NoName Attacks 5 More Targets
The NoName hackers announced another massive operation stretching across 3 countries, Netherlands, Italy, and Germany. The hackers justified the attacks by accusing the 3 nations of supporting Ukraine in the ongoing Ruso-Ukrainian conflict.
- All 3 nations have provided Ukraine with military and humanitarian support, sending UAVs, weapons components, military equipment, and resources
- NoName sees these actions as statements of war, given the gang’s open pro-Russian sentiments
- It’s unclear how effective the cyberattacks have been, but NoName published evidence of the neutralized websites
- The cybercriminal group is known for pushing political and ideological propaganda
It is likely that the 5 victims have restored their systems since NoName’s attacks aren’t usually too severe. The gang values quantity over quality, which is why it prefers to hit multiple targets lightly rather than spend resources on one highly impactful operation.
NoName’s goal is primarily to intimidate and discourage its targets from supporting the Ukrainian government. The gang often spends a week or more conducting multiple operations against the same governmental body.
The latest such operation was against Spain, which lasted 6 days of relentless attacks.
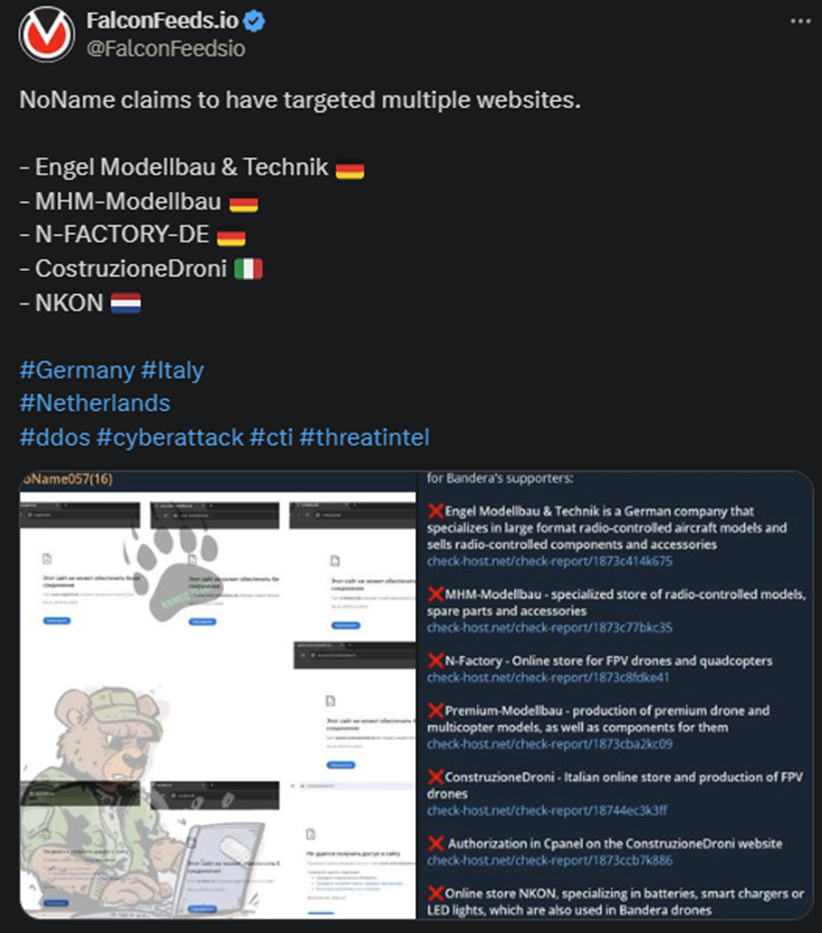
NoName’s MO hasn’t changed since the beginning of the Ruso-Ukrainian conflict. The gang has always targeted pro-Ukrainian companies and institutions, prioritizing those who support Ukraine’s war efforts directly. This appears to be the case with today’s attacks.
The hackers can also target those who merely announce support packages even before these being actually delivered. NoName operators have attacked multiple governments and private corporations since March 2022, when they first came public.
What Do We Know About NoName?
The most obvious thing we know about NoName is that it shows pro-Russian sympathies and is fully invested in the destruction of Russia’s enemies. Other than that, there is no clear information on the gang’s structure, members, assets, or anything else.
The gang appears to be very well funded and influential, often managing to breach high-security targets. The primary MO isn’t necessarily ground-breaking. NoName typically relies on DDoS missiles to flood the target website with bot requests.
This is usually enough to overwhelm the targeted system and take the victim’s services offline. The fallout isn’t usually too severe, as most victims manage to bounce back fairly easily. But that’s by design because NoName prioritizes quantity over quality.
The gang’s goal isn’t to deliver crippling blows, which may require time and resources and may expose the group. Instead, it aims to pound the targets with short, but effective strikes, damaging enough to send the intended message.
That being said, NoName is a versatile, adaptable, and resourceful organization with several aces up its sleeves. The gang is known to use a multitude of tools to achieve its goals. These include intimidation, mocking, sending threatening letters, pushing propaganda, etc.
More importantly, NoName relies on affiliates to conduct flash operations against vulnerable targets. This increases the gang’s spread and influence with minimal investment, without exposing its members directly.
The group is also known to collaborate with other pro-Russian cybercriminal entities like XakNet and KillNet for the same reasons. This allows the hackers to infiltrate multiple targets across several countries at once.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

