, more modern groups.
This explains why extortion rings never truly go away. They simply change names, reorganize their tools, and spread out their workforce to avoid detection. Arrests are often conducted, but the overall group stands its ground.
The same applies to Lockbit. The problem, though, isn’t only that Lockbit returned, but that, with 3.0, it returned stronger than ever. But what makes Lockbit such a threat in the ransomware sphere? Several things:
- High activity and resources allowed them to produce more than 2,000 victims worldwide and financial gains of up to $120 million
- The tendency to work with the most talented, knowledgeable, and motivated individuals
- Always upgrading their systems, tactics, and tools
- Working with affiliates to increase their earnings and evade detection
- Undergoing several version updates to stay one step ahead of their victims and law enforcement agencies
These critical points turn Lockbit into one of the most prolific ransomware actors in the world. And it doesn’t appear as if the situation will change anytime soon.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

