US Healthcare Data Breach Statistics
Healthcare data breaches increased by 2733% between 2009 and 2019 in the United States. The alarming frequency of such attacks has exposed the majority of Americans’ healthcare data.
The origins of healthcare data breaches range from disgruntled employees to state-sponsored hackers. On many occasions, the data is sold on the dark web.
We studied data from a range of reputable sources to find out just how bad the situation is for healthcare data privacy in the USA, and whether things are likely to get better or worse in the coming years.
Among many worrying insights, we found between 2009 and 2019:
- 3,054 data breaches of healthcare records
- 230,954,151 healthcare records lost, stolen, or exposed
- 70% of the US population affected by healthcare data breaches
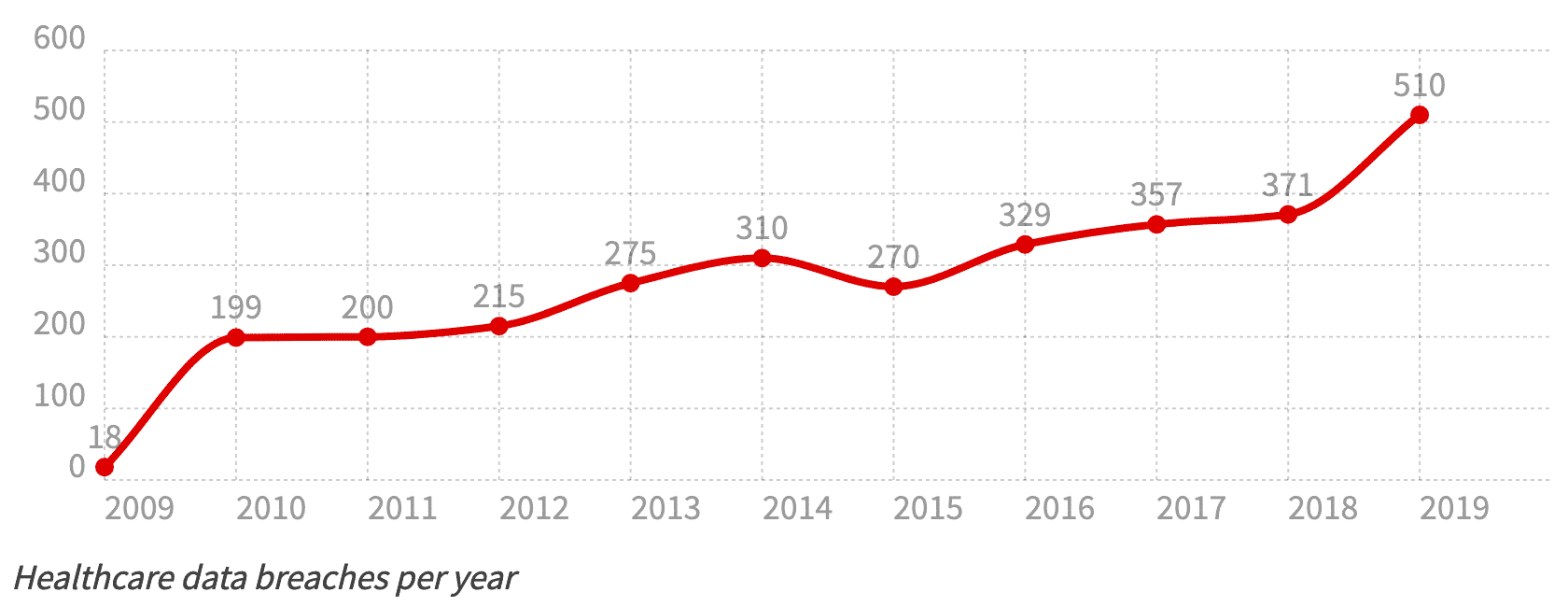
Healthcare Data Breaches by Year
Healthcare data breaches occurred 2733% more frequently in 2019 than in 2009, with an average of 1.4 violations involving at least 500 records per day.
At least 3,054 breaches occurred in the decade. These are known, and reported breaches, and the true figure may be far higher.
