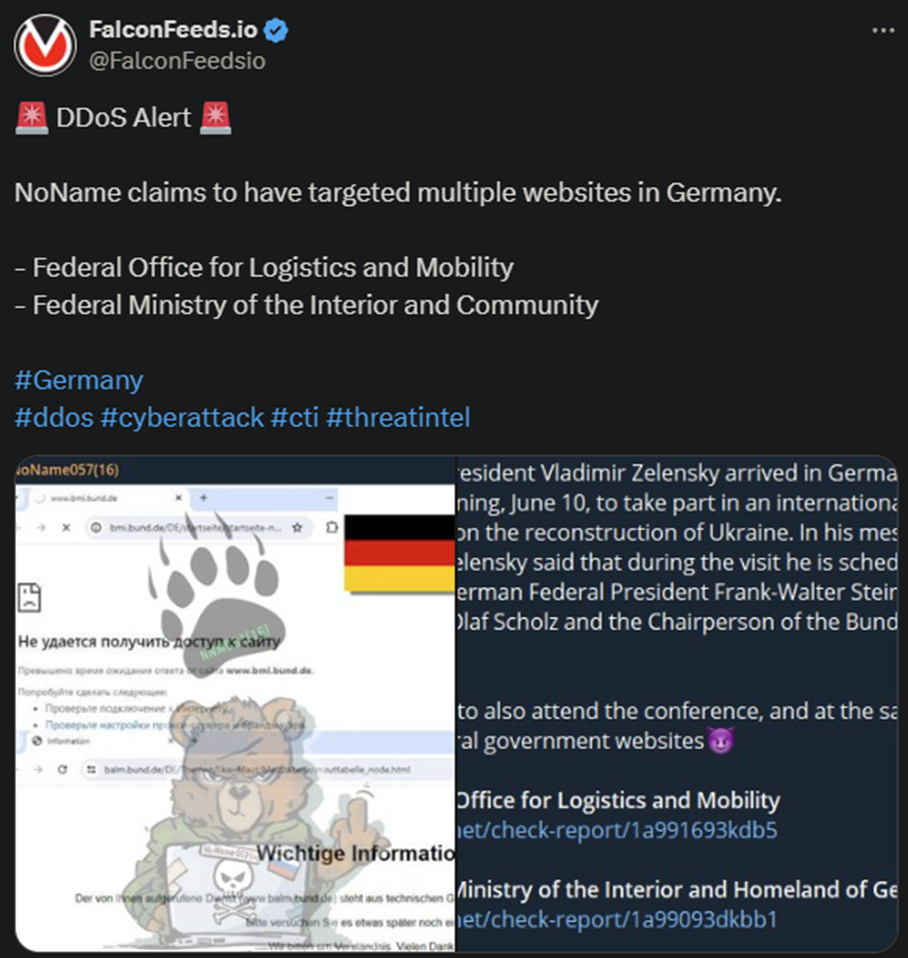
NoName Attacks Germany Following Zelenski’s Visit
Infamous hacker group NoName announced a coordinated attack against German targets earlier today. The attack was motivated by Zelenski’s visit that took place on the 10th of the current month.
- NoName has been the most vocal and active anti-Ukrainian entity since the beginning of the Ruso-Ukrainian war
- The organization consists of pro-Russian hackers who have made it a norm to attack Ukraine’s allies consistently
- NoName has been conducting multiple attacks per day for over 2 years already
- Today’s attack targeted the Federal Office for Logistics and Mobility and the Federal Ministry of the Interior and Community
Germany hasn’t released any public statement yet, given that attacks like these have become a norm lately. NoName has been targeting Ukraine’s allies relentlessly, often relying on affiliates and other hackers to inflict even more damage.
NoName’s attacks aren’t particularly damaging because they’re not meant to be. The organization focuses on quantity over quality. The goal is to target as many public institutions as possible as often as possible.
This level of activity naturally impacts the gang’s ability to inflict serious damage, although it has happened before.
NoName relies on DDoS attacks to intimidate their targets and send a message. The message is consistent in all cases: “Stop supporting Ukraine.” The hackers prefer to prioritize states and organizations that support the Ukrainian government actively.
This refers to them sending military and humanitarian packages, as well as direct funds. Next in line come those who have promised aid packages but haven’t delivered yet. NoName has targeted multiple countries multiple times since its inception.
How DDoS Attacks Work
DDoS attacks are fairly simple, both in theory and in practice. The attack is mostly automated, as it relies on flooding the target website with requests. This is done via millions of bots that will soon overwhelm the system, causing the site to crash.
In most cases, the target website will recover fast, typically within minutes or hours at most. But in some situations, the attacks can be more debilitating, causing more long-term damage.
NoName relies on DDoS attacks primarily but has often resorted to other tools as well. These include intimidation, public mocking, threats, data stealing, doxing, and even sending threatening letters to media officials.
NoName’s goal is to control the anti-Russian narrative and impact Ukraine’s ability to withstand Russian aggression. The gang has often conducted numerous DDoS campaigns for days or even weeks, pounding the same target.
This has been the case with Moldova in the past, which NoName targeted for more than 2 weeks, almost daily. Despite the attacks not being particularly damaging, the cumulative effect can create a visible impact.
It’s important to note that, despite its high activity and determination, it doesn’t seem that NoName’s actions have had any meaningful political effect. Ukraine’s allies are still pushing forward dealing with NoName, and other pro-Russian hacker gangs, along the way.
That being said, NoName remains a global threat with a worldwide reach and plenty of resources to spare.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

