Avast Says My Router is Infected – Solved
Avast antivirus routine scans may show up ‘your router is infected’ or ‘router is vulnerable’ warning. This warning further elaborates that your DNS has been hijacked and modified.
- Know if your router is infected.
- Fix Avast’s ‘your router is infected/DNS hijack found’ error.
- Enhance your router’s security settings.
Quick Summary
A compromised router or DNS hijacking can be exploited for nefarious purposes. Cybercriminals might intercept your entire network traffic to harvest confidential data. Additionally, they could launch further malware attacks, including those aimed at extortion.
How to Know if Your Router is Infected
At times, the warning from Avast antivirus might be a false positive. If your router is infected or its DNS has been hijacked, you should notice the following tell-a-tale signs.
- A slower internet connection. A router malware infection may cause your internet connection to be painfully slow. This is because your bandwidth will be used for malicious activities such as redirecting traffic to and from various destinations as directed by the malware.
However, a slower internet connection doesn’t necessarily mean your router is infected. Check for other signs below.
- Spoofed familiar sites. Your popular sites may have additions to their URL or behave differently. For instance, you may notice more ads or a lack of the HTTPS certification (no padlock sign in the URL). At times, the sites may be flagged by your antivirus. These unexplained changes may point to router DNS hijacking.
- New unknown software on your devices. Besides spoofed websites, you may also notice unfamiliar apps you didn’t install on your devices. You may get requests to install the software you didn’t even download.
- Unknown device connections on your router. To check for unknown devices, you will need to log into your router. You will then cross-check and review the IP addresses and device connections. You can also use a Wi-Fi network scanner utility for this task.
- Modified DNS settings. By default, your router uses a DNS server provided by your internet service provider (ISP), and these settings are auto-configured. If the settings have changed and the DNS server doesn’t match your ISPs or the one you had changed to, that is a red flag.
- You have no access to your router. Some malware/hackers may not be subtle; once they have infected your router, they will change the router’s credentials. Thus preventing you from doing further checks or changes.
How to Fix the Avast’s ‘your router is infected/DNS hijack found’ Error
If you notice one or more of the above tell-a-tale signs, then the Avast warning isn’t a false positive. Your router has a malware infection, and your DNS has been modified. Proceed as follows to get rid of the virus and DNS hijacking.
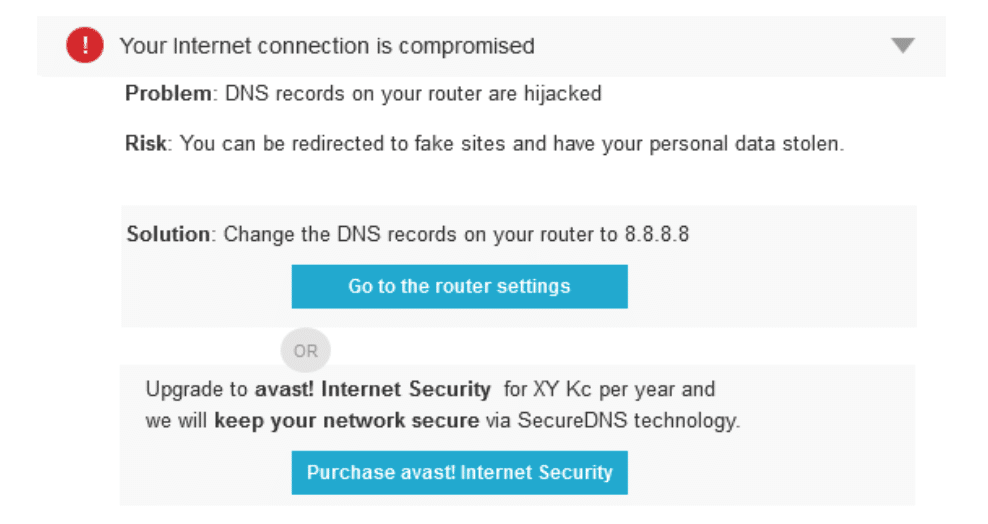
When the Avast Home Network Security tracks down an intrusive virus worming its way through your router, the notification you’ll receive will look something like this:
Factory reset your router.
A factory reset will revert the router to its original system state. It will erase all the data, including your network settings, passwords, and other firmware modifications. Additionally, a factory reset will also get rid of any router malware. Most routers come with a dedicated reset button located in the rear, front, or on one of the sides.
To access the button, you will need a straightened paper clip. In most routers, you will need to press the button for about 10 to 30 seconds for a factory reset. It would help if you did a factory reset while the router is plugged into a power source.
Update your router password
Once your router reboots after the factory reset, you should update your login credentials. They will be changed to default, and you need a strong username and password combination. A strong and unique password will prevent re-infection. You will also need to reconfigure and update your network and Wi-Fi settings.