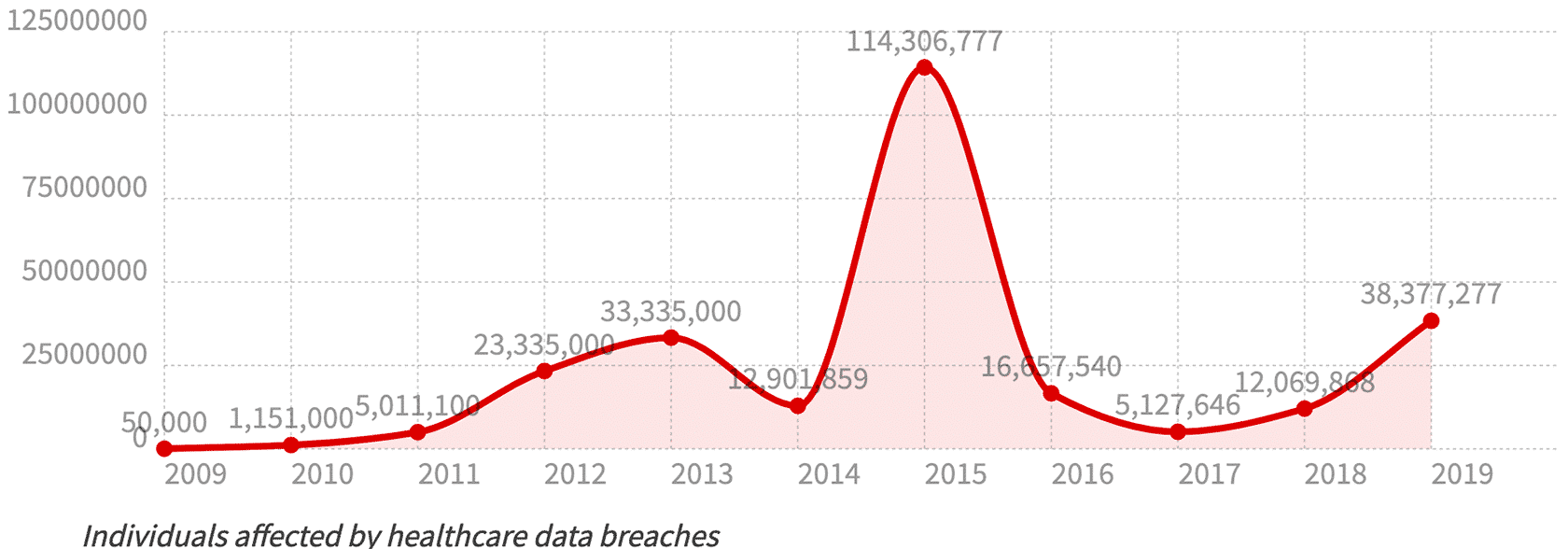
Healthcare Records Exposed by Year
The worst year for an overall number of healthcare records exposed was 2015, despite having fewer total breaches than the two years prior and every subsequent year. This is primarily due to the Anthem Inc. data breach that exposed personally identifiable medical records of 28.8 million people.
2018 and 2019 saw a sharp increase in the number of individuals affected by healthcare data breaches, with a six-fold increase between 2017 and 2019.
