NoName Hits 5 Targets in Lithuania
NoName targets 5 companies in DDoS attack in Lithuania, causing significant financial and logistical problems. As with all NoName attacks, this too is politically motivated and technically aimed at the Lithuanian president, Gitanas Nauseda.
- NoName has made a name for itself in the field of DDoS attacks since March 2022
- The organization’s main prerogative is to attack any private or state entity that supports Ukraine or nurtures anti-Russian sentiments
- The recent attack was aimed at the Lithuanian government, following a recent public announcement in the Lithuanian press
- The announcement stated that Lithuania is preparing a $200-million help package for Ukraine
The attacks took place during a massive coordinated operation, as is typical with NoName activity. The organization is known to collaborate with other hacktivist groups like Killnet in an attempt to improve their success rate.
Despite being active for nearly 2 years, nothing is known about NoName’s internal structure, leadership, or members. This is evidence, to some, that NoName is actually funded by the Russian government, which gives it power, influence, and independence.
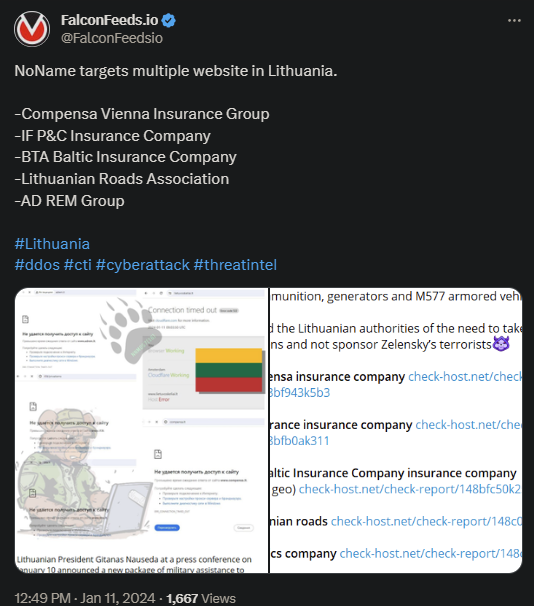
NoName posted evidence of the attack on their Telegram channel, stating Lithuania’s willingness to support Ukraine as the reason for the DDoS intrusion. The aftermath of the attacks is unclear, but it is presumed that the victims resumed their operations.
How Does NoName Operate?
NoName is a self-proclaimed pro-Russian hacktivist group that’s been active since late March of 2022. The group first became public with the Ruso-Ukraine war and immediately swore allegiance to the Russian government.
Since then, the organization has been targeting everyone they deemed as being pro-Ukraine or aiding the Ukrainian government in any way. Naturally, most of the early attacks aimed at Ukraine itself in the early phases, but quickly spread to other targets.
The US quickly followed, as well as numerous other governments like Latvia, Denmark, Germany, Norway, Poland, Finland, etc. The attacks usually targeted governmental institutions, but private entities were also among the victims.
As a result of the attacks, the victims’ online activity ceased until they could figure a way to resume their operations. NoName is notoriously aggressive and relies on intricate approaches to breach their victims’ systems.
A January 13th attack targeted presidential candidate of Czech Republic, general Petr Pavel, leading to the theory that NoName also aims to disrupt elections in specific countries. This holds sufficient water, seeing how NoName is politically and ideologically driven.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

