Proxy vs VPN: Differences and Similarities – Explained
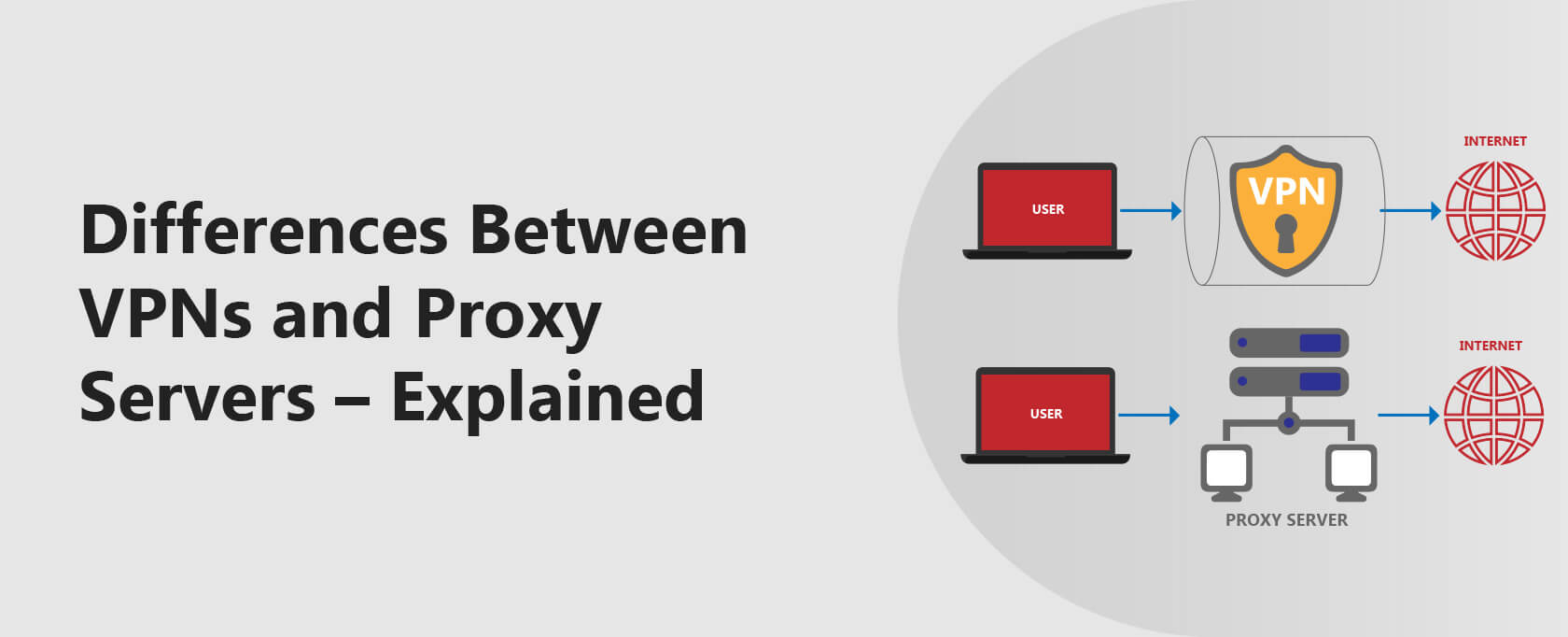
VPNs and proxy servers offer various ways to access the internet privately, protect your identity, and bypass geo-restrictions.
However, a VPN gives you more security and privacy than a proxy server. You can use a VPN or a proxy server, depending on your online tasks.
- What is a VPN, Proxy server, and how do they work?
- How to set up VPNs and Proxy servers
- The differences and similarities between a proxy vs VPN.
- Use cases for VPNs and Proxy servers.
In this ultimate guide, you will learn the differences there’s to know about VPNs and proxy servers.
I explain how VPNs and proxy servers work and how to set them up, providing an in-depth comparison of their features such as encryption, coverage, logging, and reliability.
VPNs offer more comprehensive security and privacy, making them ideal for overall internet protection, while proxy servers are better suited for specific tasks like bypassing geo-restrictions or accessing blocked websites.
For optimal performance and value, I recommend using paid or premium VPNs and proxy servers.
What is a VPN, and How Does it Work?
A VPN or Virtual Private Network secures your connection and hides your IP address over the internet. It does this by tunneling your internet traffic between your device and the internet.
Besides tunneling, the VPN service also encrypts your internet traffic and routes it through a VPN server.
Encryption ensures that no one will know what your internet traffic entails. Hence your online activities are generally safe from sniffers, eavesdroppers, your ISP, and even the government.
When your traffic is routed through the VPN server, the server assigns you a new IP address.
Online entities and services you access will only see the server’s IP address. The server’s IP address masks your actual IP address. This is how the VPN gives you online privacy.
Paid VPN services implement other mechanisms and features to ensure your data is safe, private, and secure.
It’s important to note a VPN provider will only enhance your online privacy if you aren’t simultaneously logged into an online account that knows about your identities, such as Facebook or Gmail.
A VPN in itself does not guarantee online privacy.
What is a Proxy Server, and How Does it Work?
A proxy server is an intermediary that ‘surfs the internet on your behalf. The proxy handles all your needs when you access the internet through the proxy server. It receives your requests and sends them to websites and online services.
It then receives and forwards the results from the websites and online services. The internet services you access will only see the IP address of the proxy server. Hence, the proxy server masks your actual IP address.
Unlike VPNs, most proxy servers don’t encrypt your online traffic.
Let us look at common proxy servers you can use as your daily drivers.
Common types of proxy servers
HTTP Proxy servers
These are the most popular proxy servers. They are used for website traffic and hence gaining access to geo-restricted websites.
SOCKS Proxy servers
These servers can handle any type of traffic besides web traffic. They are popular for online gaming, file sharing, and video streaming. However, they are usually slow and congested.
Transparent Proxy servers
These proxy servers are used to monitor the online activities of connected users. They block access to websites, verify Wi-Fi logins, and even for parental control. They are known as transparent because users don’t know of their existence.
How to Set Up a VPN
Setting up a VPN involves installations and subscriptions. Here are quick steps to set up a VPN on any device.
- Choose a good VPN – subscribe, download, and install it.
- Log in to the VPN and connect to a server of choice.
- Enjoy access to online content.
How to Set up a Proxy Server
Unlike VPNs, you don’t need to install proxy servers. You only configure them. Paid proxy servers will require a subscription.
The proxy provider will give you a proxy IP address, port number, or the proxy auto-config file (.pac file)/ proxy script address. However, some proxy server providers may require that you install an extension.
Here is how to configure proxy servers on various platforms.
This method eliminates the process of setting up the proxy on various applications.
Windows 10
Setting up the proxy using proxy auto-config file .pac:
- Open Settings, go to Network & Internet, then Proxy.
- Under the Automatic proxy setup section
- Toggle the Use Setup Script switch to On.
- Enter the script address.
- Click Save and close settings.
Setting up the proxy using the IP address and port number:
- Open Settings and go to Network & Internet, then Proxy.
- Under the Automatic proxy setup section, toggle the switches off
- Scroll to the Manual proxy setup section and toggle Use a proxy server switch On.
- Type the IP address and port number in their respective fields.
- Click Save and close settings.
Mac
- Choose the Apple menu, go to System Preferences, then click Network.
- Select the network service you are using (Ethernet or Wi-Fi).
- Click Advanced, then click Proxies.
- To configure your proxy server automatically, select Automatic Proxy Configuration, and then enter the PAC file address in the URL field.
- To configure your proxy settings manually, select a relevant proxy server, then type the IP address and port number.
- If the proxy server is password protected, tick the “Proxy server requires password” checkbox. Please enter your username and password in their respective fields.
- Click OK.
Firefox browser
- Click on the Firefox menu > Options.
- Under the General section, scroll to Network Settings and click Settings.
To manually configure the proxy, select Manual proxy configuration.
Choose the type of proxy, then enter the IP address and port number.
For automatic configuration, select Automatic proxy configuration URL, and enter the pac address. - Click OK to save your settings.
To use the proxy on other browsers, use the above platform method.
Android
- Go to Settings > Network & Internet/Connections > Wi-Fi.
- Tap on the cog icon next to your current Wi-Fi network and tap Advanced.
- Tap on the Proxy option and choose the proxy type.
- For manual setup, enter the proxy hostname (IP address) and the port.
- For the pac address, select the Auto-config option
- Tap Save.
iOS
- Open the Settings > Wi-Fi.
- Select the current active Wi-Fi connection.
- Under HTTP proxy, click Configure Proxy.
Tap Manual to enter the hostname (IP address) and port. If the proxy server is password protected, toggle authentication. - To use the Proxy Auto-Config (PAC) file, Tap Automatic.
- Click Save.
Differences Between Proxies and VPNs
Here is a brief overview:
| VPN (Virtual Private Network) | Proxy server | |
| Encryption | Encrypts all your internet connection. | Doesn’t encrypt your internet connection. |
| Coverage | Works with all your internet traffic | Works with web and specific apps’ traffic. |
| Logging | No-log policy (premium VPNs). | Logs your activities. |
| Reliability | More reliable. | Less reliable. |
Let’s take an in-depth look.
