Peculiar 3AM Ransomware Infects 2
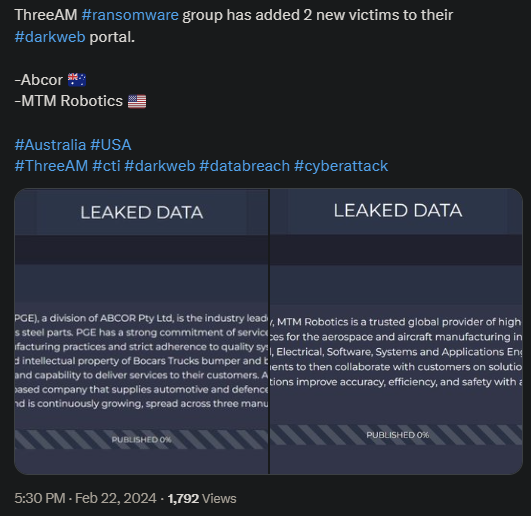
3AM ransomware posted evidence of their attack against 2 prominent targets. One is the Australian Abcor which specializes in metal production and parts assembly. The other is MTM Robotics, a global provider of automation and software systems.
- Neither of those involved in the attack have commented on the breach, so it’s unclear how the negotiations are going
- The attacks took place on the 22nd and 3AM detailed the victims’ profiles on their public platform
- 3AM relies on the double-extortion method to compel its victims into paying the ransom
- The 3AM actor itself has mostly functioned as a backup plan for failed Lockbit attacks
The latter suggests that 3AM is either an extension of Lockbit or that it’s a group made out of anonymous Lockbit operators. However, the recent dismantling of the infamous Lockbit and the fact that 3AM seems unaffected supports the theory that 3AM is its own actor.
The group also uses MOs, tools, and tactics that diverge from what Lockbit operators would deploy. The organization’s systems and tools are so out of the ordinary that they confuse rookies and experts alike.
The group relies on an outdated PHP script to monitor page views on their website, which is a strange preference. Especially since such a tool doesn’t save them any significant amount of money and doesn’t come with extra advantages either.
There are, however, some theories regarding the unusual choice. These include the fact that outdated software is more difficult to detect by modern security tools. They’re also simpler to use than their more complex modern counterparts.
Why 3AM Is Worth Keeping an Eye On
3AM isn’t as active as other ransomware organizations, but this doesn’t make it any less dangerous. While 3AM was previously used by Lockbit operators during failed Lockbit attacks, it has now become a self-sufficient ransomware actor with a visible print.
The organization employs multiple commands to paralyze applications, disable security systems, and disable backup processes to allow hackers to infiltrate with ease. This also permits the invaders to extract valuable data, which they will then use to extort the victim.
This complex attack pattern allows 3AM to infiltrate even the most well-defended targets. The operators also seem to conduct rather aggressive negotiation tactics.
The double extortion method also helps a lot in this sense, as it allows hackers to use extra leverage to force the victim into submission. Even so, most experts advise against paying the ransom.
On the one hand, it’s because you have no guarantees that the hackers will actually delete the stolen data. On the other hand because, even if they do, they might sell it to third-party cybercriminal groups first.
So, you might think that you’ve solved the problem, only for a new one to emerge several weeks or months later. It’s common for ransomware groups to sell or share stolen data between them.
This leads to multiple ransomware actors extorting the victim for the exact batch of data and the cycle never ends. Even so, the decision ultimately belongs to the victim, as some decide that paying the ransom is better than the alternative.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

