Knight Ransomware Targets Brazil and Romania
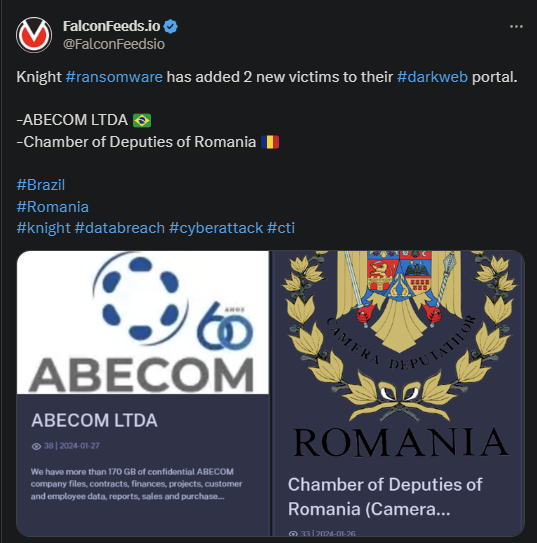
Knight is responsible for 2 ransomware attacks, as stated by the organization itself in a public post. The 2 victims are ABECOM LTDA from Brazil and Romania’s Chamber of Deputies.
- The attacks took place a day apart and resulted in significant data leak
- According to the original post, ABECOM lost around 170 GB of data, while the Romanian institution lost the equivalent of 250 GB
- Knight posted evidence of the attack on their TOR network and stated that the negotiations have begun
- The hackers are notorious for their aggressive negotiations and high ransom demands
Ransomware attacks have increased in frequency lately, which suggests that the business is blooming. The emergence of novel ransomware actors over the past several years is additional proof of that. Such is the case of Knight.
Despite the organization first public iterations dating back to August of 2023, the actor isn’t a newcomer. In fact, Knight is the rebranding of Cyclops, a veteran in the ransomware sphere.
Ransomware attacks are especially dangerous and debilitating, sometimes more dangerous than standard DDoS disruptions. At least DDoS attacks are easily reversible, even though this isn’t the case in some situations.
Ransomware attacks, though, fall in a different category. The main problems include losing significant data, having the systems paralyzed, which leads to financial damages, and having to negotiate with the attackers so that they don’t publish the data.
How Knight’s Ransomware Operations Work
Knight isn’t an innovator in the ransomware field. The cybercriminal actor uses the same double-extortion method that’s so popular among ransomware groups. The attacker will encrypt and steal the data, then demand ransom in exchange of deleting it.
If the victim refuses negotiations or a consensus isn’t reached, they will publish the data publicly. This can result in significant financial and reputational damages, which can have lasting effects. It is then no surprise that many victims prefer to pay the ransom.
However, specialists argue against that. The main reason is that paying the ransom incentivizes ransomware actors to stay active in the business. On the other hand, only the victim can decide the best course of action, depending on the case.
Because, in some situations, paying the ransom could be the better option.
Knight uses a variety of attack methods, including phishing campaigns, including through false TripAdvisor advertisements. The ransomware actor is constantly evolving, though, always improving its structure, tools, and MOs.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

