Newcomer Arcus Media Ransomware Targets 3
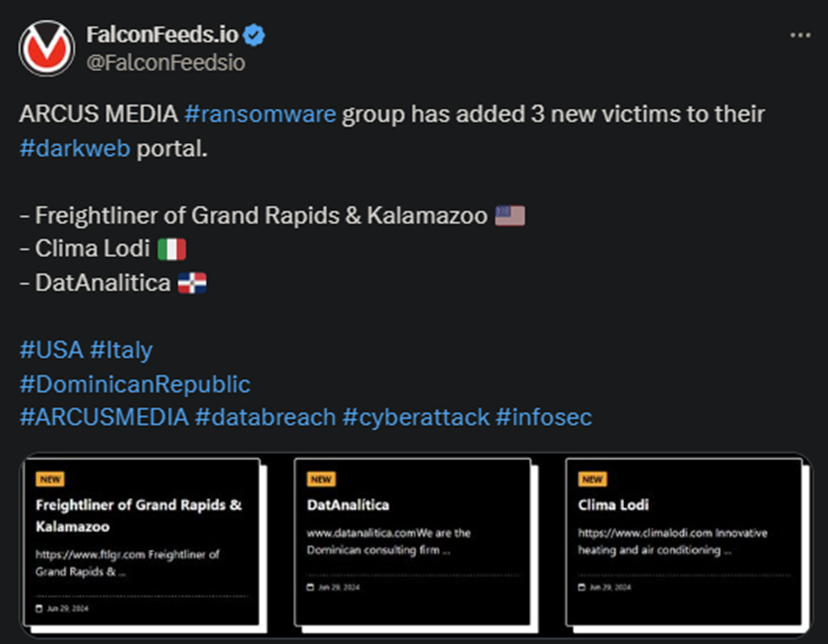
The Arcus Media hackers have announced 3 more victims on the 29th. These are Freightliner of Grand Rapids & Kalamazoo from the US, Clima Lodi from Italy, and DatAnalitica from the Dominican Republic.
- The hackers didn’t post any relevant information about the breaches aside from short summaries of those attacked
- Neither of the victims has commented on the situation, which most likely indicates that the negotiations haven’t been finalized
- Arcus Media first came public in May of the current year and has already produced 6 victims since its inception
- The Arcus Media hackers appear to conduct targeted attacks rather than going for the typical spray-and-pray
Given the gang’s recent emergence, there is little-to-no information about its structure, members, preferred industry and target type, or any other aspect. While the group first reached the public sphere in May, they didn’t hit their first targets until June.
The first week of June saw Arcus Media producing no fewer than 6 victims. These come from different industries, mainly manufacturing, services, real estate, construction, and health. The hackers also appear to exfiltrate a lot of data.
Currently, Arcus Media advertises itself as a RaaS (Ransomware-as-a-Service) service and has a TOR website where they post their leaks. The attack method typically revolves around phishing emails because it’s cost-effective and gets the job done.
Regarding the negotiations, there’s little information to be worth with. The hackers conduct the negotiations on their TOR platform but it’s unclear if they’ve had any successful ones. Some of their victims include:
- Langescheid GbR
- Franja IT Integradores de Tecnologia
- Duque Saldarriaga
- BHMAC
- Botsello Mills Ltd.
What to do in Case of a Ransomware Attack?
Arcus Media is just another example that shows how prolific and active the ransomware sphere is. Ransomware actors have grown more competent and active over the past year, producing more victims than even before. And the trend doesn’t appear to slow down.
So, in the unfortunate case that you become a victim, what should you do? The answer is simple: move on. Don’t negotiate, don’t pay the ransom, don’t even contact the hackers. As cybersecurity experts explain, paying the ransom does nothing for you.
On the contrary, it has more negative than positive effects. Sure, you will get access to your system, but that’s not the only reason one pays the ransom. High-level targets with a lot of sensitive data are also interested in having the stolen data deleted.
That’s the main reason why they pay the hackers. Unfortunately, there’s no guarantee that the attackers will keep their word and delete the stolen data. In many situations, they prefer to either keep it to themselves, sell it, or share it with other cybercriminal gangs.
Plus, paying the ransom marks you as a vulnerable target. So, you’re more likely to be targeted again in the future.
The standard recommendation is to ignore any type of contact or communication with the hackers and look for other avenues to fix the problem. The hackers will most likely leak the data on the Dark Web, but that’s likely to happen whether you pay the ransom or not.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

