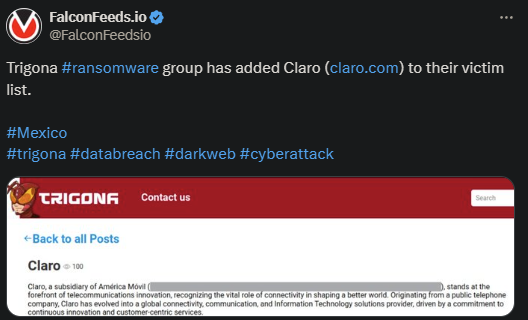
Trigona Ransomware Attacks Mexico-Based Company
Trigona announced a new victim, Claro, a telecommunications company located in Mexico. The target company is a global Information Technology provider with a high-value profile and worldwide customers.
- Trigona’s OP doesn’t detail much about the event, aside from some raw information about the victim
- Claro representatives haven’t commented on the incident, so it’s unclear what they’ve decided to do
- Trigona advertises itself as a highly profitable organization, with up to 50% of its breaches resulting in paid ransoms
- The cybercriminal gang is highly controversial, with some suggesting it doesn’t even exist
Trigona was first observed publicly in October of 2022, but evidence of its activity can be traced back to June of the same year. Unlike standard ransomware actors, Trigona doesn’t necessarily breach the targets on its own.
Rather, it has been reported that the hackers get their victims from RAMP (Russian Anonymous Marketplace.) This is a Dark Web platform where hackers post compromised credentials that others can use to breach the victims.
This tactic minimizes Trigona’s cybernetic presence, as they don’t need to use their own tools to breach the victim. It also explains why Trigona hasn’t been targeted by law enforcement agencies so far. The gang is very tactical and stealthy.
When it comes to the actor’s actual identity and inception, the information is both insufficient and contradictory. Some suggest that Trigona is just a mock-up with no real substance to qualify as an actual cybercriminal group.
Who Is Trigona?
Trigona’s actual identity is unknown, but theories abound. Links have been found between Trigona and several ransomware groups, like Crylock and BlackCat (ALPHV.) This is due to the similarities between codes, tactics, tools, and techniques used.
The strongest connection was found between Trigona and Crylock, as both gangs appear to use similar strategies and tools to perform their attacks. When it comes to BlackCat, the suggestion is that the two organizations often collaborate with each other.
What does this mean? Some specialists suggest that Trigona may not even be a legitimate ransomware actor but rather a patsy. As the theory goes, Trigona is nothing more than a mock-up actor that other ransomware gangs use as a cover-up.
This is a very useful tactic if for gangs being targeted by law enforcement agencies, as it allows them to function undetected. That being said, this theory hasn’t been confirmed.
When it comes to an actual ransomware profile, Trigona sticks to the standard double-extortion technique. The hackers encrypt the victim’s files, steal the target data, and leave instructions to teach the victim how to contact them for negotiations.
If negotiations fail, the Trigona hackers will leak the victim’s data publicly, which can carry serious reputational and financial fallout. Not that the situation is any different if the victim does pay the ransom.
As cybersecurity experts have pointed out, most ransomware gangs publish or sell the leaked data anyway. This will then lead to additional breaches in the future. This is why professionals advise against paying the ransom or even contacting the hackers, to begin with.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

