MEDUSA Ransomware Infiltrates Canadian Furniture Manufacturer
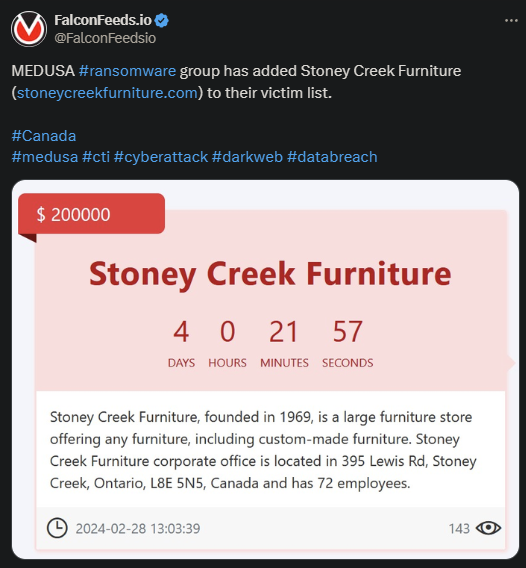
MEDUSA ransomware announced another successful hacking breach against a reputable Canadian furniture manufacturer and provider. Stoney Creek Furniture, founded in 1969, has 4 days left to meet the hackers’ demands.
- MEDUSA gave the victim a week to contact them for negotiations
- It’s unclear whether Stoney Creek Furniture submitted to the attackers’ demands or they decided to ignore them
- MEDUSA is known to be a tough negotiator that often demands obscene ransoms
- The infamous ransomware ring has also increased its activity considerably since the release of their TOR website
Unlike other ransomware actors, MEDUSA displays a detailed view of each of their operations. This includes:
- The countdown to the public release of the stolen data
- The price tag with the ransom demand
- A short brief about the victim, its activity, and revenue
- The date of the attack
Experts have pointed out that MEDUSA has increased its activity following the release of their new TOR portal. This coincides with a general increase in ransomware activity among most ransomware actors.
MEDUSA currently ranks as a dangerous, cunning, and blunt organization with strict MOs and tactics. The group offers almost no wiggle room during negotiations, partly because the hackers have done their homework.
MEDUSA almost always relies on premeditated strikes, rather than shooting arrows in the dark, which is what smaller ransomware groups tend to do. The spray-and-pray method is good for attacking targets in bulk, not as effective for securing actual results.
The Story of MEDUSA
MEDUSA often gets conflated with MedusaLocker, which is a different organization. MedusaLocker emerged in 2019, whereas MEDUSA has been active since late 2022. The 2 showcase name similarities, but nothing else.
Despite hitting the public eye in 2022, MEDUSA didn’t really showcase its true potential until early 2023. This coincided with the release of its TOR blog and visible upgrades in the group’s tactics.
One such notable upgrade refers to the use of the living-off-the-land infiltration method. This refers to using legitimate software to mask its venomous fangs and infect regular users who could not suspect anything.
Not only is this method stealthier and more reliable than operations based on direct targeting, but it’s also more difficult to flag. This explains why MEDUSA is so effective and so notoriously challenging to predict.
It’s important to note that MEDUSA also relies on the double-extortion technique. This means that the hackers who access your system encrypt the data and steal everything they can. The value of the ransom will increase considerably because of it.
That’s because the victim then needs to negotiate both the decryption key and the deletion of the data. However, experts warn that paying the ransom doesn’t guarantee either outcome.
Ransomware actors typically provide the decryption key, but the victim doesn’t have any guarantees that they will also delete the stolen data. The hackers may simply pass it on to affiliate ransomware groups instead.
This will eventually lead to additional extortion demands later on, sometimes months after the initial breach. To prevent that, the specialists’ recommendation is to ignore the attackers, take the loss, and work on one’s security to prevent the event from repeating in the future.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

