Qilin Ransomware Leaks Their Victim’s Data
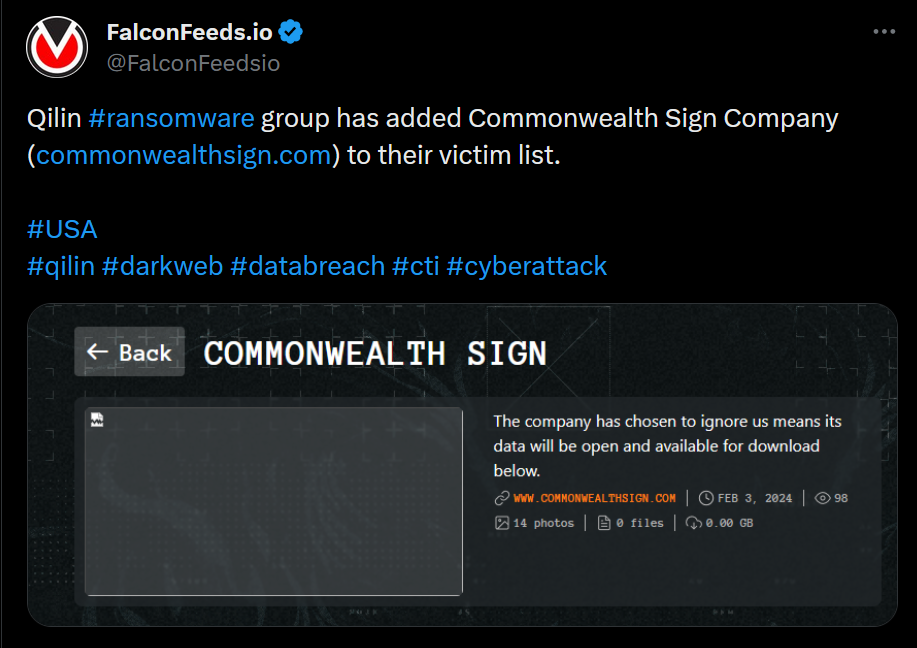
Qilin ransomware, also known as Agenda, announced a coordinated attack against Commonwealth Sign on February 3rd. The attack was successful, as the attacker managed to penetrate the victim’s defenses and steal important data.
- Despite the targeted ransomware breach, it is reported that the victim didn’t lose too much of its confidential data
- According to Qilin itself, the victim refused to contact the attackers to negotiate the terms
- As a result, the ransomware actor announced that it will leak the company’s confidential data publicly
- Qilin qualifies as a highly dangerous and resourceful ransomware actor that has grown in size over the past year
Unlike other cyberthreat actors, Qilin prefers to aim high. The group has a predilection for high-end targets and large enterprises with a significant financial potential. While most victims refuse to pay the ransom, some comply, which incentivizes Qilin to stay active.
Qilin’s main MO is the double-extortion method. The attacker encrypts the victim’s system and steals as much valuable data it can get. The victim then has to negotiate both the decryption key and the destruction of the cloned data.
This typically raises the value of the ransom considerably. Especially if the stolen data is particularly sensitive and the victim would like it out of the public’s eye.
Why Is Qilin a Menace?
The ransomware sphere has grown drastically over the past 3 years, with many new organizations trying to make a name for themselves. The most infamous ransomware actors are also highly adaptable and resourceful, rendering most defenses useless.
This calls for serious defensive improvements and constant updates and upgrades to keep up with the bad faith actors. And Qilin is among the top cyberthreats in terms of adaptability, resilience, and innovation.
Most importantly, Qilin appears to be specialized on infiltrating high-profile targets that have a lot to lose. This means that Qilin has a well-designed attack system with the latest tools and upgrades. The main methosd are phishing and spear phishing.
Interestingly, though, Qilin isn’t known to demand obscene ransoms, as is the case with more aggressive ransomware actors like Lockbit. Rather, Qilin remains in the range of $50,000-$800,000, with some occasional exceptions.
The organization also isn’t particularly active, as only 12 attacks have been attributed to its name between 2022 and 2023. This is presumably due to the profile of their victims who tend to be less accessible to standard ransomware actors.
Even so, Qilin is still a very potent threat and they appear willing to expand. Investigation groups have identified recruitment posts attributed to Qilin, who is actively looking for members and affiliates.
And with Qilin’s current profile, tools, tactics, and future, goals, there’s no telling where the organization will go. So, prevention is key when it comes to minimizing the risk of ransomware breach.
Experts advise keeping your systems up to date and being constantly aware of your system’s vulnerabilities. Also, working with professionals to boost your defenses is always a great plus, especially when dealing with potent threats like Qilin.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

