Modern Medusa Ransomware Bites Into 2 More Victims
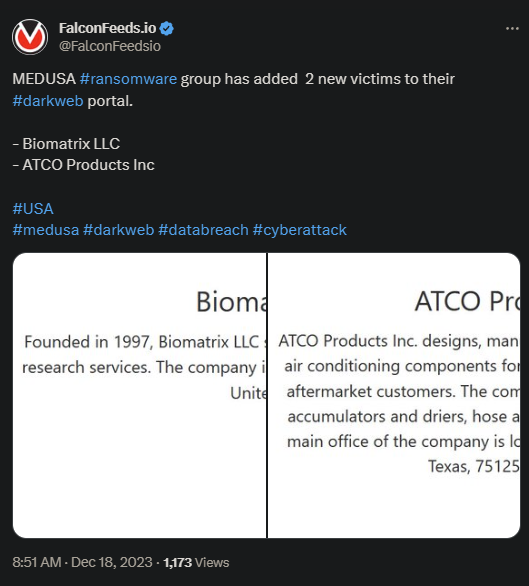
MEDUSA ransomware group hits 2 new US companies, Biomatrix LLC and ATCO Products Inc. These old and reputable organizations have fallen victims to the ransomware attack recently, but details are not known about the aftermath.
- Biomatrix LLC specializes in biomedical and clinical services and dates back since 1997
- ATCO Products Inc is an automotive air conditioning manufacturer, specializing in parts, original equipment, tools, and everything related to the industry
- MEDUSA attacked the two in a rapid succession and posted evidence of the breach on its public website
- The attacks were financially motivated, as is the case with all ransomware attacks
The MEDUSA ransomware group isn’t new. The organization first became active in 2019, but it sustained numerous upgrades along the way. This type of adaptability allowed the group to remain anonymous and protect its assets from identification.
The group’s original name was MedusaLocker and operated as a RaaS (ransom-as-a-service) model. The organization’s main targets operated in the healthcare and educational sectors, but other business profiles fell victims as well.
Despite being a relatively old threat, MEDUSA spiked its activity only recently. 2023 qualifies as the most active and profitable year, as the group performed several high-profile hits.
The MOs employed consist of a mix of brute force, phishing, and vulnerability exploitation, allowing the group to adapt to its victim’s defense profile. More importantly, MEDUSA always upgrades its assets, allowing it to circumvent most defensive systems.
How MEDUSA Operates
One of the strengths of MEDUSA is its ability to improve and stay connected to the massive and intricate network of worldwide cyber-threats. It’s been pointed out that MEDUSA keeps tight connections to several global hacktivist groups.
This allows the org to keep a low profile and expand its sphere of influence in areas that would normally be unreachable. The main MO is almost identical in most cases.
MEDUSA infiltrates the system, employs PowerShell to erase data backup and prevent data restoration, and deactivates the main defense systems. Ultimately, it encrypts the data available and disrupts the victim’s operations.
Ther main file extension is .MEDUSA, but other file extensions may be observed, such as exlock, NTlock ransomware, Keversen ransomware, skylock, and many others. These are due to MEDUSA’s numerous iterations and variants available.
The best method of defense relies on a complete overhaul of the entire firewall system. Someone with obvious vulnerabilities and a lot to lose should rely on specialists to upgrade their systems and boost their defenses.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

