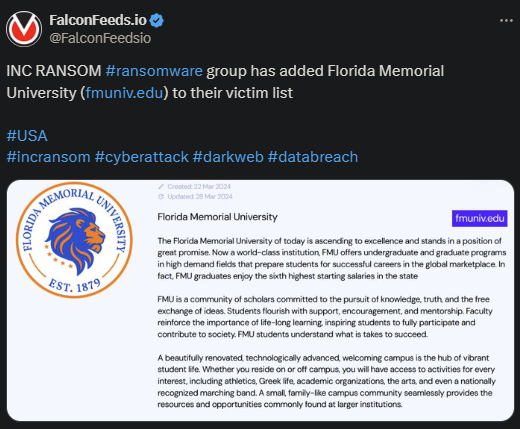
Inc Ransom Targets Florida Memorial University
Inc Ransom has breached Florida Memorial University. It’s unclear how much data the hackers managed to steal or how damaging the attack has been overall. No university representatives have commented on the event.
- Inc Ransom is a relatively new ransomware actor, having emerged publicly in August 2023
- The group has been involved in several high-profile attacks, most of them (>50%) in the US, close to 17% in the UK, and the rest in Singapore, France, Netherlands, and Austria
- The hackers don’t discriminate, as they typically hit the most profitable industries like IT, battery manufacturing, metal refining, real estate, and governmental institutions
- Unlike other ransomware actors, Inc Ransom doesn’t sell the victim’s data in case of failed negotiations; it leaks it online for free
Ransomware attacks have been on a steady growth trend over the past several months, despite the FBI trying to contain the situation. The American law enforcement agency has cracked down on several high-profile ransomware actors.
One of these is Lockbit in February of this year, which didn’t last long because Lockbit resumed its activity shortly after. But it’s undeniable that major law enforcement organisms around the world rage a never-ending battle against cybercriminal groups.
This explains not only why Inc Ransom prefers to keep a low level of activity but also why it prefers stealth. The hackers are always careful to cover their tracks and not leave too many breadcrumbs behind them.
However, Inc Ransom operators tend to be more feared than others due to their more aggressive negotiation tactics. So, let’s talk about that.
What to Know About Inc Ransom?
We’ve already touched upon Inc Ransom’s ideal victim profile: preferably wealthy and poorly protected. The fact that the infamous ransomware actor is so careful when choosing its victims suggests that the hackers have the means to make the most of it.
However, that’s not the real reason why most corporations with a lot of losses fear Inc Ransom. Instead, it has to do with the hackers’ negotiation tactics.
Inc Ransom operators use the standard double-extortion method, which involves encrypting the victim’s files and stealing valuable data. But most ransomware actors do that. What Inc Ransom does differently is that it creates extra leverage during negotiations.
The hackers will negotiate both the decryption key and the data, as well as the victim’s reputation as a whole. That’s because Inc Ransom will often accuse the victim of immoral business practices, which they claim they have evidence for.
It doesn’t matter whether the evidence is legitimate or fabricated, the hackers will leak it publicly anyway in case of failed negotiations. This will often impact the victim’s reputation just the same, even if the leaked data is not legitimate.
This is why many victims prefer to pay the ransom or find another way to please the hackers.
Even so, cybersecurity analysts point out that paying the ransom does nothing to protect the victim’s reputation or prevent the confidential data from reaching the public eye. In many cases, the hackers will leak the data publicly anyway, even if the victim pays.
This includes Inc Ransom as well.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

