VPN with Tails — The Basics You Need to Know
Should you use a VPN with Tails?
Yes – If you pick a privacy-focused VPN and exclusively use that VPN with Tails only and never for any other purpose whatsoever.
No – If you use your Tails VPN on other occasions, such as unblocking streaming sites on your regular OS.
In other words, you need a dedicated VPN that you use for Tails exclusively.
If you use a VPN with Tails but then also use that VPN for your regular internet activity on your regular OS (where you are logged into Gmail, etc.), then you can potentially negate the privacy enhancements Tails offers to you.
I personally recommend getting a fresh ExpressVPN account registered with a disposable email address you haven’t used elsewhere.
You should preferably register this account from a clean device or OS install, or if you want to go even further, while being behind to another VPN connection. You can also pay with cryptocurrencies bought either from a local seller or a local cash-only ATM.
And finally, you should get a special VPN router on which you can install your VPN and then exclusively use that router when you use Tails. This is because most VPNs do not natively run on Tails OS directly.
Related: How to install Tails on a USB
In this article, you will learn about:
- How Tails operates and what it’s used for
- How a VPN operates and what it’s used for
- Why sometimes it’s not recommended to use a VPN with tails
- How to safely use a VPN with Tails (important section!)
Short article summary and 2024 update:
Using a VPN with Tails can enhance your privacy and security, but it’s crucial to use a dedicated VPN exclusively for Tails.
Combining a VPN with your regular internet activity on your usual operating system can undermine the privacy benefits offered by Tails.
It is advisable to use a fresh VPN account, such as ExpressVPN, registered with a disposable email address, and installed on a specialized VPN router dedicated to Tails.
Tails is a Debian-based Linux operating system designed to preserve privacy and anonymity by routing all internet traffic through Tor.
While the Tails organization does not recommend using VPNs as a replacement for Tor, there are certain scenarios where using a VPN with Tails may be beneficial.
However, significant modifications are required to make a VPN work with Tails, and there are various pros and cons to different methods, such as VPN over Tor and Tor over VPN.
You can jump quickly to the relevant sections by using the menu on the right (desktop) or the one a bit further down (mobile).
Introduction to Tails and Tor
The Amnesic Incognito Live System, known as Tails, is a Debian-based Linux operating system whose ultimate goal is to preserve your privacy and anonymity. To achieve this, Tails forces all your internet traffic to route through Tor — software that lets you browse the internet anonymously. Tails are also equipped with an instant messaging client, an email client, and an office suite, all pre-configured with security.
Tails are simple and easy to use, even if you’re a novice user. With Tails OS, you can prevent third-party applications from tracking your online activities.
To learn more about Tails or Tor, follow either of these links:
- Tails Operating System – https://tails.boum.org/index.en.html
- Tor Browser – https://www.torproject.org/
We assume you have some working knowledge about VPNs. So in this guide, we’ll focus on how to use VPN with Tails to keep you secure.
Advantages of Using Tails
- Skip setup. As Tails is pre-configured to route all your network traffic through Tor, no setup is required.
- Secure your PC.
- Protect your privacy and browsing history when using someone else’s machine.
- Leave no trace of visited websites, entered passwords, opened files, and many more.
- Save chosen files and configurations to persistent encrypted storage.
- Access various software to communicate sensitive information safely.
- Avoid mistakes. Tails will block applications that try to connect to the internet without Tor, encrypt persistent storage, and delete all memory at shutdown
Pros and Cons of Using VPNs with Tails
The Tails organization doesn’t recommend using VPNs as a replacement for Tor, as their goals are incompatible. However, certain use cases might warrant using a VPN with Tails for even greater benefits.
To experience the best of both technologies, significant modifications would have to be made to get VPN to work with Tails.
There are two primary ways to VPN with the Tails operating system.
1. Tails → Tor → VPN (VPN over Tor)
This method adds a VPN hop after the Tor network’s end.
- It enables access to services and features you could otherwise get only through a VPN.
- You can access services and websites Tor would otherwise block.
There are many disadvantages, too, when using a VPN connection after Tor.
- You have access to no Tor-hidden services.
- If the Tor network gets compromised, your real IP address will be leaked.
- If third parties or other providers want to flush you out, they’ll only have to focus on breaking the VPN, not the whole Tor network.