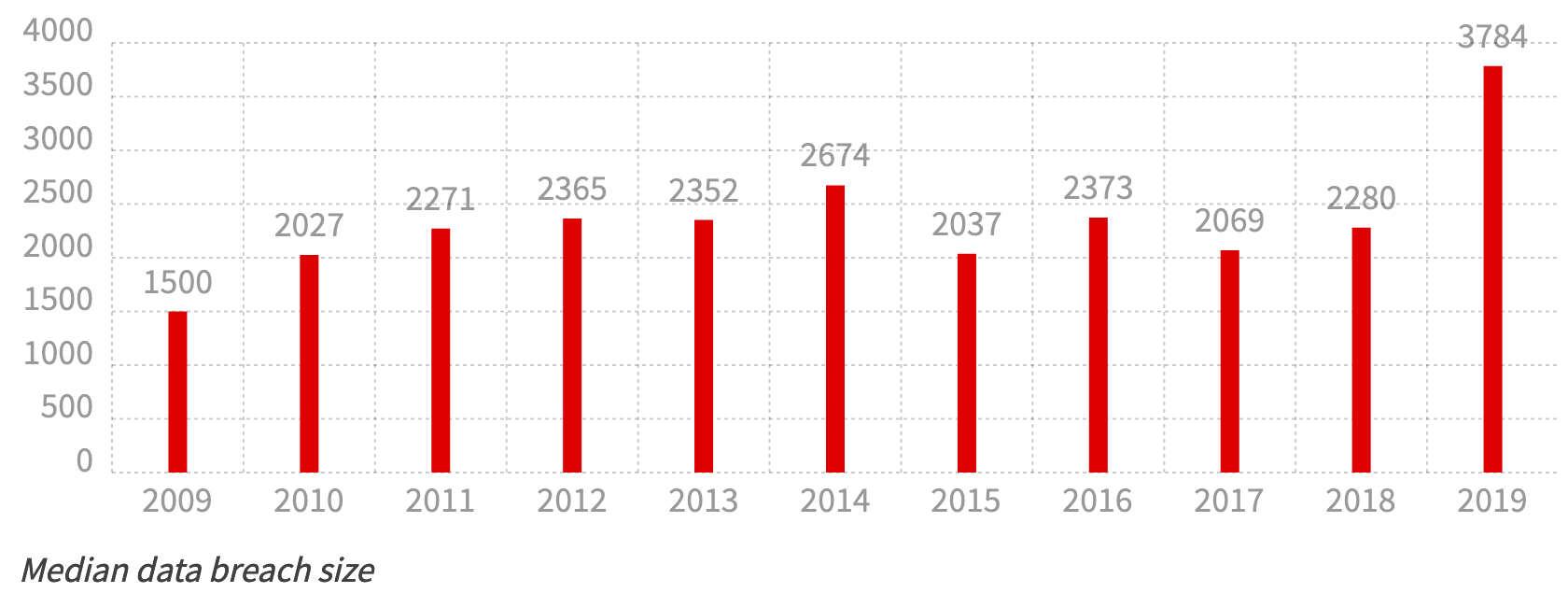
Median Healthcare Data Breach Size by Year
Besides the massive Anthem Inc. breach in 2015, most incidents were below average for the decade. There’s a fairly regular median size of the breach until 2019 when it almost doubles.
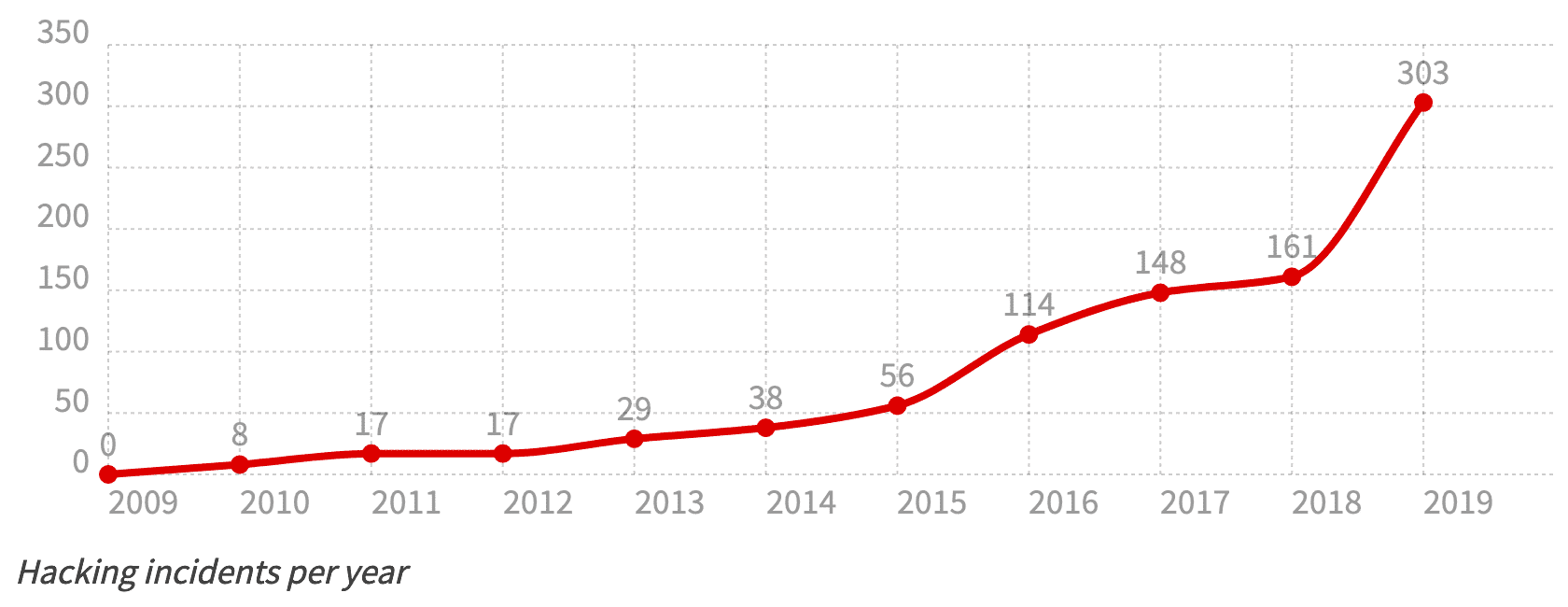
Healthcare Hacking Incidents by Year
Before 2016, there were under 100 breaches each year. Between 2016 and 2018, that number rose dramatically to 423 in three years. 2019 was the worst year, with 303 healthcare data security breaches.
