Russian Hackers Target UK Government Institutions with New DDoS Attacks
The Russian hacker group NoName has targeted today several UK institutions and organizations. The DDoS attacks resulted in the affected websites becoming temporarily unavailable.
- Russian hackers from the NoName group targeted today 4 UK-based organizations and institutions
- Websites of the British Helicopter Association, Waltham Abbey City Council, Geological Society of London, and the London Court of International Arbitration went offline after a series of DDoS attacks
- Access to the affected websites was later restored
- Hackers explained they target organizations and businesses with a pro-Ukraine stance
- Latest attacks are part of a multi-week long campaign against various European organizations
- Attacks are expected to continue
The Russian hacker group NoName has today targeted several UK-based organizations and institutions. The targeted organisations’ experienced temporary outages today after the targeted attacked them with DDoS attacks.
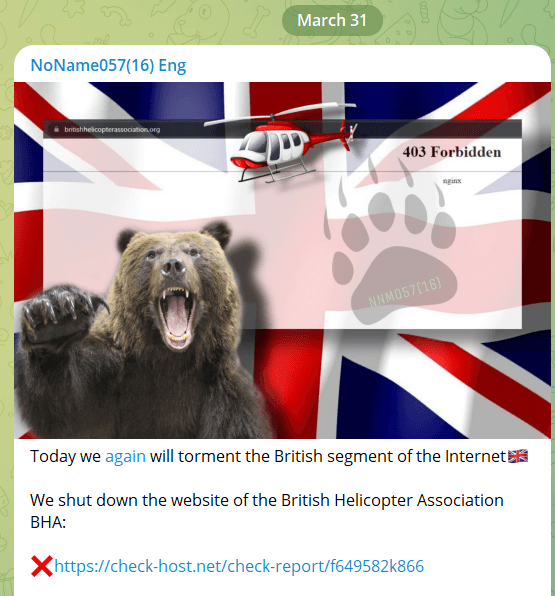
Earlier on March 31, the hacker group NoName announced on Telegram that it had successfully DDoS’ed the portal of the British Helicopter Association. The website was temporarily unavailable on March 31 but restored later.
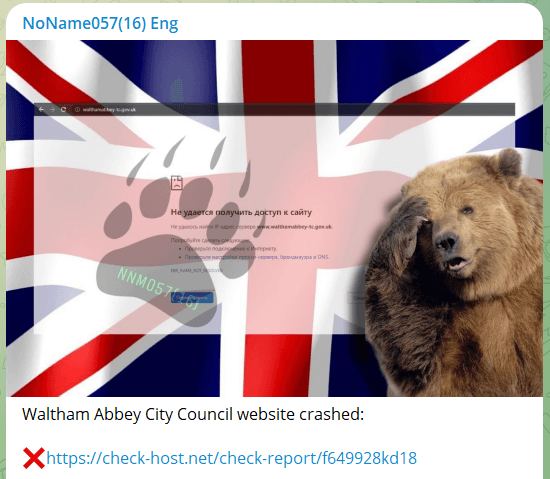
The second and third targets were the portals of Waltham Abbey City Council and the Geological Society of London. Likewise, these websites temporarily went offline until access was restored again.
Then, later on March 31, the London Court of International Arbitration website went offline after the Russian hackers targeted it with a new DDoS attack. At the time of the writing of this article, the website is still inaccessible.
This series of attacks follow the attack on March 29 against the website of the Liverpool City Council. Like in these new cases, the website of the Liverpool City Council became temporarily inaccessible until access was restored.
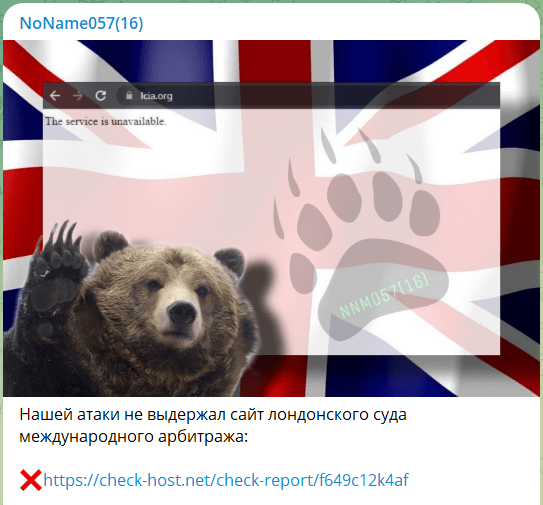
In all these cases, the Russian cybercriminals announced their attacks on Telegram. They provided screenshots and a description of the attack and their motives.
Multiple attacks carried out recently
The hackers commented that they specifically seek to target organizations and institutions of countries with pro-Ukraine foreign policy, especially those who have in the past provided material support to Ukraine.
On March 28, the Russian hacker group revealed that it had DDoS’ed German weapons manufacturer Rheinmetall, a company that recently announced future plans to open a tank factory in Ukraine.
This was preceded by an attack against the website of the French National Assembly on March 27. The week before, the hackers targeted various banking institutions from Estonia and Italy.
In all these cases, these attacks make the targeted websites temporarily inaccessible. Usually, the downtime lasts between 1 to 6 hours.
While not very severe, these attacks may hinder citizens’ access to key government and banking-related services.
It is not known if the Russian hackers are acting independently or operating under a Russian state body or intelligence services.
DDoS attacks are relatively not complicated to carry out, meaning that they could also be perpetrated by non-state actors. However, a possible government connection cannot be excluded.
The hacker group was very active in the last two weeks, carrying out neat-daily attacks against multiple organizations and government bodies per day.
As such, it’s very likely that these attacks will continue in the near future.
Our Mission
We believe security online security matters and its our mission to make it a safer place.