2. Tails → VPN → Tor (Tor over VPN)
Here, the VPN connection is established before connecting to Tor. This method offers many benefits.
- You can use Tails at airports.
- VPNs can help access Tor on censored networks.
- This enables customers to connect when Tails is unusable to their internet service providers (ISPs) or when ISPs have blocked the use of the Tor Browser.
- The Tor network treats your traffic as originating from an anonymous VPN service.
- If Tor gets compromised, you’ll still have a staunch defender in the form of the VPN server protecting you.
Despite the benefits of using a VPN connection before the Tor network, there are still some reasons why using a VPN isn’t recommended.
- If the VPN network is compromised, your data could potentially be exposed to third parties.
- The best VPNs are services you must subscribe to and pay for.
- VPNs may introduce a permanent entry guard if they’re set up before the Tor network.
We recommend ExpressVPN if you want to use a Tails VPN. But keep in mind to get a new clean account and never use it for anything else other than your Tails activity.
Using Anonymous OpenVPN with Tails
Anonymous VPN offers security services for many platforms, including Windows, Linux, and macOS.
Prerequisites
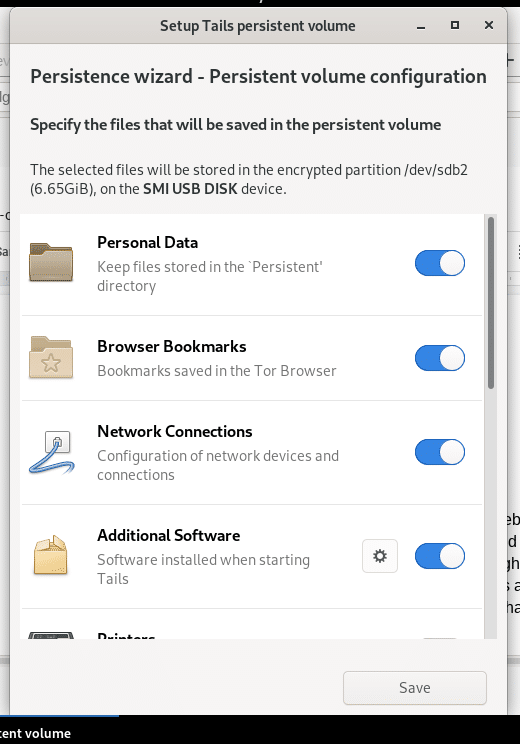
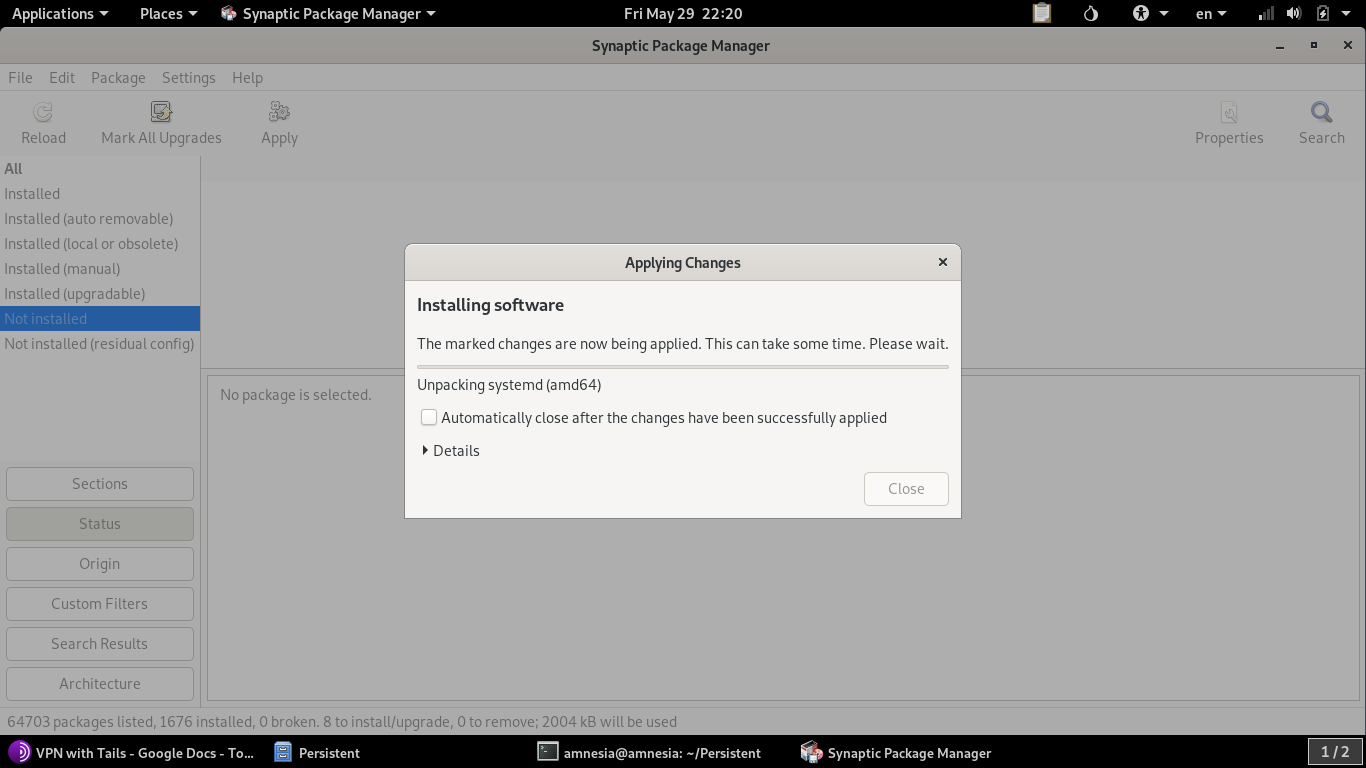
Unlock and configure Persistent Storage.
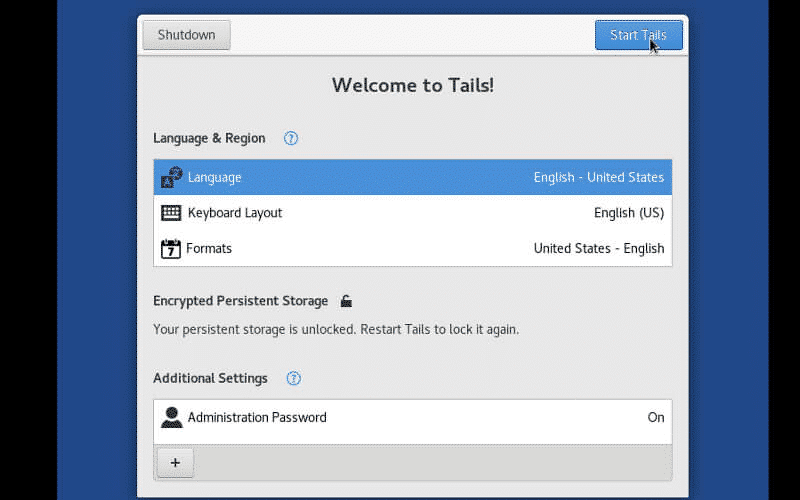
- Unlock persistent storage at the Welcome page by adding a passphrase.
- Add the VPN application you’ll download later to the persistent storage.
Set an administrator password.
- Find the administration password option under “Additional Settings” by clicking the “+” button.
- Set and confirm the password; you’ll be prompted to enter this in the terminal for many operations.
Configure your internet connection.
Steps
Method 1
- Purchase a VPN.
