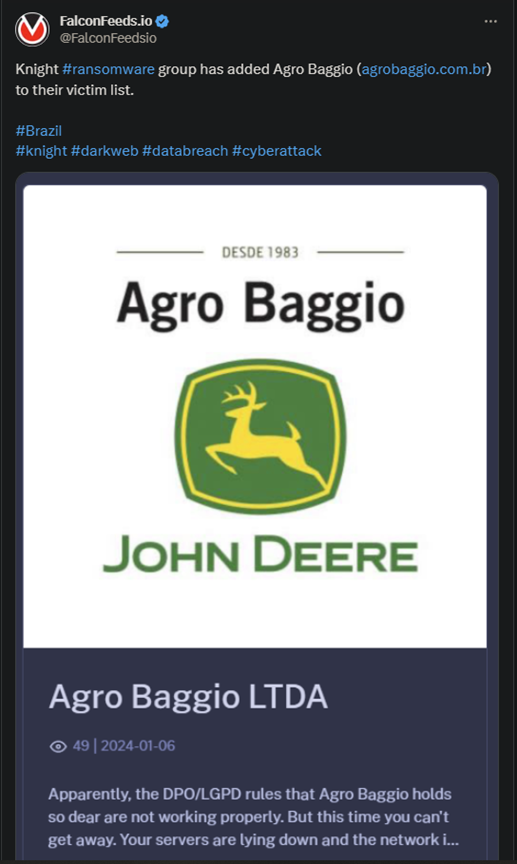
Knight Ransomware Attacks Agro Baggio
Knight ransomware reaches Brazil, this time attacking Agro Baggio, a company dealing in agricultural machinery and services. The company’s website went offline because of the attack, but the actual aftermath isn’t clear.
- If this attack followed Knight’s normal MO, then the victim’s operations were suspended and critical data was cloned and encrypted
- Knight always leaves a ransom note behind, instructing the victim on how to contact one of its representatives
- Knight is a newcomer on the ransomware stage, as it went public in August of 2023
- Since then, it has been involved in several high-profile attacks
Although little is known about the group’s internal structure, the most widely-accepted suggestion is that Knight is a version of Cyclops. This software is being sold on the RAMP forum, making it difficult to track the actual identities of those behind it.
The main MO involves phishing and spear phishing, many attacks relying on false TripAdvisor advertisements. This was especially true during the group’s initial attacks.
Although the group’s origins are still unknown, many of its attacks have been concentrated on US soil. As it turns out, little over 60% of the attacks were aimed at American companies.
The organization also seems to avoid the public sector as a general rule, although instances of public institutions being hit do exist. Knight’s primary targets are retail sellers, but other sectors have been affected too.
Who Is Knight?
The accepted theory is that Knight is simply a rebranding of Cyclops. This comes primarily from Knight’s own public posts in July of 2023, when the group stated openly that they will change their name to Knight.
Knight appears to be strictly financially motivated, as the organization hasn’t stated any clear ideological or political ideas. The ransoms they ask in exchange for full system restoration and data deletion are always directly proportional to the victim’s numbers.
Knight uses the typical double extortion technique, downloading and encrypting the data, and threatening to publish it in exchange for the ransom. It’s unclear how many successful hits are associated with Knight.
The group has also produced Knight Lite, which affiliates can use in spam-based attacks. All victims receive a ransom note that directs them to the Tor network where they will then receive an email address.
They are supposed to use that email address to contact Knight representatives and begin negotiations. The best strategy against Knight, as it is with all ransomware agents, is improved defense systems and better awareness.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

