Russian NoName Bites Into Germany Again
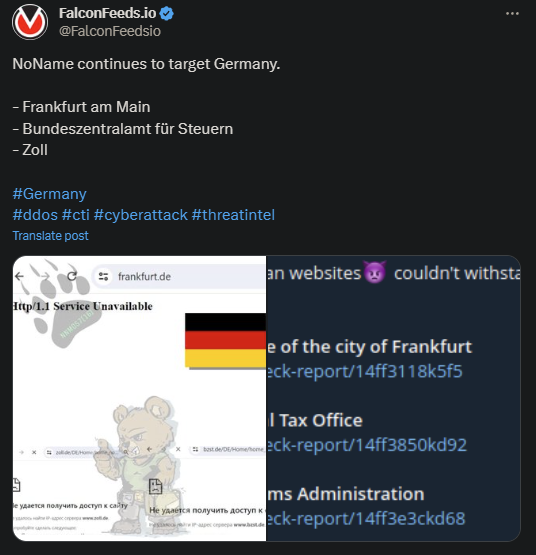
NoName turned its attention towards Germany again, this time breaching 3. The victims are Frankfurt am Main, Bundeszentralamt fur Steuern, and Zoll.
- These were DDoS attacks, aiming to disrupt the victims’ systems, paralyze their operations, and cause as much financial and logistical damage as possible
- They were also meant to make a political and ideological statement, as is most typically the case with NoName operations
- The cybercriminal actor is a well-known pro-Russian hacktivist group with deep Russian ties and interests
- The victims’ websites were rendered inaccessible as a result of the attacks
NoName took responsibility for the attacks on their public Telegram channel, boasting about the results. It is reported that the websites were restored relatively shortly after the attack.
However, the fact that NoName hit public institutions exclusively this time is a statement in and of itself. As stated by the organization itself, the attack aims to push pro-Russian ideas and punish those the group deems enemies of the Russian state.
Generally, NoName tends to hit both public institutions and private entities if they see them as either opposing Russia or supporting Ukraine. This time around, the organization’s targets were strictly in the public domain.
This supports the idea that NoName aimed to make a clear statement about Germany’s involvement in the Ruso-Ukrainian war. Germany has been providing significant military and humanitarian aid to Ukraine during the ongoing conflict.
What Does NoName Stand For?
NoName first came public in March of 2022, shortly after the beginning of Russia’s invasion of Ukraine. The organization immediately pledged allegiance to Russia and hit the public sphere with a non-ambiguous post.
The post stated that their purpose is to attack Ukraine and all those who support “the neo-Nazi regime of Zelensky.” Shortly after the post, NoName conducted its first attacks against the Ukrainian government.
The goal was to cause as much financial and logistical damage as possible to impact Ukraine’s ability to resist the Russian will. These attacks were quickly followed by targeted operations against Ukraine’s supporters, including the US.
The recent attacks against Germany fall in the same category.
Aside from direct DDoS attacks, NoName also resorts to intimidation, as evident especially within the first year of activity. Ukrainian media employees reported receiving threatening letters meant to either intimidate or blackmail.
These tactics make NoName highly feared in the cybercriminal world. Especially given that the organization is often known to work with other hacktivist groups like Killnet and XakNet to conduct more extensive operations.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