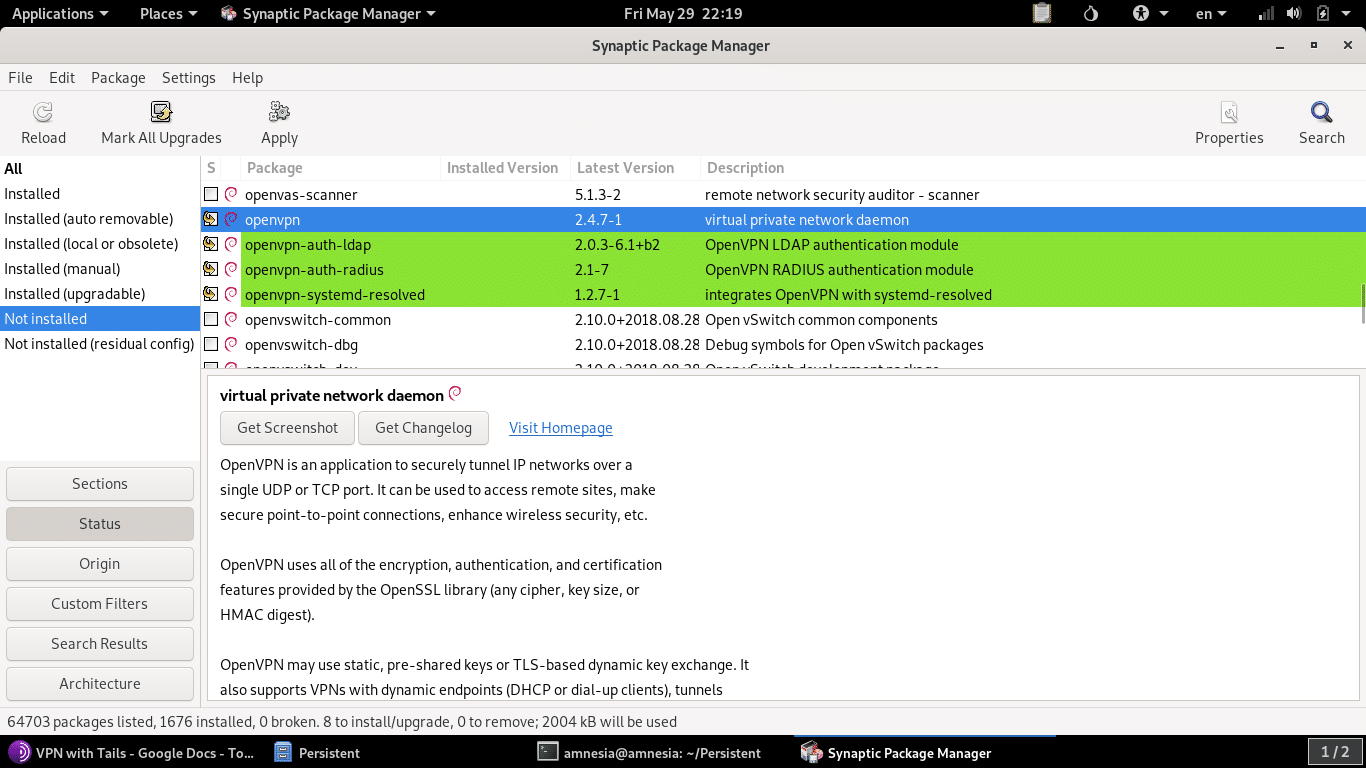
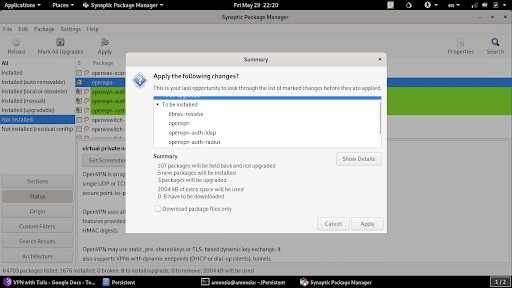
- Download and install a Dedicated VPN.
- After installation is complete, download the Dedicated VPN keys.
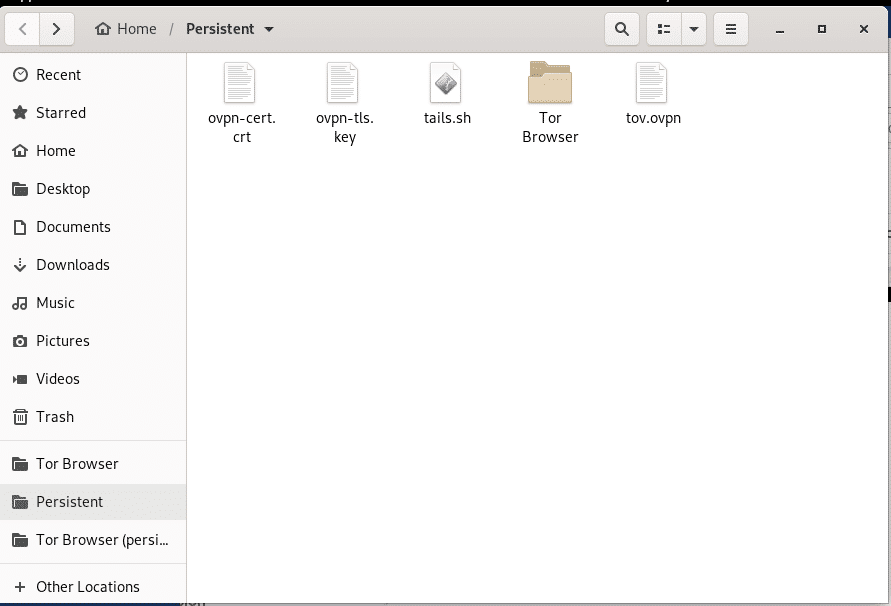
- Rename DeicatedVPN**.ovpn as tov.ovpn and copy them to the persistent storage.