It’s worth noting that while the sophistication of hacks has increased, so has the ability of organizations to identify attacks that may not have even been discovered.
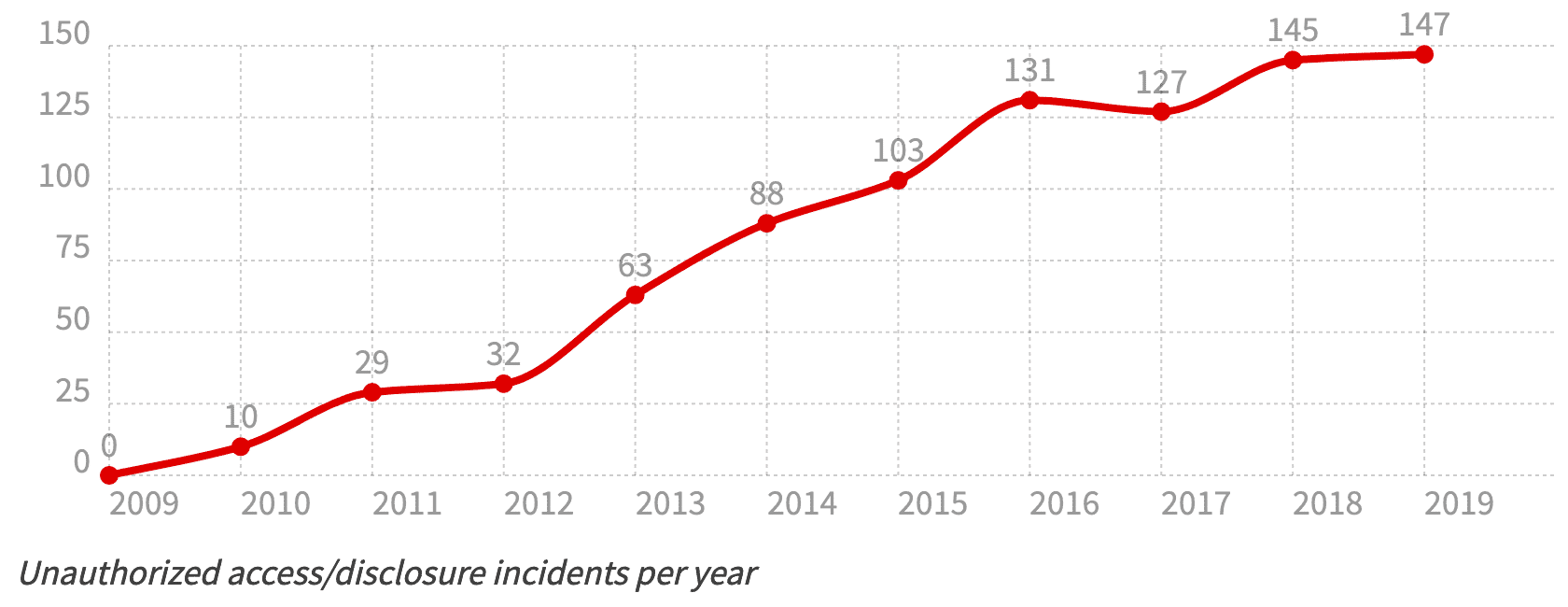
Unauthorized Access/Disclosures by Year
Unauthorized access and disclosures include internal breaches such as employee error or malice. Due to the prevalence of recent data breaches, healthcare organizations have invested heavily in breach-detection, which may explain the sudden increase in reported incident numbers.
