Lockbit Travels to China
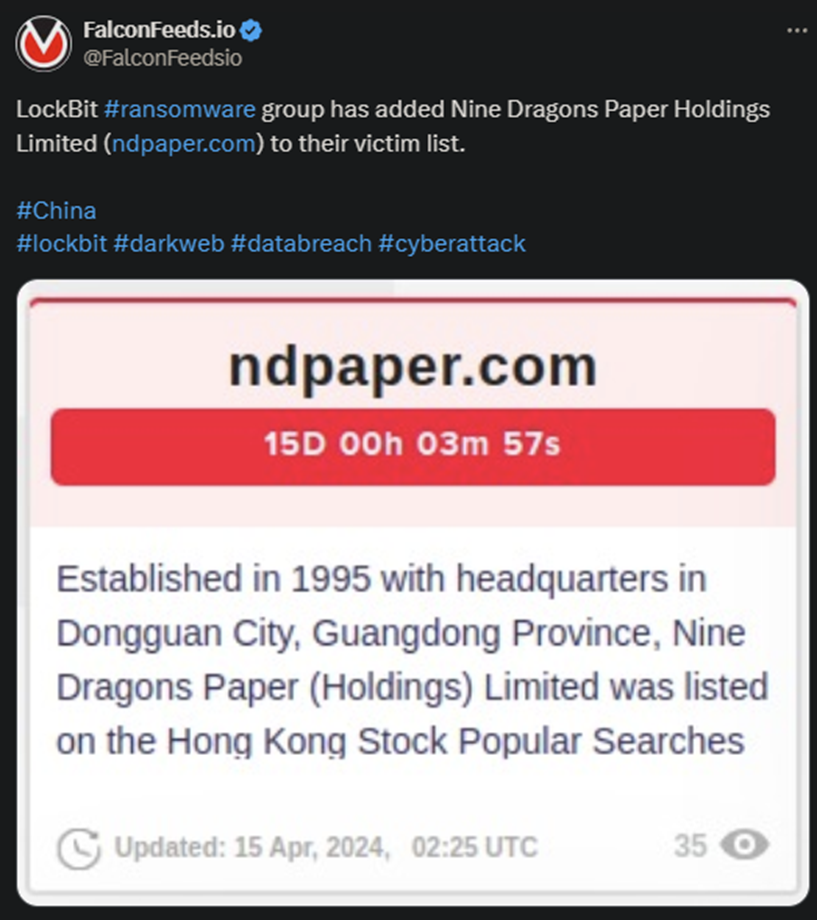
LockBit hackers announced that they’ve breached a Chinese company by the name of Nine Dragons Paper Holdings Limited. The enterprise has been formed in 1995 and ranks as a high-value target for the hackers.
- According to LockBit’s post, the victims got a 15-day time limit to contact them for negotiations
- It’s unclear at this moment what the victim company has decided, and no representative has come forth with a public statement yet
- LockBit is currently the most infamous, dangerous, and resourceful ransomware gang in the world
- LockBit hackers have produced so many victims globally that they eventually attracted the attention of the FBI
The law enforcement agency attacked LockBit earlier this year and managed to seize the organization’s website and assets. The success was short-lasted, as LockBit operators regained access to their systems only several days later.
They then targeted the FBI itself in response to make a statement and showcase their resilience and fearlessness. Operation Cronos wasn’t a total failure, though, as it managed to shed light on the gang’s structure, MO, and tools.
As the FBI specialists showed, LockBit’s 4.0 version was already in advanced stages of development at that time.
FBI’s efforts also revealed over 2,000 high-profile victims and more than $121 million in ransom gains. This alone speaks volumes about LockBit’s level of development and success.
This latest breach falls in line with LockBit’s usual MO. The target is high-value, packing substantial revenue and most likely having a lot to lose. Whether Nine Dragons decides to negotiate with the hackers, though, remains to be seen.
Why LockBit Is a Real Threat
LockBit isn’t necessarily ahead of the game in terms of general tactics. The gang relies on the same tried-and-tested phishing techniques which work wonders on uneducated victims. But they also target specific institutions directly.
They have the means and know-how to do it. In other cases, LockBit operators may infect legitimate apps, software, and public-service websites to create traps.
But LockBit’s true power comes from its code and intricate tools. The organization relies on the double-extortion practice to create as much leverage during negotiations as they can. The victim needs to pay for both the decryption key and the deletion of the data.
As FBI’s operation showed, many victims are unable to circumvent the lockdown without the decryption key. This can lead to massive data losses and logistical problems. Which is why some decide to pay the ransom and get it over with.
Which, as cybersecurity experts point out, is not a solution anyway. First, because paying the ransom doesn’t guarantee that the hackers will keep their word and delete the data. More often than not, they won’t. Instead, they will keep it for later use.
Or sell it to other cybercriminal gangs.
Secondly, because paying the ransom, or even just negotiating with the hackers, automatically marks you as vulnerable. This puts you on the hackers’ list so they know that you’re fair game for future attacks.
They also won’t shy away from spreading that information around.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