- Download a script to connect OpenVPN in Tails and copy it to your persistent storage as tails.sh.
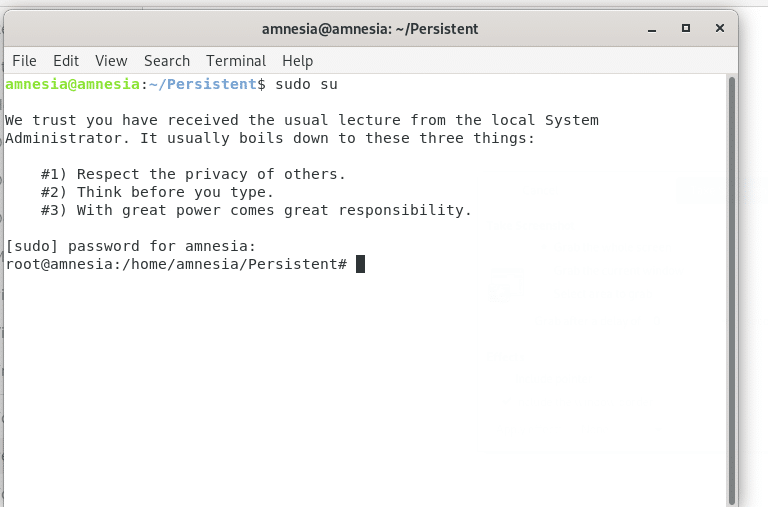
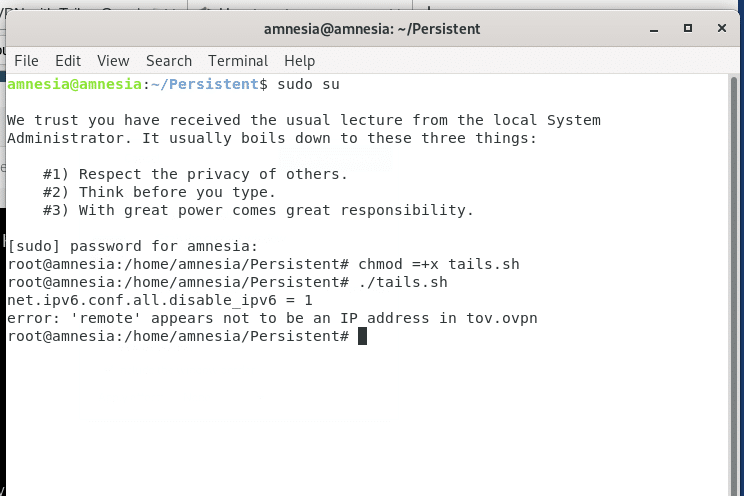
- Open a terminal where these files are located (Persistent Storage) or navigate to the folder where these files will be located after opening the terminal.
- Switch to root.
- Enter the command chmod +x tails.sh to set the execution rights.
- Run the tails.sh script file with ./tails.sh
- Enter your username and password to authorize the VPN connection.
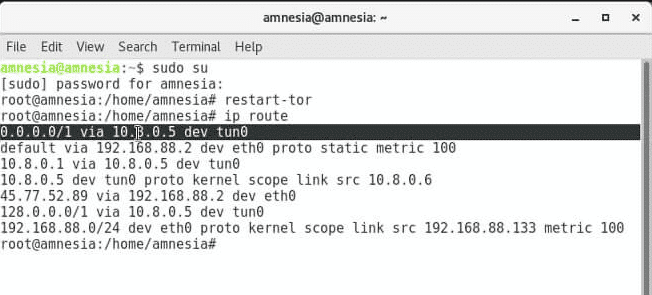
- Upon successful completion, restart Tor and ensure it works by entering the relevant commands.