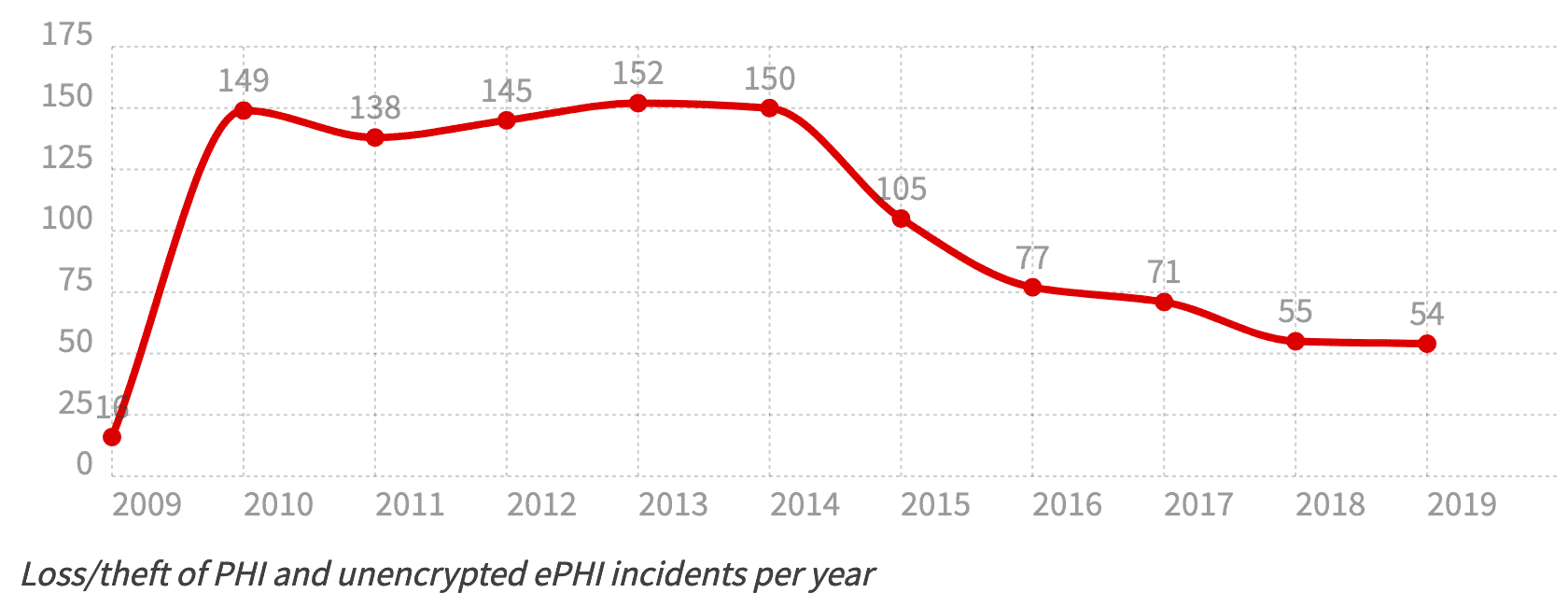
Loss/Theft of PHI and Unencrypted ePHI by Year
One of the most serious incidents resulting from a data breach is the loss of unsecured personally identifiable information. A frequent cause for this is human negligence about cyber security. Many incidents have occurred with the theft of an unencrypted laptop from a vehicle or other publicly accessible location.
