Lockbit Ransomware Locks Down Oil Company in Oman
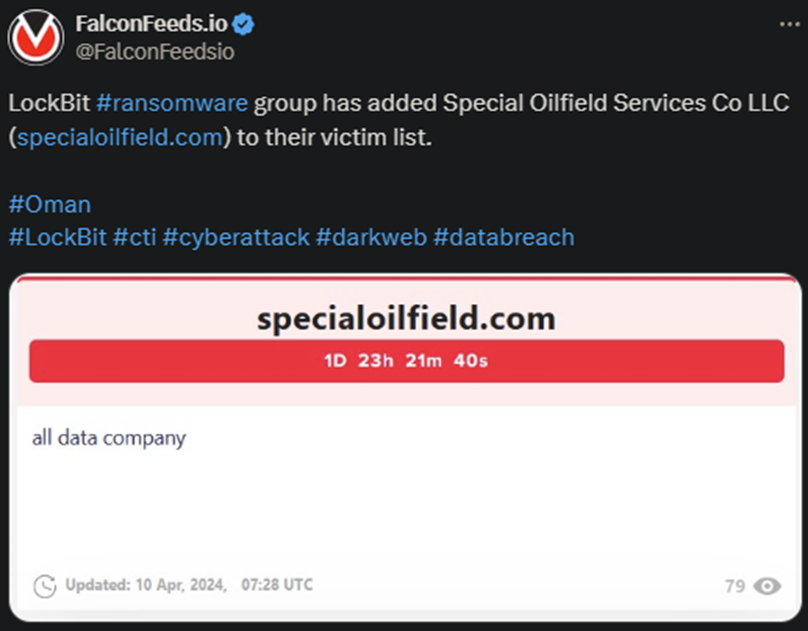
Lockbit hackers announced a new victim, this time in Oman. The target is Special Oilfield Services Co, LLC. No representative has commented on the breach, so it’s unclear how the ransomware attack has been handled.
- According to Lockbit’s OP, the victim got 2 days at their disposal to make contact with the hackers and begin negotiations
- If the hackers’ terms are not met, they will leak the stolen data publicly
- Lockbit is currently the most powerful, active, and infamous ransomware group in the world
- The ransomware gang was targeted by the FBI itself in February 2024 during Operation Cronos
Operation Cronos represented the culmination of months of stalking and gathering information about the hackers and their associates. Unfortunately, the operation ultimately failed shortly after the FBI announced its seizure of Lockbit’s website.
Lockbit went back into business merely days later, regaining control of its assets and attacking none other than the FBI itself in response. This alone shone a light on the gang’s power, resourcefulness, and intimidation factor.
Since the failed operation Cronos, Lockbit has returned in full swing, operating at the same level as before. Lockbit operators are extremely effective and make no compromises during negotiations. Which is why many victims refuse to negotiate.
This will invariably lead to the hackers leaking the stolen data publicly. Which, in turn, will lead to even more breaches in the foreseeable future, often sooner than later.
But is there a way to prevent that without paying the ransom?
How Lockbit Hackers Operate
Lockbit isn’t exceptionally versatile, as it prefers to stick to the tried-and-tested ransomware methods. This involves relying on the double-extortion technique to gain as much leverage as possible during negotiations.
The hackers will both encrypt the victim’s system and steal sensitive data to blackmail the target. This double-trouble approach allows the hackers to demand higher-than-usual ransoms, sometimes nearing or exceeding $1 million.
If the victim pays, the hackers will provide the decryption key and delete the stolen data. Or so the story goes. As cybersecurity experts warn, that’s usually not the case. While the hackers will provide the decryption key, there’s no guarantee that they will delete the data.
In fact, they most likely won’t. Most ransomware gangs either keep the data for themselves for later use, leak it publicly in closed circles anyway, or sell it to other cybercriminal rings. These will then use it for their own goals.
Goals which extend from blackmail to spying to hacking either the target company or its clients. The conclusion is simple: ignore the calls for negotiations. Specialists recommend a no-negotiation policy which naturally implies accepting the consequences.
The hackers will leak the stolen data, which means that the victim will incur some reputational damage. But it beats having that and losing a lot of money on top of that. As to the hackers’ preferred targets, Lockbit doesn’t necessarily discriminate.
The operators will always follow the money trail and typically coordinate their operations so that they produce the most profit. If you feel like you have a lot to lose financially or reputationally, you might want to act sooner rather than later.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

