NoName and Russian Cyber Army Attack Romania Again
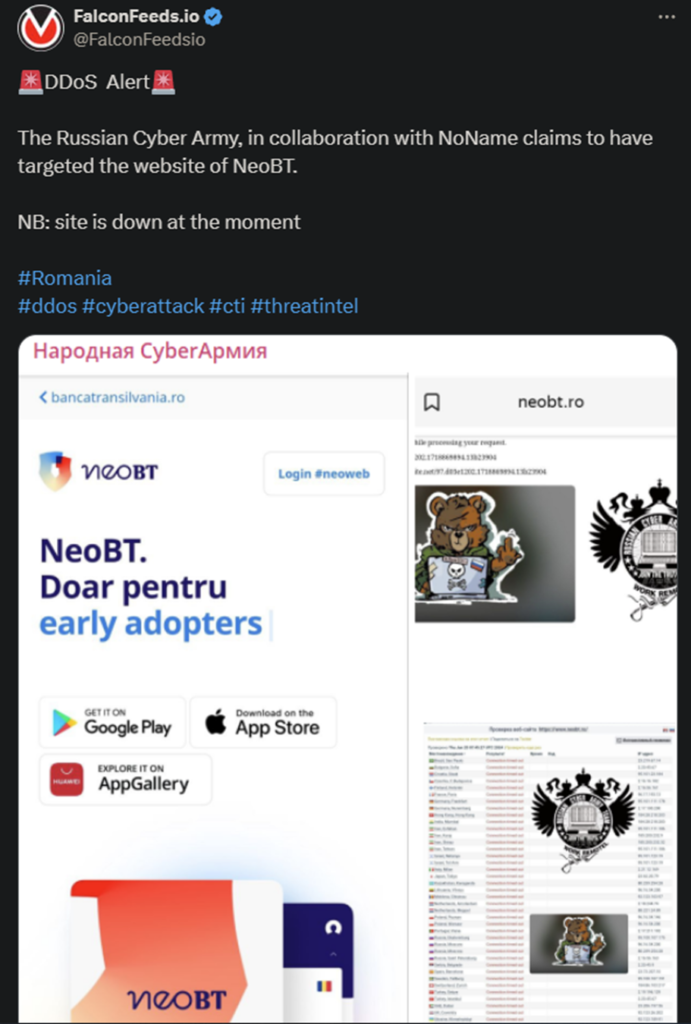
Russian Cyber Army has announced another notable operation against one of Romania’s public banking services, NeoBT. This attack comes after several others that have been perpetrated by NoName.
- Russian Cyber Army published the news about the attack on their public platform, mocking the country’s cybernetic defenses
- The attack has been motivated by Romania’s support for Ukraine in the ongoing war
- NoName has targeted the country multiple times, both recently and in the past
- The pro-Russian cybercriminal gang is deeply invested in protecting Russia’s goals and interests
This recent attack was aimed at Transilvania Bank, more specifically at their online banking service, NeoBT. It’s unclear what type of damage the hackers have inflicted, but the bank’s website was down at the moment of writing this article.
Russian Cyber Army has often collaborated with other pro-Russian gangs, like NoName, to target more prominent institutions. Politically-driven attacks, such as this one, usually target public, state-owned institutions, but that’s not always the case.