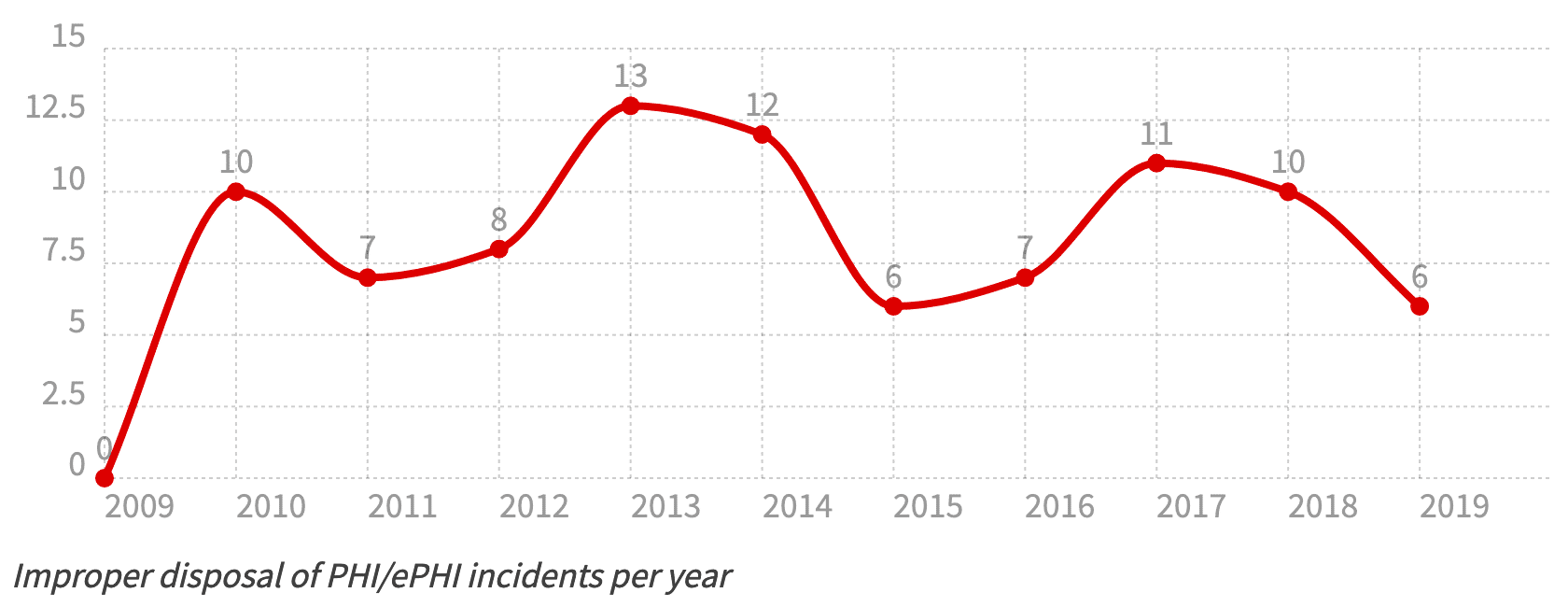
Improper Disposal of PHI/ePHI by Year
Where personal information is concerned, the destruction of storage devices is recommended. Old hard drives must be fully sanitized rather than wiped. When data is no longer needed, it must be carefully disposed of.
Over the past decade, over 1 million personal healthcare records have been leaked due to improper disposal.