Use the public DNS on your router.
If you use the “automatic” DNS configuration on your router and still get the Avast warning, change to a public DNS. At times Avast may not recognize the DNS server from your ISP. Some of the best available public DNS include Google and Cloudflare.
Their addresses are as follows. Google primary DNS 8.8.8.8, secondary DNS 8.8.4.4, Cloudflare primary DNS 1.1.1.1, secondary DNS 1.0.0.1
Once you change the DNS configuration on your router, don’t forget to click ‘Save and Apply.’
Tips to Enhance Your Router’s Security
Follow these tips to ensure your Avast router remains secure:
Up to date firmware
Updates patch vulnerabilities, fix bugs and even bring new features. Ensure you update your router’s firmware to the latest version whenever available. Most firmware updates ensure your router’s security will not be compromised by malware and hackers.
You can also opt for custom router firmware such as DD-WRT, Tomato, or OpenWRT. Custom router firmware offers improved functionality, performance, security, and excellent features such as VPN use. However, flashing a custom router firmware voids your warranty.
Change your login credentials
Regularly update your login credentials. They should be unique and strong. This will ensure that no one except you can log into your router.
Change the SSID or network name
SSID or Service Set Identifier is the network name your router broadcasts. It is how you know which Wi-Fi network you are connecting to. To enhance your security, change the default SSID to something different that doesn’t identify you.
Disable WPS and enable WPA2 or WPA3
WPS lets users bypass the Wi-Fi password and get into your network by using a pin. Usually, the pin is printed on the router. This method is weak as cybercriminals can recover the pin remotely. On the other hand, WPA2/WPA3 offer adequate security and stronger encryptions.
Ensure your router’s firewall is always on
The firewall is your first defense against online threats. It monitors and takes care of your incoming and outgoing traffic.
Turn off remote-based router management
This feature can allow anybody to manage your router from anywhere in the world. This includes cybercriminals.
Use Stealth Mode
This feature enables the router not to respond to probing requests from cybercriminals. The status of open ports is hidden, so your router will be less conspicuous on the open internet. If your router has this feature, enable it for extra security.
Set up an antivirus on your other devices
Unsecured devices are easy targets for malware and cybercriminals. If these devices connect to your network, your router could quickly get infected. Hence, cybercriminals can then use the router to propagate attacks on your other devices.
Wrap Up
A router malware infection can be disastrous. Malware and hackers can access your sensitive information, including financial details and other personally-identifying information. If your Avast antivirus warns you that your router is infected and your DNS is hijacked, you should take precautionary measures.
Although it can be a false positive sometimes, it would be best if you regularly review your router’s security settings.
Sources and references:
1. Imperva – What is DNS Hijacking
2. Lifewire – How to reset and restart a router
3. Tom’s Hardware Forum – How to use “Stealth Mode” on your router
4. Google – How to use a public DNS
Frequently Asked Questions
Some people found answers to these questions helpful
How do I check my router for malware?
The surest way to check your router for malware is through the tell-a-tale signs. This includes a slow internet connection, modified DNS settings, spoofed sites, unknown device connections on your router, and unfamiliar programs on your device. Your antivirus might also notify you – especially when you get redirected to spoofed sites.
Can malware spread through Wi-Fi?
Yes. Wi-Fi networks present lucrative opportunities for malicious people to spread malware. Malware such as Trojan horses, worms, and other viruses can spread via Wi-Fi networks. Unprotected devices are at high risk of getting malware and further propagation.
Can an infected computer infect a router?
Yes. Outdated routers can be vulnerable to malware such as the VPNFilter malware. Also, the router can get infected from the internet. An infected router can pose various threats, such as spreading the malware to other devices.
Will resetting my router mess up my internet?
Yes. A factory reset will wipe out your internet settings, including your Wi-Fi name, password, and other functionalities you had set. On the bright side, resetting your router is one of the best ways to eliminate router malware.
What if my router has been hacked?
If your router has been hacked, your security and privacy will be compromised. The hacker will steal sensitive information, propagate further malware attacks, and even carry out blackmail and social engineering. At the extreme, you might not even access the internet nor login into your router.


1 Comment
jraju
October 28, 2023 4:40 pm
Read your article. Fine. But let me put it this way. one component of avast network inspector does not alert any threats , say no vulnerability. But avast smart scan alerts dns hijacking. How it is possible. Is it a false postitive on smart scan to label dns hijack. I checked with grc.com dns check and it says, excellent, when I change my dns to cloudfare 1.1.1.1. I do not want to change the dns in the router and naturally , device overrides the router dns.
expecting your reply