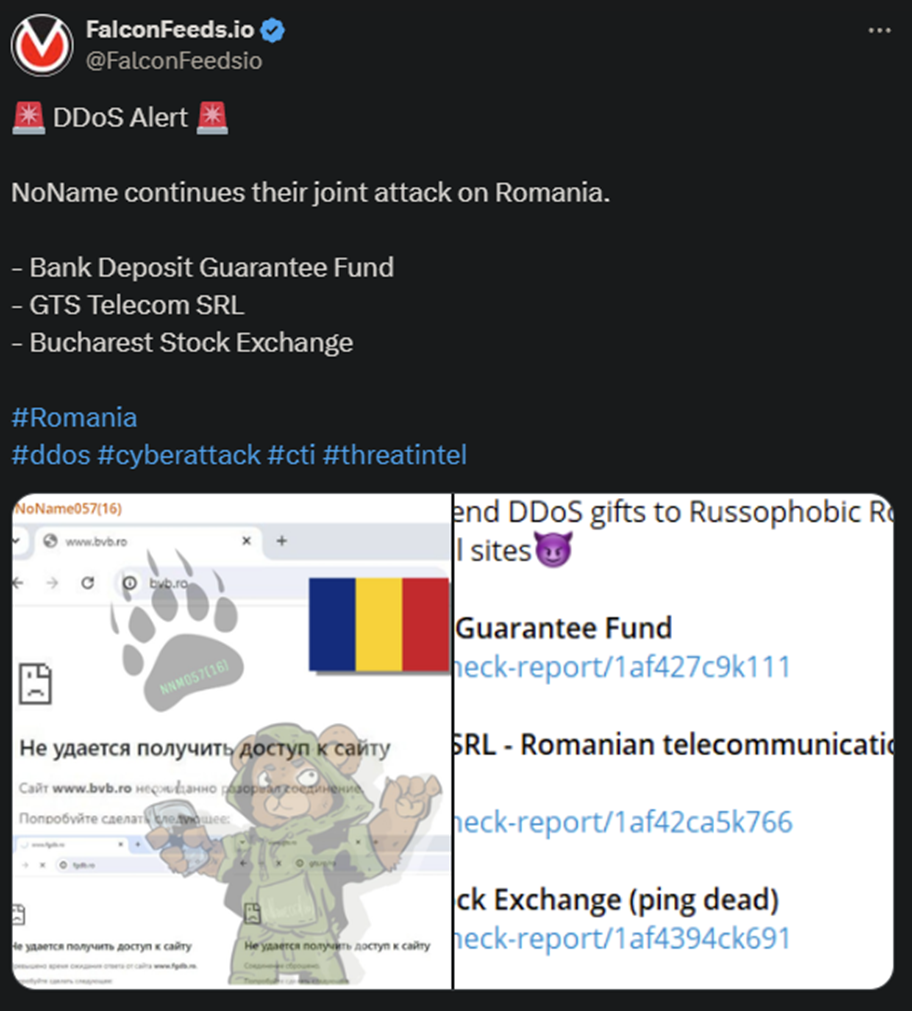
This attack comes one day after another that targeted Romania’s institutions. The last one took place on the 19th and targeted 3 institutions. These were the Bank Deposit Guarantee Fund, GTS Telecom SRL, and the Bucharest Exchange Stock.
At that time, NoName mocked “Russophobic Romania”, announcing that more hits are to follow.
The attacks haven’t been particularly invasive, as organizations like NoName focus on quantity rather than quality. The gang aims to target as many institutions as possible to spread their message and cause doubt and fear.
NoName’s goal is to impact Ukraine’s ability to resist the Russian advances on the war front. To that end, the hackers rely on DDoS hits against both Ukraine and its allies.
Who Is NoName?
The identity of the group is unknown at this time, which already speaks volumes about the organization’s proficiency. NoName has been active since February, 2022, when Russia first invaded Ukraine.
The gang has conducted numerous operations since, usually multiple per day. In some cases, the hackers have managed to breach a dozen targets per day, sometimes more. That’s by design, as the hackers have daily quotas to meet.
According to an anonymous source, NoName hackers have strict deadlines to fulfill. They are supposed to identify, attack, and breach between 5 and 15 targets per day, preferably as close to the latter as possible.
The organization also appears to have an almost military-like structure, operating with precision and impunity. Some have suggested that the gang is directly funded by the Russian government. This would explain why NoName doesn’t appear interested in financial gains.
This theory hasn’t been confirmed yet.
Whatever the case may be, NoName appears motivated, resourceful, and capable enough to carry on its cybercriminal activities uninhibited. It also seems as the gang has recently shifted to a more decentralized operating model.
This allows the organization to resort to a more unorganized MO and a looser internal structure. The goal is to make it more difficult for law enforcement agencies to pinpoint specific members and infiltrate the group.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