Biggest Data Breaches of the Decade
| Rank | Name | Year | Entiry Type | Individuals Affected | Type |
| #1 | Anthem Inc. | 2015 | Health Plan | 78,800,000 | Hacking | #2 | Premera Blue Cross | 2015 | Health Plan | 11,000,000 | Hacking | #3 | Laboratory Corporation of America Holdings dba LabCorp | 2019 | Healthcare Provider | 10,251,784 | Hacking | #4 | Excellus Health Plan, Inc. | 2015 | Health Plan | 10,000,000 | Hacking | #5 | Community Health Systems Professional Services Corporations | 2014 | Healthcare Provider | 6,121,158 | Hacking | #6 | Science Applications International Corporation | 2011 | Business Associate | 4,900,000 | Loss | #7 | University of California, Los Angeles Health | 2015 | Healthcare Provider | 4,500,000 | Hacking | #8 | Community Health Systems Professional Services Corporation | 2014 | Business Associate | 4,500,000 | Theft | #9 | Advocate Health and Hospitals Corporation, d/b/a Advocate Medical Group | 2013 | Healthcare Provider | 4,029,530 | Theft | #10 | Medical Informatics Engineering | 2015 | Business Associate | 3,900,000 | Hacking | #11 | Banner Health | 2016 | Healthcare Provider | 3,620,000 | Hacking | #12 | Newkirk Products, Inc. | 2016 | Business Associate | 3,466,120 | Hacking | #13 | AccuDoc Solutions, Inc. | 2018 | Business Associate | 2,652,537 | Hacking | #14 | 21st Century Oncology | 2016 | Healthcare Provider | 2,213,597 | Hacking | #15 | Xerox State Healthcare, LLC | 2014 | Business Associate | 2,000,000 | Unauthorized Access | #16 | IBM | 2011 | Business Associate | 1,900,000 | Unknown | #17 | Clinical Pathology Laboratories, Inc. | 2019 | Healthcare Provider | 1,733,836 | Hacking | #18 | GRM Information Management Services | 2011 | Business Associate | 1,700,000 | Theft | #19 | Iowa Health System d/b/a UnityPoint Health | 2018 | Business Associate | 1,421,107 | Hacking | #20 | Employees Retirement System of Texas | 2018 | Health Plan | 1,248,263 | Unauthorized Access |
2015 was a big year for big data breaches. Of the 10 biggest healthcare data breaches between 2009 and 2019, five occurred in 2015.
Hacking was the main cause of all the biggest attacks, including the massive 2015 Anthem Inc. attack that led to a breach affecting 78.8 million individuals. The Antham Inc. breach was seven times larger than the second biggest of the decade and bigger than the subsequent nine largest.
Why is healthcare data so frequently targeted?
The data shows that healthcare organizations are extremely vulnerable to cyber-attacks. The amount of personal information held in such databases is problematic for healthcare organizations and the public.
Healthcare providers have steadily increased their cyber security budgets over the past decade; however, many still use outdated and poorly secured computer systems. But why are these organizations so frequently attacked, and is there anything that can be done to protect this data further?
Some common issues that often lead to healthcare information data breaches are:
Outdated systems make them an easy target
Hospitals, in particular, are extremely vulnerable to cyber-attack due to many using outdated computer systems. This means that known vulnerabilities are often left unpatched and systems not updated. Hospital IT teams are often so busy simply keeping systems and databases working correctly that data security becomes a lower priority.
Medical devices connected to the network are often unsecured
Many modern medical devices rely on networking to relay information and work together. Similar to using a smartphone to control your thermostat, hospitals increasingly rely on IoT for improved patient care.
Due to the vast number of connected devices in hospitals, the logistical challenge for IT teams is often too great for proper cyber security maintenance. Add to this that medical devices are not usually built with security baked in, and it’s easy to see why medical devices are often used as an entry point for an attacker to gain access to a healthcare provider’s network.
Data needs to be accessible and shareable, but most staff have no cyber security training
The medical staff needs access to patient data, but the additional training costs and time constraints often mean that the people who access the network most frequently are ill-equipped to keep it secure. When accessing data remotely, staff may be using their own potentially compromised devices. IT only takes one such device to open an attack vector.
You can also find country-specific VPN guides such as our best VPN for New Jersey and our New York VPN guides.
We also have guides on finding a Texas VPN, Nevada VPN, and Florida VPN.
For specific use-cases and unblocking you can check out our Stake VPN guide.
Healthcare data breaches aren't going away
It’s clear to see by the trends over the past decade that the problems surrounding healthcare data will not go away without serious time, training, and money, invested into creating a whole new infrastructure that is ready for frequent patching and leaves less room for human error.
The sheer value of healthcare data is such that without making it exceedingly difficult for attackers to access, they will continue to develop new and increasingly intelligent methods of attack.
Sources: