Iranian Cyber Av3ngers Targets Israel
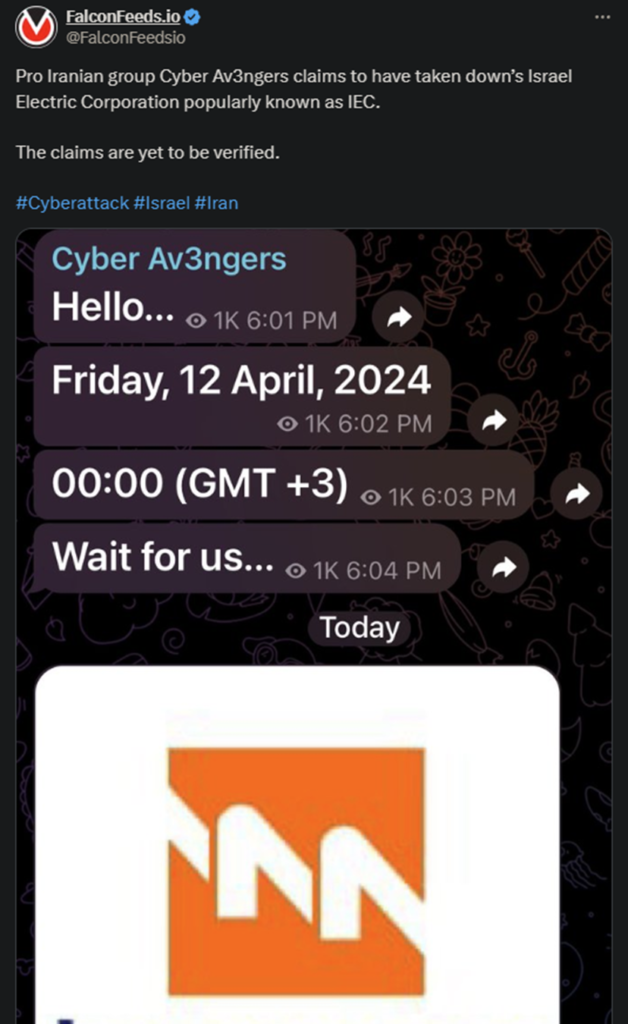
Pro-Iranian cybercriminal gang Cyber Av3ngers claims to have targeted Israel Electric Corporation (IEC.) The attack hasn’t been confirmed, but this is typically the case with Cyber Av3ngers.
- The hackers haven’t provided any details regarding the attack other than the announcement itself
- Cyber Av3ngers is a controversial cybercriminal group with a shady history and uncertain beginnings
- The first public traces associated with Cyber Av3ngers date back to July 2023, but the hackers claim to have started their business in 2020
- Cyber Av3ngers is associated with the Iranian government and operates as an affiliate
Cyberwarfare is by no means a new concept, and Cyber Av3ngers are just one of the many cybercriminal gangs involved in it. All countries are involved in some type of global conflict use cyberwarfare operations against their enemies.
Iran is a major player in this sense, with several high-end cybercriminal groups at its disposal. Some of these operations are conducted by the Iranian government itself, while others are taken over by affiliates and affiliate organizations.
Cyber Av3ngers is one of them and currently ranks as one of the fastest-growing one today.
Most of these cybercriminal operations involve some type of DDoS breach, although some involve multiple attack MOs. Data leaks are also common, especially for espionage purposes or even financial gains.
Ransomware organizations thrive on the latter, with some targeting high-profile institutions, both state-owned and private. But Cyber Av3ngers doesn’t appear to have a financial component to its tactics. Instead, the group is strictly politically motivated.
Is Cyber Av3ngers a Legitimate Group?
The question is warranted, given the gang’s activity over the past half a year. First, the hackers claim that they’ve been in service for far longer than the public has observed them. They claim 2020 as the first year when they became active.
However, there’s hardly any evidence of that, as everything points at 2023 as their first public operation. Then there’s the fact that many of the gang’s alleged operations are just that, alleged. Just like this recent one against IEC, many of its hits haven’t been confirmed.
Some have, which lends the idea that the group is legitimate some substance, but by no means does this apply to all operations. A potential explanation for this is that the group tries to appear larger, more resourceful, and more powerful than it actually is.
This is a common tactic, meant to spread fear and intimidate potential targets. As to why the gang has targeted Israel, that’s self-explanatory. Being affiliated with Iran, it’s safe to say that Cyber Av3ngers share the same political and ideological views.
It’s also no coincidence that the attack occurred in a time of rapidly-growing tensions between Iran and Israel. It’s important to mention that despite being new in the cybercriminal sphere, Cyber Av3ngers already shows a lot of potential.
The gang has managed to infiltrate critical and well-protected infrastructure systems, including US-based water facilities. It also appears that the hackers often steal data or cause data leaks, which can increase the damages they can inflict.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

