Medusa Ransomware Bites Again
MEDUSA operators announced another successful breach, this time against the US-based Traverse City Area Public Schools. This is a massive operation against a school district with 10 elementary schools, 2 middle schools, 2 high schools, 1 alternative high school, and 1 Montessori school.
- The district also serves approximately 8.908 students and works with 932 employees
- This operation ranks among the biggest and most rewarding MEDUSA has conducted recently
- According to the hackers, the operators managed to steal approximately 1.2 TB of data, but it’s unclear what the leaks contain
- None of the victims involved in the incident have come forth with a public statement, but one may come at a later date
MEDUSA is known for being a stealthy and dangerous gang with knowledgeable operators and high-end tools and tactics. The organization doesn’t shy away from targeting high-profile institutions, whether they are public or private.
The hackers only follow the money and rely on the double-extortion method to intimidate and coerce the victims into paying. Unlike other ransomware groups, MEDUSA offers the victims several payment methods.
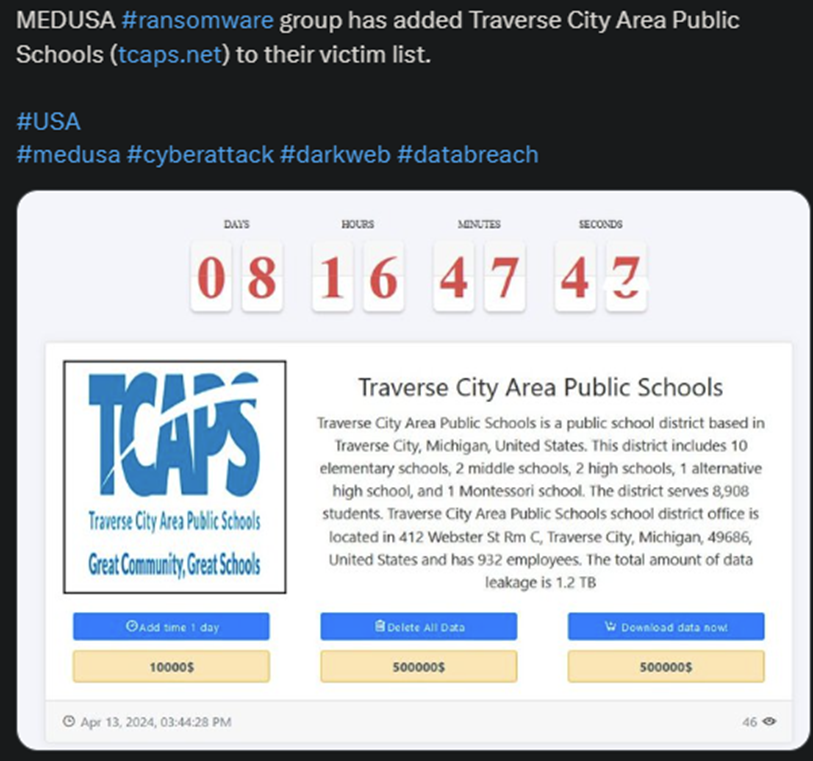
The hackers always post a summary of the victim, the countdown timer, and 3 different payment options for the victims to consider. These are the options to add another day to the counter, delete all the data, or download the data.
The price for each option varies, depending on the victim’s profile, its revenue, and the amount of data stolen. In this particular operation, MEDUSA operators gave the School District quite the spicey options.
The victims can pay $10,000 to add another day to the counter and $500,000 whether they want to delete or download the data. $500,000 for each, of course.
Medusa Ransomware Bites Again
MEDUSA is a little over a year old, yet it’s managed to amass an impressive amount of high-end victims. The organization is well-structured and operated and relies on a lot of affiliates to increase its profits. This also increases its stealth factor considerably.
The gang is known to be very blunt during negotiations and sometimes demand absurd ransoms. But the thing that makes the group so dangers is the main MO. Unlike many other ransomware actors, MEDUSA doesn’t necessarily rely on phishing emails.
Instead, it relies on vulnerable apps and services or manually hijacking legitimate accounts. Because the hackers use legitimate software for malicious purposes, MEDUSA’s activity is very difficult to track and flag.
This explains how the gang is able to sometimes steal massive amount of data from high-end actors from a variety of industries. Despite these advanced tactics, MEDUSA’s pay rate isn’t necessarily higher than that of other ransomware groups.
But the fact alone that the organization can breach global players with such ease and effectiveness raises an alarm signal. Plus, the victim doesn’t necessarily need to pay for the hackers to make a profit.
They can always sell the stolen data to other groups or exploit it some other way for their own gains.
This isn’t something you can control, but you can control whether will or will not negotiate with the hackers. And the best course of action is to reject any type of negotiation, because that can never lead to anything positive for you.
Only for the hackers.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