Method 2
VPN Service Providers and Tails
| VPN Service | Services to Tails |
| ExpressVPN | Works if installed on a VPN router. VPN settings and configurations not fully tested with the Tails OS, so ExpressVPN can’t yet be installed in Tails. Since Tails is a Linux-based OS, you may refer to our manual setup link below using PPTP on Ubuntu, though this isn’t guaranteed to work. |
| PureVPN | Not tested with Tails; therefore, not guaranteed to work. |
| NordVPN | Incompatible, as Tails doesn’t support the use of VPNs directly. |
| OpenVPN/Anonymous OpenVPN | Not directly supported, but can be set up with a few workarounds. |
Is Using VPN With Tails as Bad as They Say?
The Tails VPN Support page insists that combining Tails and VPNs is bad.
Moreover, replacing Tor with a VPN is a bad idea as well. As shown earlier, setting up a VPN isn’t too straightforward. If you’re inexperienced, it’s easy to make mistakes during the process.
Disabling Tor is a bad idea, but VPNs aren’t intrinsically bad or lacking in security, as an official statement on the Tails VPN Support page suggests.
Example
If you use Bitcoins to purchase a subscription to a reliable VPN, then the level of security you get is at least on par with that of Tor.
Data packets go from the computer to the VPN and then to the Tor network by a permanent entry guard, which creates an endpoint server to receive data before reaching the Tor network.
The connection is encrypted by the VPN. Therefore, there’s little difference between a permanent entry guard and a direct connection from the computer to the Tor network.
The attacker must bypass the VPN’s security if Tor or Tor exit nodes are compromised. This is much safer than accessing Tor directly.
Almost no VPN providers work directly with Tails. But it’s possible to overcome this with a VPN router.
Risks of Using VPN Over Tor Network
Use VPN with Tails or a Tor network only when necessary, as this may weaken your anonymity and cause other problems if not configured properly. When considering a VPN, definitely consider the use cases previously discussed.
Circuit Switching isn’t supported when using a VPN over the Tor network.
Internet traffic goes through different exit relays when using a Tor network. This means network requests have different paths or addresses to access the internet.
If your Tor network gets compromised, third parties will find what you requested and from where. However, using a VPN introduces a permanent exit node for internet traffic, allowing others to identify your data’s location.
The anonymity of the network built with a VPN over Tor greatly depends on the VPN’s anonymity.
People prefer to use Tails because of its anonymity and because it doesn’t trust the services of other applications in securing user privacy.
However, if you think adding one more hop with a VPN to the process of what Tails does will increase your safety, you’d be mistaken.
The purpose of using Tails is wasted if your VPN provider sells you out. Make sure the VPN you choose is reliable and trustworthy.
Use a VPN over the Tor network only when necessary.
When using a VPN service over Tor, two instances are established in your machine: one will let you route VPN over Tor, and the other will use Tails normally with Tor.
It might be inconvenient to go through CAPTCHA so often, but you should always use the VPN instance only when you absolutely must. Some websites may also block VPN users as well.
And if you’re new to VPN and Tails, aside from the recommendations outlined here, it’s still a good idea to go through all documentation carefully.
Conclusion
Tails with Tor Browser might answer many of your security and private browsing concerns. Although there’s no consensus about whether it’s a good idea to use Tails with a VPN, the combination may be extremely helpful when used correctly.
If you want to track your traffic or eavesdrop on your online conversations, setting up the Tails OS to go through the VPN and then to the Tor Network will cut off all access routes to you.
This setup will give you peace of mind and keep you out of harm’s way permanently.



25 Comments
Opsecbully
December 27, 2023 10:57 pm
You must be a troll, tails isnt running on HDD but usd drive, and only using ram memory “amnesia”
Opsecbully
December 27, 2023 10:58 pm
usb*
STP
December 18, 2023 10:29 pm
To amnesia —>> Got root ^^
Good point
STP
December 16, 2023 7:38 pm
Thank you for your guide, but sorry lost in at “Download a script to connect OpenVPN in Tails and copy it to your persistent storage as tails.sh.”
