MEDUSA Ransomware Bites One More
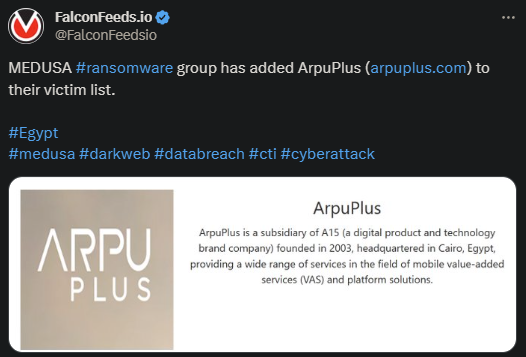
MEDUSA announced a new victim, this time located in Egypt. ArpuPlus is headquartered in Cairo and is a subsidiary of A15. This is a digital service provider founded in 2003 with an impressive database of customers.
- MEDUSA posted evidence of the attack on their public platform
- The attacker didn’t mention any details regarding the amount of data they secured, the value of the ransom, or the payment deadline
- ArpuPlus didn’t comment on the event and it’s unclear whether they’ve decided to negotiate with MEDUSA or not
- MEDUSA is a veteran in the ransomware sphere, with its first public appearance dating back to June of 2021
While MEDUSA isn’t as active as other ransomware organizations, the group displays a slightly unique attack pattern. Its main victims, approximately 34%, are in the US, but MEDUSA has a global reach.
According to the most recent statistics, MEDUSA’s victims are spread across the globe, including France, Turkey, Australia, Singapore, UAE, Canada, India, etc. MEDUSA attacks pretty much indiscriminately, as it targets all industries it can access.
However, the organization is not reckless and often plans its attacks with great care. This is to improve the chance of successful breach and to secure as much valuable data as possible. This will give MEDUSA a lot more leverage during negotiations.
An important aspect of MEDUSA’s MO is its predilection for targeting major public and private corporations. One such attack took place against the Minneapolis School District in March of 2023, when MEDUSA asked for $1 million in ransom.
The school refused to pay, so MEDUSA leaked the stolen data publicly.
What to Know About MEDUSA
MEDUSA first appeared on the public’s radar in June of 2021 and had a slow, but steady growth ever since. The organization is pretty much opaque, so nothing is known about its structure, internal organization, members, or finances.
What is known is that MEDUSA doesn’t rely on its own power and abilities to set up its ransomware operations. Instead, it employes affiliates and cooperates with other ransomware and cybercriminal organizations to expand its reach and influence.
To stay true to its name, MEDUSA employes a multitude of attack strategies to overwhelm and confuse its victims. This qualifies the organization as highly resourceful, knowledgeable, and adaptable and explains its impressive reach and resilience.
One of MEDUSA’s trademark signs is its outstanding pool of file extension it uses. The main one is .MEDUSA, as was expected, but there are numerous others worth mentioning. These include .1btc, .myloc, .key1, .readinstructions, and many others.
MEDUSA operates based on the double-extortion tactic, encrypting the victim’s files and copying and downloading as much sensible data it can get. The attacker will then threaten with public exposure unless the ransom is agreed upon.
Typically, MEDUSA doesn’t demand extreme ransoms, to make sure that the victims afford to pay. The organization typically remains bellow $500,000, but ransoms can skyrocket above $1 million in some cases.
No matter the value of the ransom, experts advise against paying it, because doing so incentivizes the attacker to stay in business.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

