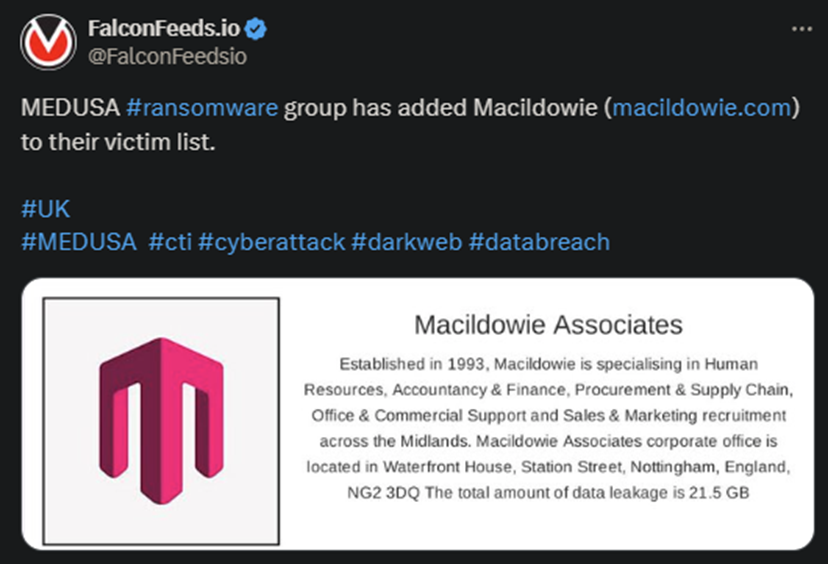
MEDUSA Ransomware Targets UK-Based Victim
The MEDUSA hackers announced another operation against a UK-based victim. The target is Macildowie, a specialist in accounting, marketing, sales, and finance. According to the attackers, the breach resulted in a data leak of a little over 21.5 GB.
- MEDUSA is a Ransomware-as-a-Service (RaaS) platform that emerged in late 2022
- The organization caught wind fast and grew extensively during 2023 as the hackers polished their tactics, tools, and primary MOs
- The victim mentioned in the leaks didn’t comment on the breach, which is typical with most attacks
- The news about the attack didn’t mention any specifics about the operation, despite MEDUSA being known to offer quite a few
Unlike other ransomware actors, MEDUSA operators like to do everything as transparently as possible. They will provide the victim with clear-cut deadlines and even mention the value of the ransom in their news post.
The victim can either pay the ransom directly, or contact the hackers for negotiations, although that doesn’t guarantee anything. Then again, paying the ransom directly doesn’t either. Which is why most experts advise against it.
MEDUSA operators usually provide their victims with several options aside from the one to pay the ransom itself. Another option is to extend the deadline, which comes with a standard fee of $10,000. The victims can also request the deletion of the data.
Or download it themselves in case they see it as extremely sensitive and vital. Both of these options come with hefty prices, usually depending on the victim’s profile and projected revenue. To be noted: these are options are separate from the ransom itself.
How Dangerous Is MEDUSA?
The organization took off during 2023 and has listed quite a few high-profile victims so far. As a general rule, MEDUSA operators prefer to target medium-size businesses, but they don’t shy away from going big either. The group is definitely capable and dangerous.
An interesting fact is that MEDUSA appears to have a more visible online presence than other gangs. Aside from the leak site itself, the group also has Telegram and X (Twitter) accounts where they market their services (RaaS) and post leaks.
A public post dating back to 25th of November, 2022, stated that OP (an anonymous individual) even discussed firsthand with one of MEDUSA’s PR persons. The person in question revealed video information about the gang being involved in casino fraud.
The legitimacy of the post itself is uncertain, especially since the poster appears to praise MEDUSA’s PR and mass-media team. It’s not difficult to image that the hackers themselves produced it as a way of increasing reputation and public acknowledgment.
When it comes to the preferred industries, MEDUSA prioritizes several sectors. These include high technology, education, manufacturing, healthcare, and retail sales. The hackers always prioritize stealth and fast data exfiltration.
The gang is clearly competent and appears to evolve as time passes.
As to what you should do in the eventuality of a MEDUSA attack, the solution is simple: don’t negotiate. If you can recover your data without negotiating with the hackers, do that. If not, give it up.
This may be easier said than done, obviously, because not all victims can stick to this rule. But it’s worth understanding that paying the ransom does nothing but keep the hackers in business.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