Probably too stupid, but where to d/l it from?
George
October 13, 2023 7:39 pm
hello
Any updates regarding the OVPN file? Is this the file that needs to be uploaded?
Frank?
Ghost
May 16, 2023 5:35 am
Hello. I am somewhat familiar with this field. However I’m having an issue launching Tails on my HP laptop. Please help, thanks.
Tom
March 11, 2023 7:09 am
Has anyone gotten the feature Frank spoke of working?
Frank
September 21, 2023 4:11 am
Hi Tom,
Just lucking at the new Tails website (tails.net), it mentioned that incorporating VPN functionality is something they will work on in the future.
Anonymous
February 26, 2023 6:33 pm
Tails does not work with VPNs.
Asdrubale
September 18, 2022 10:45 pm
Dear all
What about
1) trustful Linux OS —>VPN —> Tail over VM (ISO booting) —> TOR ?
Regards
Frank
November 4, 2022 4:14 pm
From what I have read, you do not want to run Tails inside a VM
Anonymous
April 8, 2023 6:14 pm
but inside a windows VM, which is way to different that a Linux VM, can’t compare both techs, is hard to hack your linux system using a VPN, than hack your system using windows + vpn, From there you start
Brad Kehler
September 22, 2021 6:46 pm
Very interesting article that covers a lot of the finer practical points when considering using a VPN with Tails and Tor. Thank you for taking the time to cover this material.
Klaus
July 21, 2019 2:51 am
What if you use tor bridges or Tails>VPN>TOR>VPN/SOCKS5? Would this be possible?
I need to access the clearnet from an IP in my city but cannot connect my ID to it, hows this possible through Tails? How can I “choose” my IP in Tails?
The way I’m thinking is how I mentioned above, with a paid socks5 at the end and a paid VPN before TOR, all acquired anon w BTC
Merci Mult
Miklos Zoltan
July 7, 2021 6:04 pm
Close enough.
The thing with Tails is that most VPN apps won’t run on it, so you need to put a VPN before Tails.
Like this:
VPN -> Tails -> TOR
The most efficient way is to use a VPN router (VPN account paid with crypto, etc). I recommend GL.iNet Creta (you can find it on Amazon).
You set up the router with a VPN that has an IP from your city and then only use that router exclusively for Tails and under no circumstance for any other purposes.
Sprinkler Farm
December 2, 2021 4:34 am
I agree with you that the best solution for this use case is to use Tails OS and route traffic through a GL iNet VPN router. However I am having problems implementing this. I purchased a GL iNet router (the Beryl) and I installed Mullvad VPN (using Wireguard).
I tested this by using the unsafe browser and it works as expected.
I log the Beryl into a public Wifi then I log my Tails laptop into the Beryl then I launch the unsafe browser and check the IP. As hoped, this shows the Mullvad server and not my local IP. Success, for the test.
However, I then try to use the Tor browser and it is clear that this Tor traffic is not routing through the VPN. While in tor browser I go to WhatsMyIP and it shows I am using Tor. So this is a problem… I have tried many tweaks but nothing I do seems to get Tor to run through the VPN. Any suggestions ? This would be a perfect solution to an important problem. Thank you for any thoughts or suggestions !
Sprinlker Farm
December 9, 2021 2:37 am
Ok, so I have continued to toy with the GL-iNet router (the Beryl). And I am still unable to get Tor to disappear into the VPN tunnel on the router. The VPN is Mullvad and it works fine for normal traffic (using Unsafe Browser). I asked GL-iNet customer service and they told me that this is just how it works. The my tor is what emerges out of the Mullvad VPN tunnel so that the TOR network IP is what the end website sees. Miklos, are you having success in getting the end websites to see the IP address of the VPN server for the VPN you installed on your Creta ? This will be an ideal solution for many people if it configured such that it does indeed conceal the Tor IP addresses. I’d be grateful for any insights !
Miklos Zoltan
December 24, 2021 12:21 pm
Hey. Sorry for replying so late.
Actually, it works as it’s supposed to and there is no way around it.
Using a VPN router will hide your actual IP before reaching any TOR node.
