Infamous Snatch Attacks 2 Institutions with History
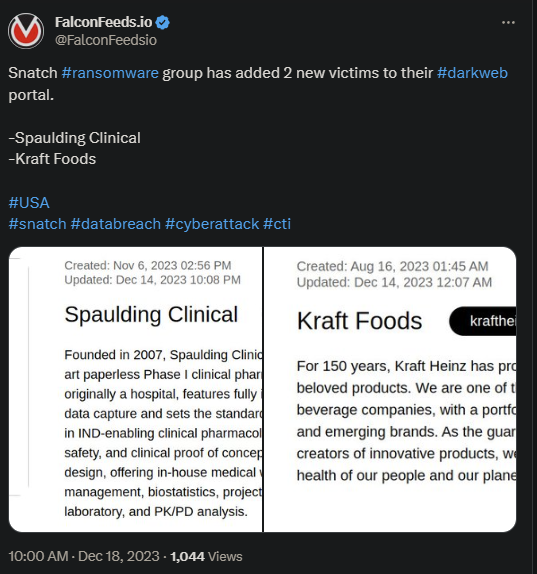
Snatch ransomware took responsibility for the latest attacks on 2 high-profile American companies. Spaulding Clinical and Kraft Foods are the victims, but it is unclear how much damage they sustained.
- Spaulding Clinical was founded in 2007 and quickly became a recognizable name in clinical pharmacology, biostatistics, and clinical data management
- Kraft Foods has 150 years of experience in the field, currently ranking as one of the largest food and beverage names in the world
- The recent attacks resulted in significant data leak and data encryption, which is consistent with a ransomware intrusion
- Snatch shares name similarities with another Snatch group that dates back to 2018
Snatch is a controversial hacktivist group that came under fire recently for what appeared to be internal problems. According to a hacker watcher actor, Snatch leaked critical information about its users and internal operations.
It’s unclear if the leak came from inside or was the result of an outside attack. Soon, the FBI and CISA (Cybersecurity and Infrastructure Security Administration) came online to dig into the findings.
The organization’s name also causes confusion, as another with the same name existed back in 2018. However, it seems like there’s no connection between the 2018 Snatch and the 2023 version in use today.
Who Operates Snatch?
Extensive reports identified Snatch as former Team Truniger. The name belongs to the organization’s founder who built and operated the group. The FBI reports have identified Truniger as the one who worked with GandCrab, another high-profile hacking group.
GandCrab dissolved in 2019, but not before extorting numerous victims of no less than $2 billion over a relatively short period of time. This sheds light on Snatch’s capabilities and potential and explains why so many victims were caught by surprise.
The method of attack is relatively simple, yet quite ingenuous. Snatch relies on several variants to carry its attacks, with the most notable one relying on rebooting the operating system.
This allows the intruder to circumvent the system’s antivirus, along with any endpoint protection variable. The program will then encrypt vulnerable files and extort the victim into paying the ransom to regain access to the system.
If the victim refuses, Snatch publishes the data publicly or sells it to the highest bidder. This, combined with the group’s effectiveness and ingenuity, allowed Snatch to thrive, despite the recent data leak.
The most recent reports show that Snatch members are aware of their vulnerability and data leak and are trying to correct them.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

