NoName Targets Multiple French Companies
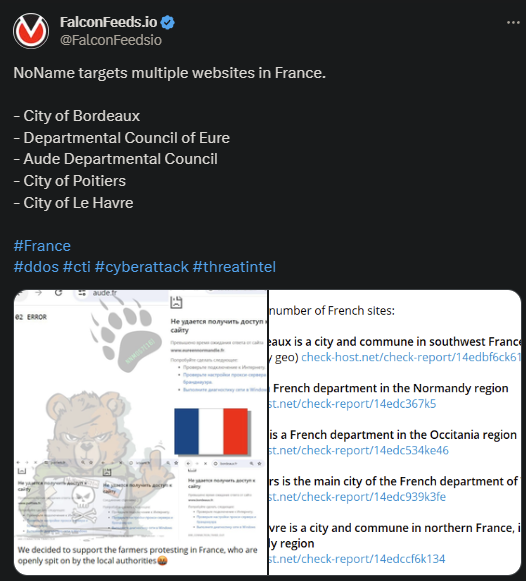
France found itself at the losing end of a cyberattack spree initiated by NoName recently. Several public entities were hit, located in different French cities.
- The institutions affected by the attacks didn’t comment publicly on the events
- NoName is known to use cyberattacks, threats, and intimidation to make political and ideological statements
- As stated by the organization itself, the reason for the recent attacks is France’s attitude towards the farmers’ protests
- NoName stands with the farmers and used the recent string of attacks to target the French public system
As NoName stated on its public Telegram channel: “We decided to support the farmers protesting in France, who are openly spit on by the local authorities.” This falls in line with the organization’s political and ideological identity.
NoName uses its power and influence to push its political agenda, which, until now, resumed to supporting the Russian government. The group has openly stated its support for Russia since its inception and attacked all those who opposed Putin.
However, the recent attacks don’t follow the same pro-Russian trend, as the farmers’ protests have nothing to do with Russia’s political climate. This may indicate the fact that NoName may become involved in other political affairs on a global scale.
Who Is NoName?
NoName is a pro-Russian hacktivist group that hit the public stage in March of 2022, at the beginning of Russia’s invasion of Ukraine. The organization immediately pledged allegiance to Putin’s regime and swore to destroy all those who oppose it.
Naturally, the first wave of attacks was directed at Ukraine, which spiked rapidly during the first months of war. DDoS infiltration and exploitation became the norm, with NoName hitting both public institutions and private corporations.
As stated by the organization itself, the goal is to spread terror and paralyze the financial and military capabilities of Ukraine and its allies. Which is why NoName soon turned its attention towards the US as well.
It’s important to mention that NoName currently ranks as one of the most dangerous organizations in the world. The group is highly adaptable, very well financed, and frequently cooperates with other organizations to improve its capabilities.
NoName constantly works with other hacktivist groups like Killnet and Xaknet to increase their success rate. The cybercriminal actor has also devised its own DDoS tool called DDOSIA, which it uses with great success today.
This paints the organization as very resourceful and well-funded, with some suggesting connections to the Russian government itself.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