It’s Your actual IP -> VPN IP -> TOR node(s)
You cannot put the VPN to come AFTER TOR, so that whatever you are accessing is seeing the VPN IP.
Miklos Zoltan
December 24, 2021 12:23 pm
> TOR network IP is what the end website sees.
Yes this is correct and there is no way around it, other than just not using TOR and instead only using a VPN.
This is because of the way TOR itself works.
That being said, this should never be an issue though. You don’t actually need a setup like the one you described.
Your device -> VPN router -> TOR is a perfect setup.
Harry
May 18, 2022 1:26 am
Hi Miklos,
Do you know of a way that someone/or company can set up the same set up that you have?
I have Tails/Tor, but I need to set up the rest of the apparent 100% anonymous solution. I started looking over the GL.inet (Creta) AR750 and you can easily be overwhelmed. Do I need to add the VPN software of my choice? Or does this device come with the software?
Tim.smy
May 20, 2019 6:54 pm
Since you have reinstall everything on each boot what would be simple method in your view. Thankyou. Timothy
Miklos Zoltan
July 7, 2021 6:07 pm
Tails has a persistent storage on which you can store some files that will be available after reboot.
Anonymous
September 12, 2021 9:36 am
see I already bought nord and have tails on a flashdrive, how do I get my vpn to work on it after I reboot the computure and load into tails?
Miklos Zoltan
December 24, 2021 12:25 pm
You will need to buy a VPN router (a special router that loads a VPN configuration – so the VPN works straight on your router).
Tails OS unfortunately isn’t compatible with many VPNs. As in, you can’t install one on Tails.
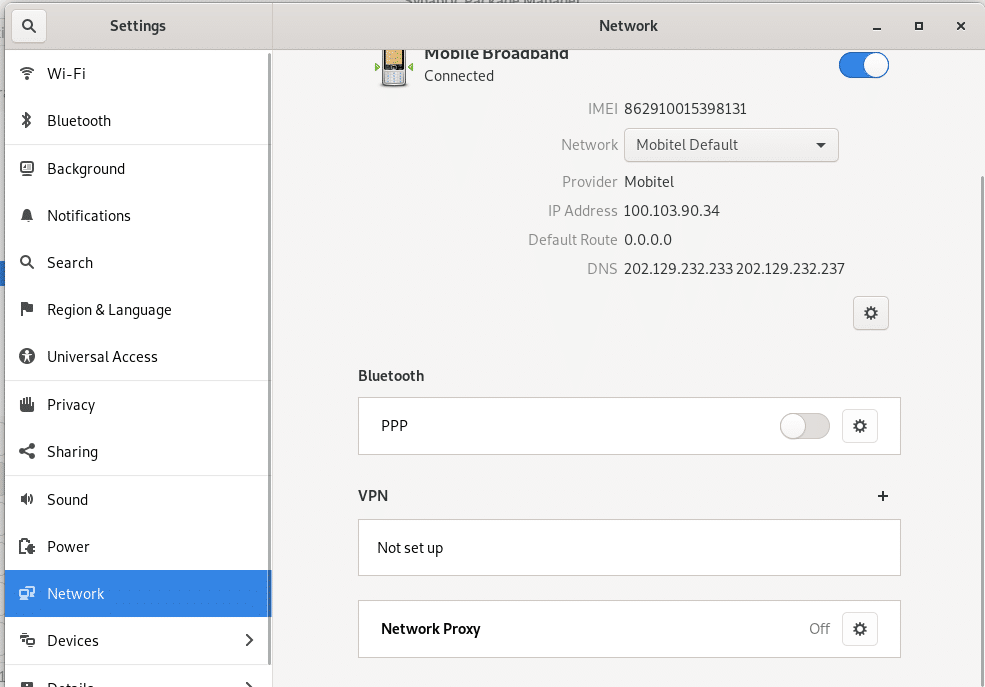
Frank
December 23, 2022 2:01 pm
Hello Miklos,
On Tails 5.8 (current version), if you go into the Settings menu, then click on the Network tab, there is an option to add a VPN! The system prompts the user to “import a VPN file”. The user is then directed to select a Directory, from which they can import the VPN file (presumably an OVPN file?). I thought you should know about this, Thank you.