Encryption
VPNs secure your internet connection with impeccable encryption while Proxy servers don’t. The VPN encryption ensures that no one will gain access to your online activities and sensitive data – provided you follow common safety practices.
Hence, a VPN protects you from prying eyes such as hackers, your ISP, and even the government – again, provided you follow internet safety practices (such as not using Gmail, Facebook, etc., together with your VPN).
Coverage
VPNs tunnel your internet connection on the operating system level. Any incoming or outgoing connections must pass through the VPN.
Some VPNs also allow you to set which apps or services can use the VPN tunnel. This is via split tunneling.
On the other hand, proxy servers work on the application level. They route web traffic or traffic from certain apps that allow proxy connections.
Logging
Some paid VPNs have a strict no-log policy. They do not store or log any activities you undertake while using the VPN. The no-log policy ensures your data remains private at all times.
Unlike VPNs, many proxy servers keep connection logs and even activity logs.
Reliability
Some paid VPNs offer a more reliable connection than proxy servers. The VPNs also come with features such as kill switch and leak protection.
These features ensure that your privacy and security are not compromised even when the connection drops. Furthermore, VPNs have many servers, and this avoids congestion.
With proxy servers, congestion and server overload may lead to connection problems.
Unblocking
Generally, a web proxy will perform poorly at unblocking geo-restricted content. This is because most websites and apps with such content have long banned most public proxy services.
On the other hand, a premium VPN is very good at unblocking and has a fast connection speed.
But like a free proxy, a free VPN will also not work in most cases of blocked content.
Similarities Between Proxies and VPNs.
Here are how VPNs and proxy servers can be similar:
Slow speeds
VPNs and proxy servers suffer from slow speeds. In VPNs, slow speeds are due to the encryption overhead. In proxy servers, slow speeds are due to the ‘middleman’ and congestion/server overload.
However, this speed decrease is almost undetectable in the case of premium VPNs.
Proxies, on the other hand, are almost always very slow.
Hide IP address
Both VPNs and proxy servers mask your actual IP address. Any internet entity will see the VPN or proxy server IP address.
Bypass geo-restrictions
By masking your IP address, VPNs and proxy servers help you access restricted content. However, a VPN is more reliable in bypassing restrictions than a proxy server.
Use Cases for VPNs
VPNs are suitable for the following tasks:
- When you need to bypass geo-block restrictions (streaming).
- When you want to browse privately and securely.
- When you need to avoid bandwidth throttling from your ISP.
- When you need to gain access to blocked websites.
- When you need to bypass price segmentation.
Advantages of using a VPN
- Encrypts your entire traffic.
- No congestion/ server overload.
- Excellent privacy (premium VPNs)
- No log policy (premium VPNs)
Disadvantages of using a VPN
- Encryption overhead hence slow speeds.
- Pricey subscriptions.
Use Cases for Proxies
Proxies are suitable for the following tasks:
- When you need to gain access to blocked websites.
- When you need to bypass geo-block restrictions (streaming).
- When you want to browse anonymously.
- For content control (transparent proxy servers)
Advantages of using a proxy server
- Increased performance due to caching.
- An excellent content control tool.
- Bypasses restrictions.
Disadvantages of using a proxy server
- Works with app or web traffic.
- No encryption.
- Logs your activities.
Wrap Up
VPNs and Proxy servers are great tools for bypassing restrictions, hiding your IP address, and giving you privacy. However, each tool is best suited for different tasks. In a nutshell, a VPN gives you comprehensive functionality compared to proxy servers.
Lastly, using paid/premium VPNs or proxy servers is advisable. They give excellent value for your money.
Frequently Asked Questions
Some people found answers to these questions helpful
Do you need a proxy if you have a VPN?
No. A paid VPN can offer all the functionality you get from a proxy server. A VPN will also provide other functionalities such as encryption, kill switch, and leak protection, among many others. Additionally, a VPN doesn’t log your online activities.
Which is faster, VPN or proxy?
Although both may slow your internet connection speeds, a VPN has better overall speeds. Besides the encryption overhead, a premium VPN doesn’t suffer from server overloads and congestion.
Can I use VPN and proxy together?
Yes. However, for excellent results, ensure you have a faster internet connection. This is because of the encryption overhead, and the proxy might slow down your speeds. Although you might improve your privacy, you may or not miss other functionalities’ bypassing restrictions. Using a proxy may negate the privacy enhancements your VPN offers.
Is a proxy server the same as a VPN?
No. A proxy server and a VPN are not the same. Nonetheless, they share some functionalities, such as masking your IP address.
Is using a proxy server safe?
A proxy server is not safe in terms of privacy and security. A proxy server doesn’t encrypt your traffic, making it susceptible to prying eyes. Furthermore, proxy servers log your activities and even connection stamps. Others may push ads and malware.